The term “cloud application security” emerged with the increasing adoption of cloud computing, roughly in the mid to late 2000s, as organizations began deploying applications on platforms like AWS, Azure, and GCP. This shift highlighted that traditional on-premises security measures were insufficient for the unique challenges and shared responsibility models of the cloud. The change accelerated as cloud-native architectures, microservices, and containerization became prevalent, demanding specialized security approaches for applications built and running in the cloud.
Cloud application security refers to the practices and technologies implemented to protect software applications deployed, accessed, and operated within cloud computing environments. It addresses the unique security challenges arising from cloud architectures, including shared responsibility, distributed components, and internet accessibility. The goal is to ensure the confidentiality, integrity, and availability of cloud-based applications and their data by mitigating threats throughout their lifecycle.
Why do organizations need cloud application security?
Organizations need robust cloud application security because their critical applications and sensitive data are increasingly hosted in complex, distributed cloud environments. Traditional security measures often fall short in addressing the unique challenges of the cloud, including shared responsibility models, misconfigurations, and the expanded attack surface. Without dedicated cloud application security, organizations risk data breaches, service disruptions, compliance violations, and reputational damage. Proactive security measures ensure the confidentiality, integrity, and availability of cloud-based assets, fostering trust and enabling secure digital transformation.
The right time to look for cloud application security is now, or ideally, before migrating or deploying applications to the cloud. Embedding security from the initial planning and design phases (“shift left”) is far more effective and cost-efficient than bolting it on later. As soon as an organization considers leveraging cloud services for its applications, it must simultaneously consider the specific security controls and strategies required to protect them in that environment. Delaying this can lead to significant vulnerabilities and increased remediation costs down the line.
What are cloud application security best practices?
Securing applications in the cloud is paramount for organizations of all sizes and across all industries. To navigate the complexities of cloud environments and effectively mitigate evolving threats, a set of proven best practices must be diligently implemented. The following outlines 10 essential cloud application security measures that form a robust foundation for protecting your valuable assets and ensuring a resilient security posture in the cloud.
- Implement strong Identity and Access Management (IAM): Weak IAM is a primary attack vector. Limiting access and verifying identities significantly reduces the risk of unauthorized access and lateral movement within the cloud environment.
- Secure your APIs: Unsecured APIs can expose sensitive data and functionalities, making them a prime target for attackers.
- Encrypt data at rest and in transit: Encryption renders data unintelligible to unauthorized parties, mitigating the impact of data breaches.
- Implement robust input validation and output encoding: These practices are fundamental in preventing common web application vulnerabilities that can lead to data compromise and other security issues.
- Regularly perform security testing: Regular testing helps identify and address vulnerabilities before they can be exploited in production. Automation ensures continuous security assessment.
- Implement Network Segmentation and Firewalling: Network segmentation limits the blast radius of a security incident, while firewalls prevent unauthorized access to your applications. WAFs provide specific protection against web application attacks.
- Maintain up-to-date Software and Patch Management: Outdated software is a significant source of vulnerabilities that attackers can easily exploit. Timely patching is essential for maintaining a secure environment.
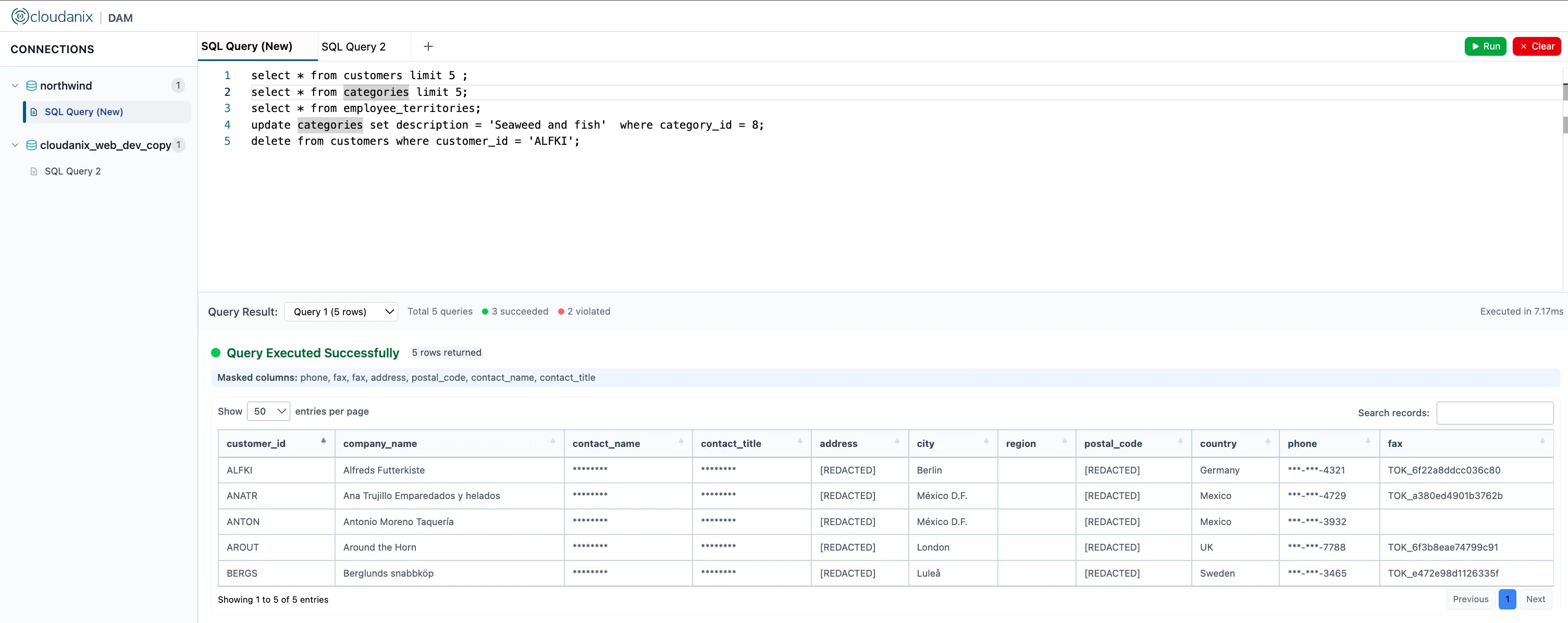
- Implement comprehensive logging and monitoring: Effective logging and monitoring provide visibility into the health and security of your applications, enabling timely detection and response to security incidents.
- Secure your Infrastructure as Code (IaC): Insecure IaC can lead to the deployment of vulnerable cloud infrastructure, undermining the security of your applications.
- Implement a robust incident response plan: Even with the best preventative measures, security incidents can occur. A well-defined incident response plan minimizes the impact and facilitates a swift recovery.
In conclusion, establishing and consistently adhering to these top 10 cloud application security best practices is not merely a recommendation but a necessity in today’s cloud-centric world. By prioritizing strong identity management, securing APIs, encrypting data, and implementing proactive monitoring and incident response, organizations can build a resilient security framework that safeguards their cloud applications and fosters trust with their stakeholders, regardless of their size or industry.
What are the steps and processes involved in cloud application security?
Securing cloud applications is not a one-time task, but rather a comprehensive and iterative process that spans the entire application lifecycle. From the initial blueprint to ongoing operations, each phase presents unique security considerations that demand a structured and proactive approach. Understanding the step-by-step journey of cloud application security is crucial for stakeholders to implement effective controls and build resilient, trustworthy cloud-native solutions.
Here is a step-by-step process outlining how cloud application security is typically approached and implemented:
- Threat modeling: Conduct threat modeling exercises involving security, development, and operations teams to anticipate attack vectors and potential impacts.
- Defining security requirements: Document functional and non-functional security requirements (e.g., authentication mechanisms, encryption standards, access controls, logging requirements).
- Secure architecture design: Choose secure cloud services and configurations, implement the principle of least privilege in architectural components, and design for secure data handling.
- Secure coding practices: Provide security awareness training to developers, establish secure coding standards (e.g., OWASP Top 10), and utilize code review processes.
- Static Application Security Testing (SAST): Integrate SAST tools into the development pipeline to automatically scan code and provide feedback to developers.
- Software Composition Analysis (SCA): Utilize SCA tools to scan dependencies and alert developers about risks, recommending updates or alternative secure libraries.
- Dynamic Application Security Testing (DAST): Integrate DAST tools into the testing phase to probe the application’s interfaces and identify runtime vulnerabilities.
- Penetration testing: Engage ethical hackers to perform thorough security assessments and provide recommendations for improvement.
- Infrastructure as Code (IaC) security: Scan IaC templates for security vulnerabilities and compliance issues before deploying resources.
- Cloud configuration security: Implement least privilege for IAM roles, secure storage buckets, and configure network security groups and firewalls effectively.
- Secrets management: Utilize dedicated secrets management services provided by cloud providers or third-party tools. Avoid hardcoding secrets in the application code or configuration files.
- Web Application Firewall (WAF): Deploy and configure a WAF to inspect incoming requests and block known attack patterns.
- Runtime Application Self-Protection (RASP): Deploy RASP agents that can analyze application behavior and block malicious activities.
- Security logging and monitoring: Implement a robust logging and monitoring system, configure alerts for critical events, and regularly review logs.
- Threat intelligence integration: Integrate threat intelligence data into security monitoring and alerting systems.
- Incident response planning: Document incident response procedures, define roles and responsibilities, and conduct regular drills.
- Vulnerability management: Regularly scan for vulnerabilities, assess their risk, and apply necessary patches or mitigations. Know more about vulnerability management.
This step-by-step process highlights the continuous and multi-faceted nature of cloud application security, emphasizing the need to integrate security throughout the entire application lifecycle.
What are cloud application security threats?
In the dynamic landscape of cloud computing, a critical first step towards robust security is a clear understanding of the prevalent threats targeting cloud applications. Heightened awareness of these potential vulnerabilities empowers stakeholders to proactively implement effective defenses and build resilient cloud environments. This section outlines the top security threats that organizations must recognize and address to safeguard their valuable cloud-based assets.
Here are the top 6 cloud application security threats that organizations should be aware of:
Data Breaches
Unauthorized access, disclosure, or theft of sensitive data stored or processed by cloud applications. This can occur due to weak access controls, misconfigurations, insecure APIs, or vulnerabilities in the application itself.
Insecure APIs
Application Programming Interfaces (APIs) facilitate communication between different software components and services. If not properly secured through robust authentication, authorization, input validation, and rate limiting, they can become entry points for attackers to access sensitive data or functionalities.
Misconfigurations
Errors in setting up or managing cloud resources, such as storage buckets left publicly accessible, overly permissive security group rules, or disabled security features. These are often unintentional but can create significant vulnerabilities.
Account Hijacking
Attackers are gaining control of legitimate user accounts through techniques like phishing, credential stuffing, or exploiting weak passwords. Compromised accounts can be used to access sensitive data, launch further attacks, or disrupt services.
Insider Threats
Security risks originate from within the organization, whether intentional (malicious employees) or unintentional (negligent employees mishandling data or credentials). Insiders often have legitimate access, making their actions harder to detect.
Lack of visibility and control
Difficulty in monitoring and understanding the security posture of cloud applications and infrastructure. This can arise from the complexity of cloud environments, decentralized management, or inadequate security tools and processes.
Understanding these top threats is the first step towards implementing effective security measures to protect cloud applications and the valuable data they handle. A proactive and layered approach is essential to mitigate these risks.
What are the challenges of implementing cloud application security?
While the cloud offers immense benefits for application deployment and scalability, securing these environments presents a unique set of implementation challenges. Organizations embarking on their cloud journey or seeking to enhance their existing cloud security posture must be keenly aware of these common hurdles.
- Misunderstanding the shared responsibility model: A key aspect of cloud security is the shared responsibility model, where the cloud provider secures the underlying infrastructure, but the customer is responsible for securing what they put in the cloud (applications, data, configurations). Often, organizations don’t fully understand this division of responsibility, leading to security gaps.
- Complexity of cloud environments: Cloud platforms offer a vast array of services and configurations, which can be complex to understand and secure. Managing security across multiple cloud services and potentially multiple cloud providers adds further complexity.
- Lack of cloud security expertise: Traditional security teams may lack the specific skills and knowledge required to effectively secure cloud applications. Understanding cloud-native technologies, services, and security best practices requires specialized training and experience.
- Integrating security into DevOps (DevSecOps): Modern cloud application development often follows DevOps principles, emphasizing speed and automation. Integrating security seamlessly into these fast-paced workflows (DevSecOps) can be challenging, requiring changes in culture, processes, and tooling.
- Consistent policy enforcement: Defining and consistently enforcing security policies across diverse cloud environments and application components can be difficult. Ensuring that policies are applied uniformly and are not circumvented requires robust governance and automation.
- Managing Identities and Access across cloud and on-premises: Many organizations have hybrid environments, with applications and data residing both on-premises and in the cloud. Managing identities and access consistently across these disparate environments can be complex.
- Data security and compliance concerns: Ensuring the security and compliance of sensitive data stored and processed in the cloud is a major concern. Different cloud providers have varying security features and compliance certifications, and organizations need to ensure they meet all relevant regulatory requirements.
- Third-party risks: Cloud applications often rely on various third-party services, APIs, and open-source components. The security of these external dependencies can impact the overall security of the application.
- Cost considerations: Implementing comprehensive cloud application security can involve significant costs for tools, services, and skilled personnel. Organizations need to balance their security needs with budget constraints.
Addressing these challenges requires a strategic and well-planned approach, involving collaboration across teams, investment in appropriate tools and training, and a continuous commitment to improving cloud application security posture.
Conclusion
In conclusion, securing cloud applications is a multifaceted and ongoing endeavor. By understanding the unique challenges, implementing proven best practices, and establishing robust processes throughout the application lifecycle, organizations can effectively mitigate risks and build a secure foundation for their cloud-native future. Prioritizing cloud application security is paramount for protecting valuable assets, maintaining trust, and achieving sustainable growth in the digital era.
