Case Studies
Real-world success stories where Cloudanix helped organizations secure their cloud infrastructure. Watch how we made a difference across ind…
Read Case StudiesCLOUDANIX
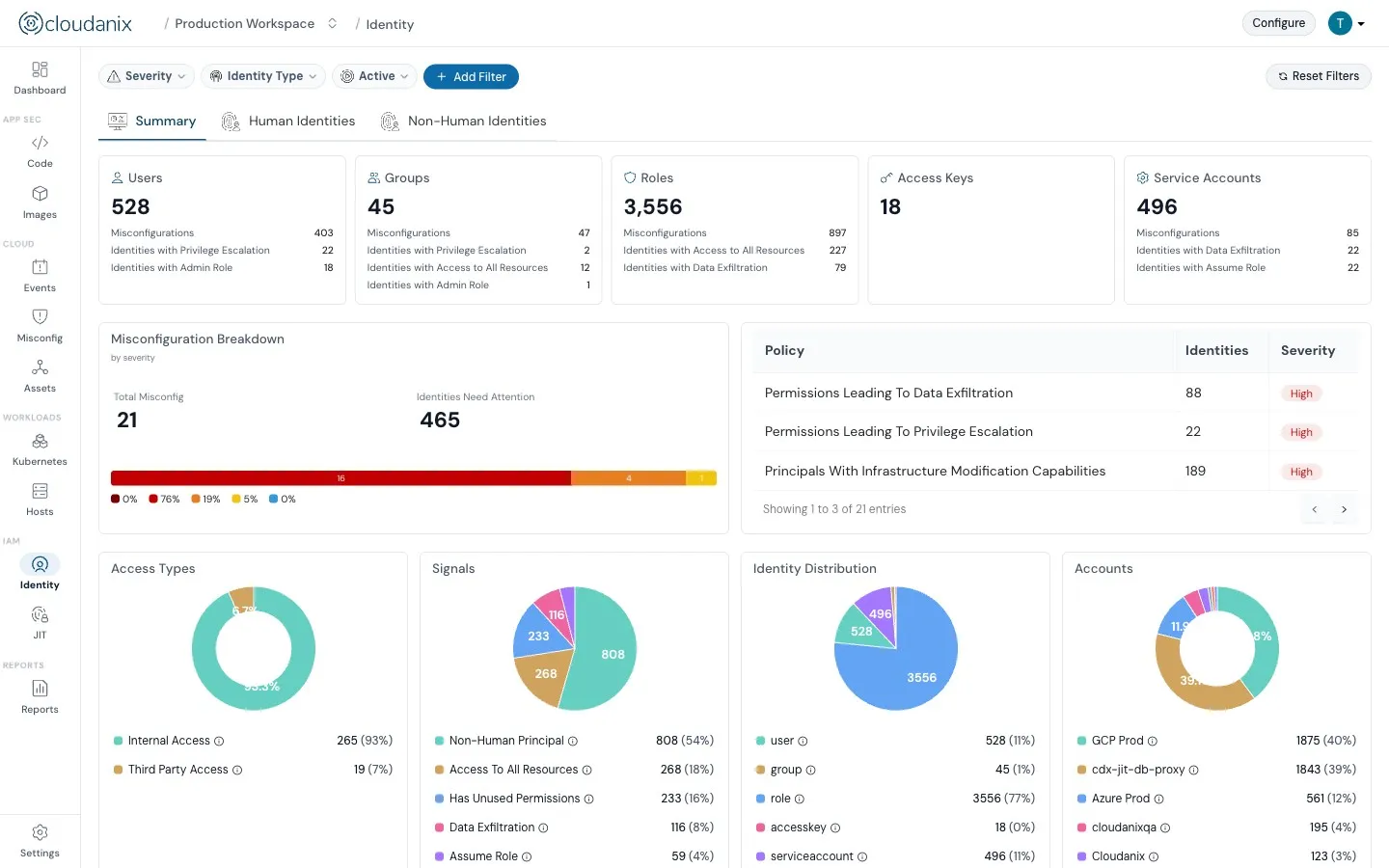
Know who has direct or indirect access to what—Cloudanix IAM simplifies permissions, highlights misconfigurations, and enforces least privilege with insights and automation.
You have multiple team members. And then you got Code, Workloads, Files, Databases, Networks and so much more. These are spread across multiple accounts, multiple clouds—so how do you as a Security team know and approve: "Who should have access to what?"
We've built a unified identity across accounts and highlight IAM misconfiguration risks like Data Exfiltration, Privilege Escalation, and wildcard (*) permissions. These risks are presented to you in a clear and actionable way so you can resolve them before it’s too late.
Cloudanix IAM JIT lets your team request permissions for a limited time in just a few clicks. Permissions are revoked automatically after the task is done. The built-in approval workflow adds oversight and simplifies audit trails.
Explore IAM JIT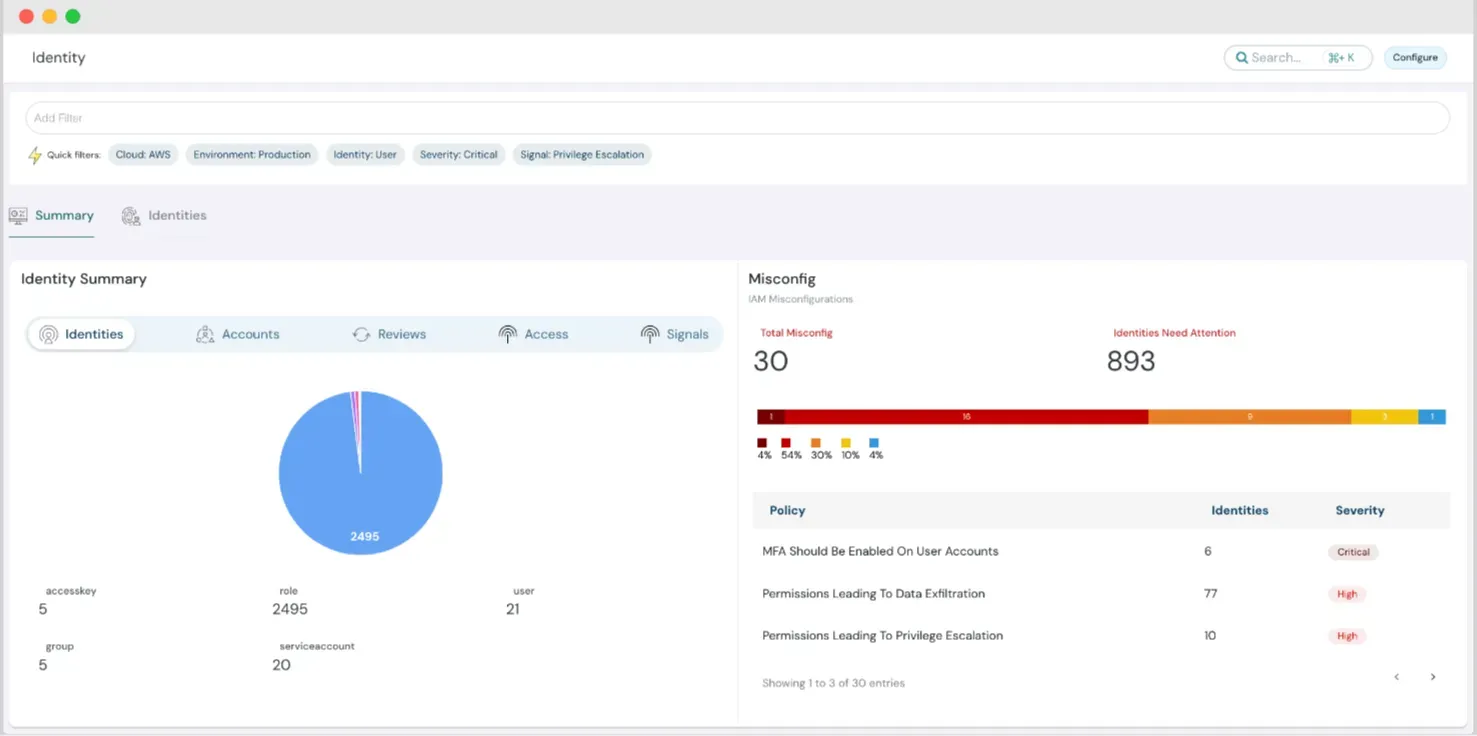
Monitor Non-Human and Human identities, including third-party, cross-account, and internal access. Gain visibility into every access point, making it easier to secure your cloud and stay compliant.
Use advanced IAM insights and right-sizing capabilities to detect unused or excessive permissions. Enforce least privilege access and strengthen your security posture.
Cloudanix provides right-sizing suggestions based on actual user activity. Whether it’s defining a new policy or removing unused permissions, you get tailored recommendations to enforce granular access control.
Customer Voice
Cloudanix is always on my team's lips because of its exceptional support. Be it a small or big query, Cloudanix has gone above and beyond to resolve them. This one's a keeper for us.

Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoReading Resources
Identity and Access Management (IAM) is the first layer of defense in cloud security. Understanding IAM principles is critical for protecting access, enforcing least privilege, and ensuring accountability in your cloud infrastructure. Explore the key reasons why IAM must be a focus for security and compliance teams, especially in complex multi-cloud environments.
CLOUDANIX
Explore guides, checklists, and blogs that simplify cloud security and help you secure your infrastructure.
Real-world success stories where Cloudanix helped organizations secure their cloud infrastructure. Watch how we made a difference across ind…
Read Case StudiesExplore the various key areas of IAM that are evolving with the rise of AI and how all these changes are breaking the boundaries of cloud se…
Read the blogDiscover the importance of Just-in-Time access in cybersecurity, its benefits, implementation, types, and challenges.
Read the blogExplore the various key areas of IAM that are evolving with the rise of AI and how all these changes are breaking the boundaries of cloud se…
Read the blogCloudanix offers you a single dashboard to secure your workloads. Learn how to set up Cloudanix for your cloud platform from our documentati…
Take a lookIAM is not a one-time fix; it requires ongoing attention and continuous improvement.
Read the blogA complete history of changes, improvements, and fixes for Cloudanix. Subscribe to get notified about the latest updates.
View Changelog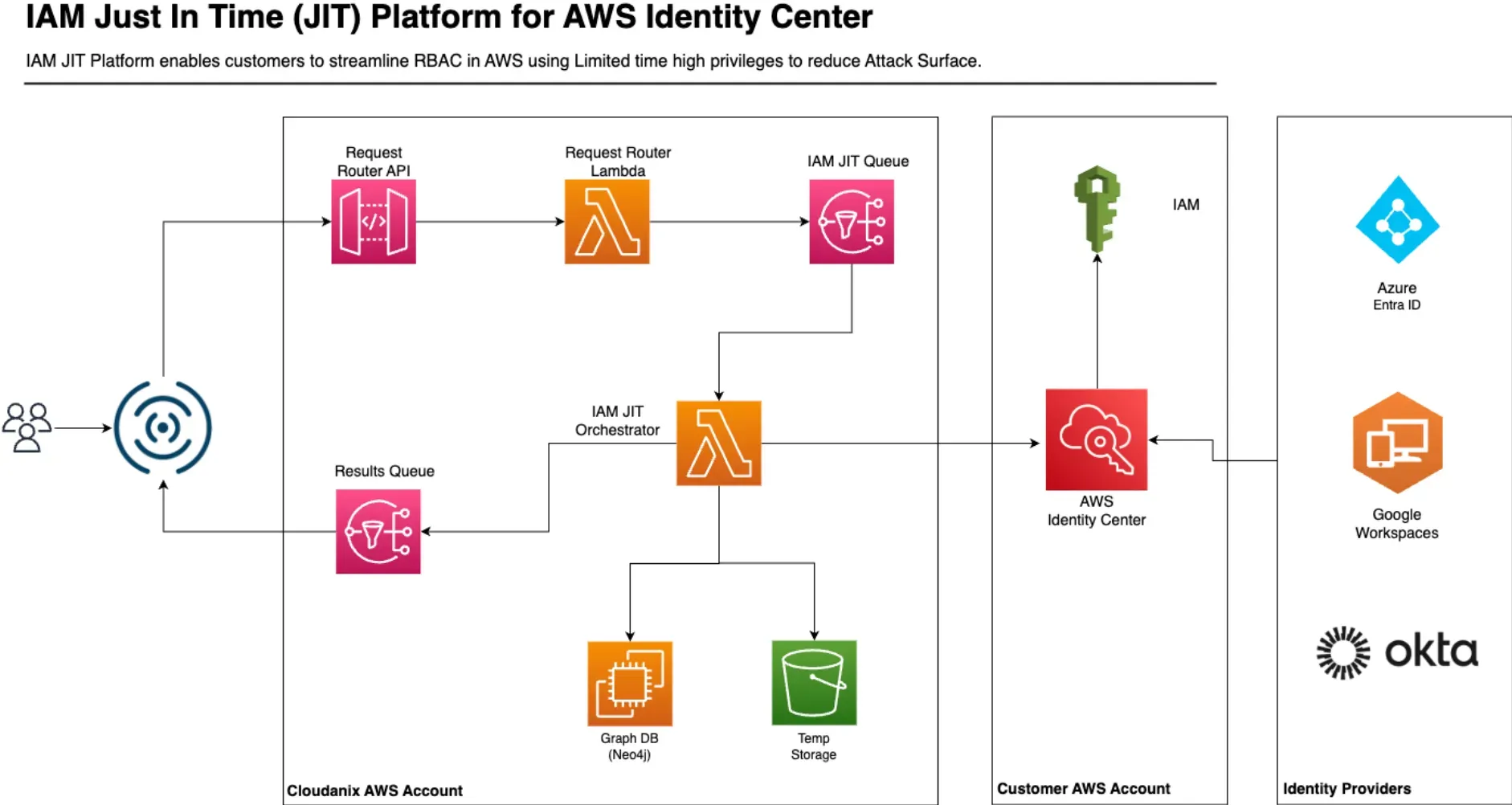
Dive deep into how IAM JIT and AWS Identity Center can strengthen your IAM security posture and streamline identity workload management.
Read the blog
IAM tools weren’t built for today’s multi-cloud environments. Learn how to adapt your identity and entitlement management for the cloud era.
Learn moreDiscover key considerations for setting up IAM, common vulnerabilities, and best practices for securing remote access and sensitive data.
Listen Now