Why Cloudanix + NIST?
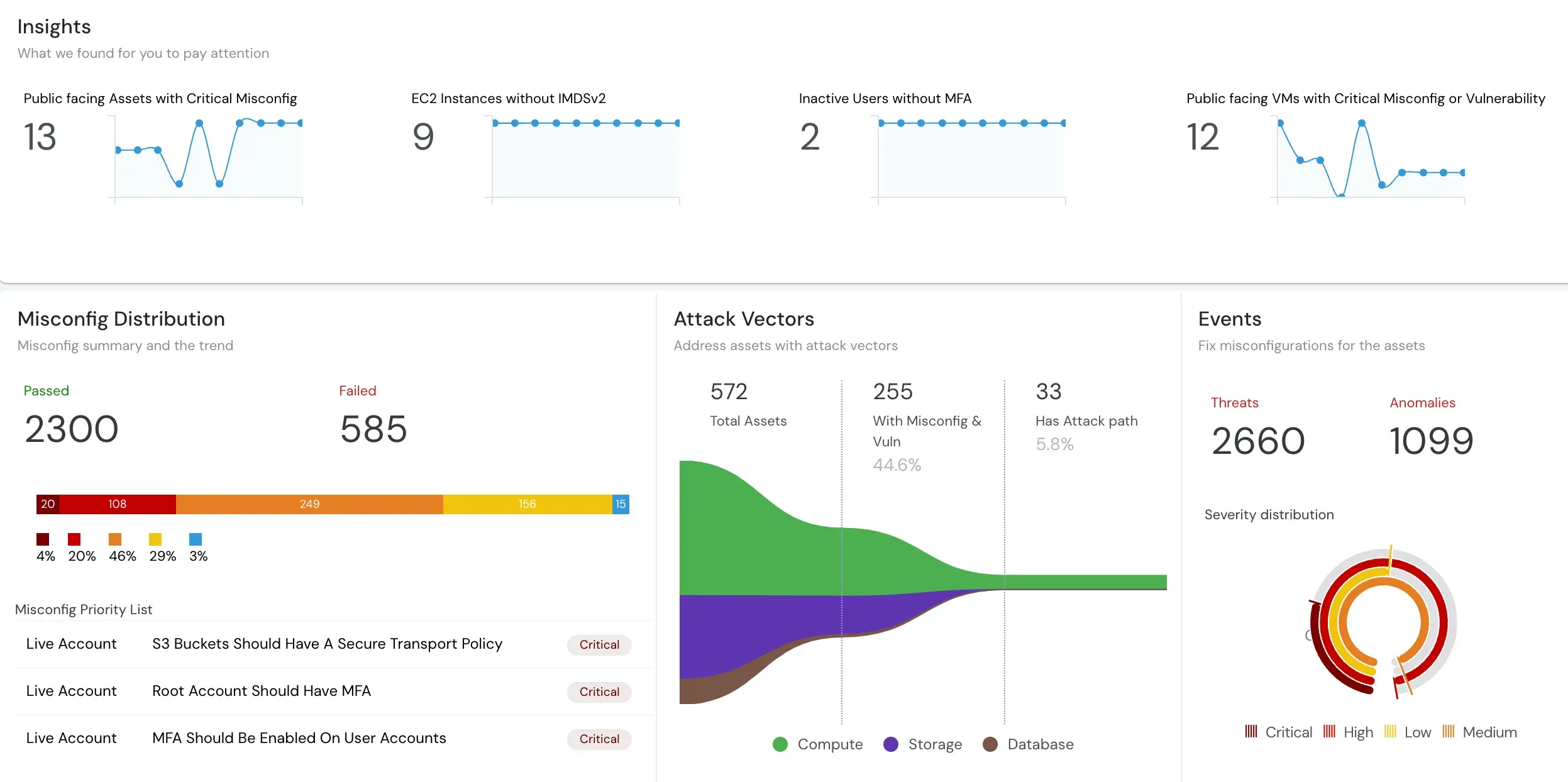
As cloud adoption grows, so do security threats. NIST offers a valuable framework, even if voluntary, for reducing cybersecurity risks. Cloudanix helps you align with NIST 800-53 standards by automating audits across your cloud environments. For example, our AWS CloudWatch Audit recipe checks for events like IAM Policy Changes, Console Sign-in Failures, and CloudTrail configuration updates — helping you stay compliant with NIST AC-2 (12)(a) on monitoring atypical account usage. You get instant audit reports highlighting any violations, allowing fast remediation and ongoing compliance tracking. Cloudanix applies predefined rules mapped to NIST controls to simplify compliance. These automated checks reduce manual effort while ensuring your configurations remain in alignment with security best practices. Track configuration changes, sign-in failures, and policy updates in real-time. Cloudanix’s alerting and reporting tools ensure you are notified of anomalies instantly, enabling quick response to potential threats.