Visibility
Real-time scanning helps provide the visibility teams need to maintain code sanity and keep vulnerabilities out.
CLOUDANIX
Correlate security findings from PR to runtime
Code Security
Cloudanix bakes security into your development workflow — scanning pull requests, analyzing dependencies, and delivering AI-powered remediation without the friction.
Key Challenges in Code Security
Code security challenges start from the very first line of code. If not tackled early in the Software Development Life Cycle (SDLC), they can create long-term risks. A reliable security solution should help teams improve visibility, support multiple tools, and prioritize risks effectively.
Real-time scanning helps provide the visibility teams need to maintain code sanity and keep vulnerabilities out.
The tool should support popular coding languages and CI/CD tools to be adopted by diverse developer teams proficient in various stacks.
A good tool must provide actionable insights that prioritize risks by severity, enabling teams to fix the most critical issues first—saving time and boosting productivity.
Cloudanix
Cloudanix ensures your code remains secure from pull request to production. Our platform addresses the modern security needs of fast-moving dev teams—without the friction.
Investing in tools that provide multi-faceted security like SAST, DAST, SCA, IAST, Database Scanning, ASTaaS, and other complicated jargon has become a norm. But do you need all this? Cloudanix provides correlation right from PR to runtime, eliminating the need for some of these capabilities like DAST, which is notorious for consuming high compute of your system while providing you the security your code requires. As mentioned above, Cloudanix understands, that new tools and processes are difficult to adopt in organizations and can cause friction. Our Zero Friction philosophy helps us build our platform so that Security teams, DevOps teams and the Engineering teams stay on the same page and align from Day 1 when it comes to Code-To-Cloud security.
Achieve Zero Friction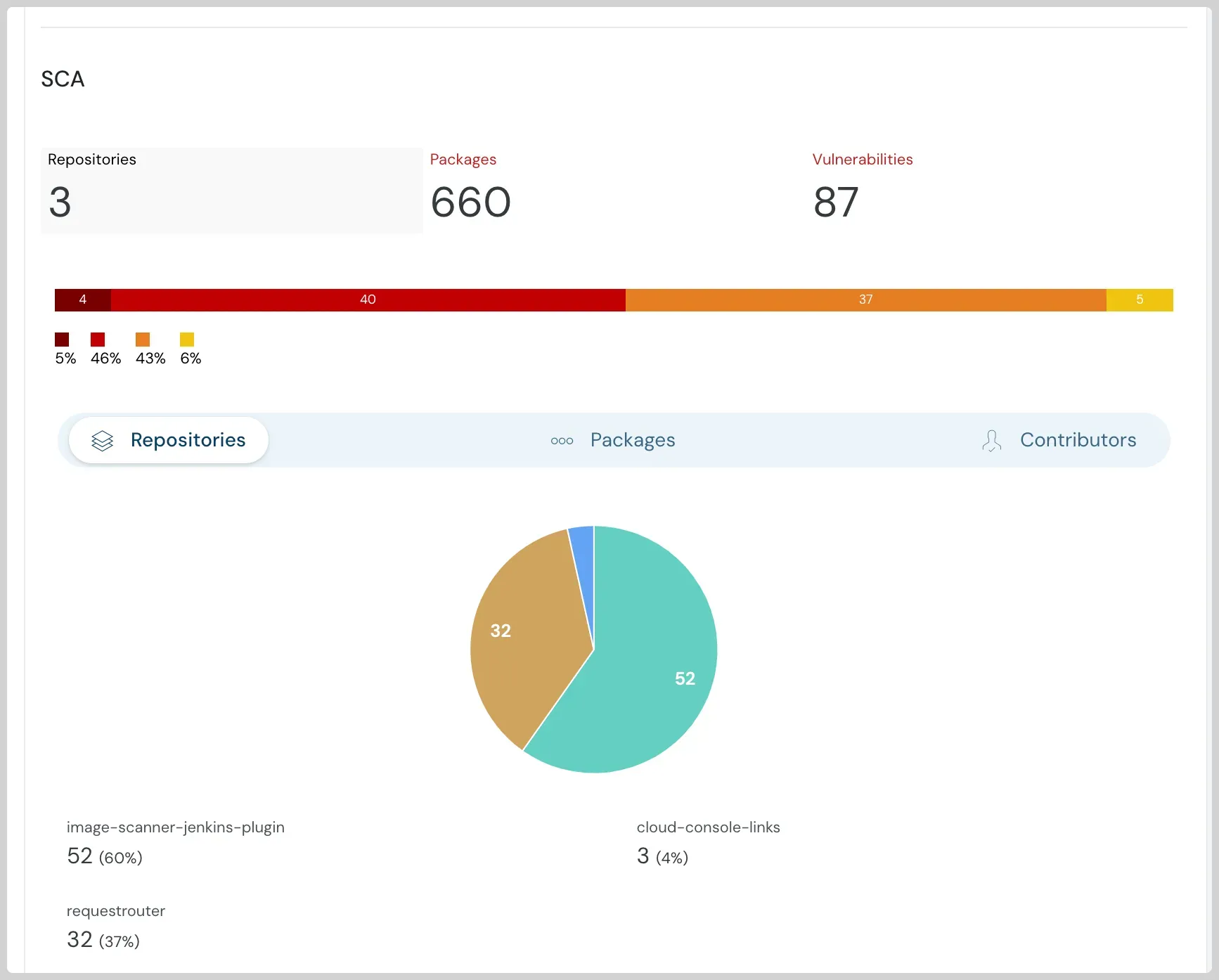
Cloudanix SCA helps Identify Vulnerabilities and Compliance Issues (License, Maintenance, Security Practices, etc.). Automatically scan your Code Repositories for Software Bill Of Materials (SBOM) and find out Vulnerabilities, Compliance Issues associated with the SBOM for Supply Chain Security.
Explore Cloudanix SCA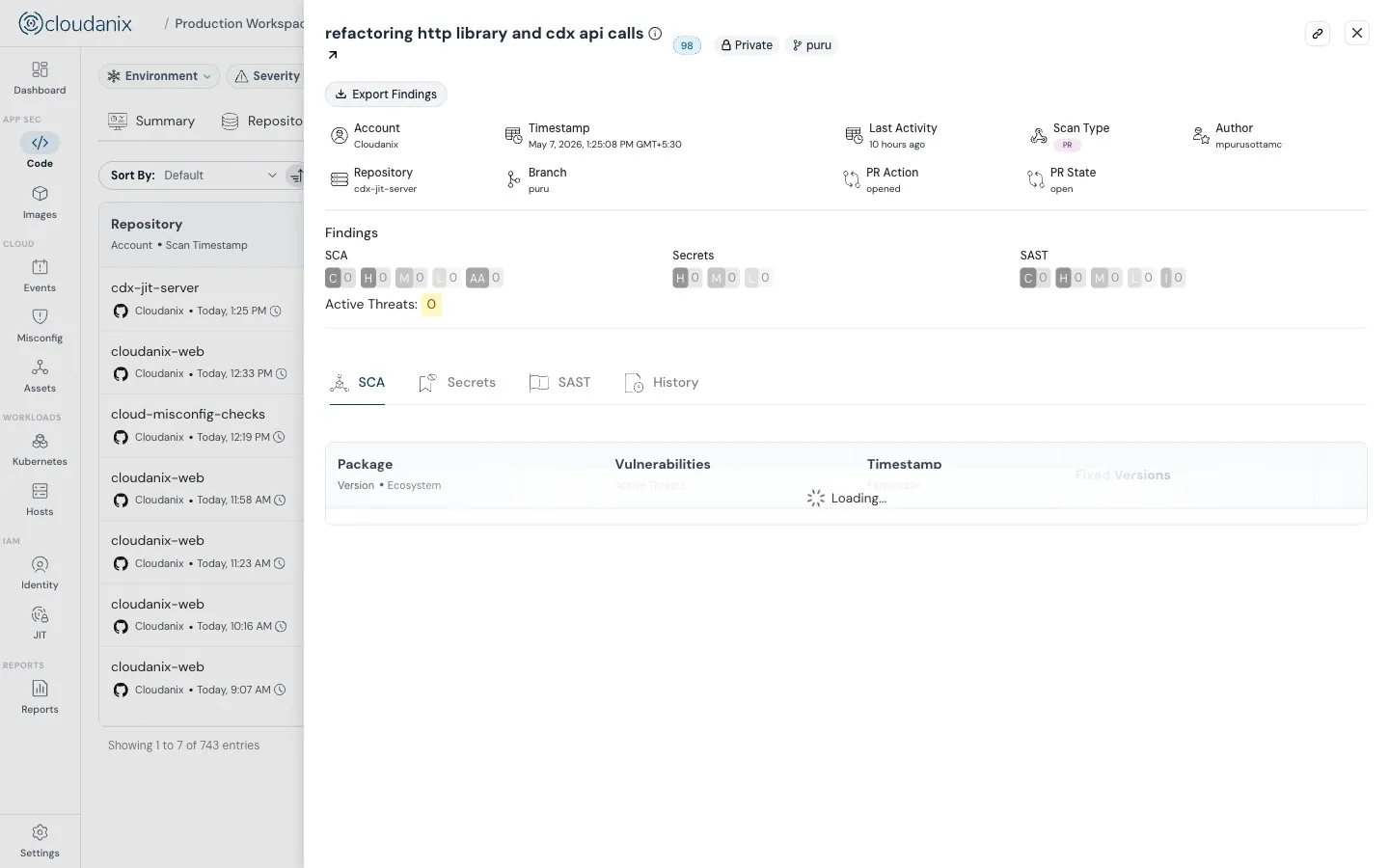
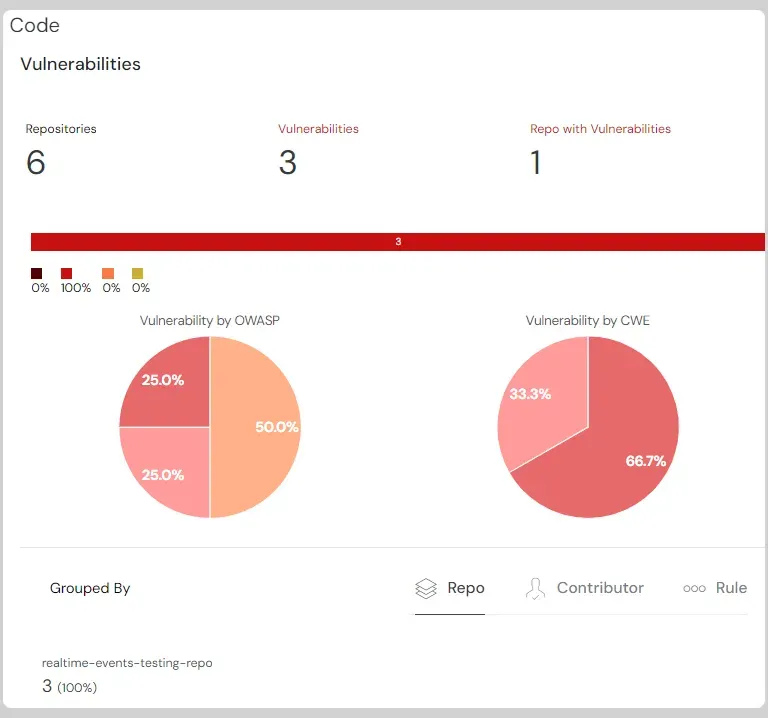
Code Security is now extended by showing Code Blocks affected by Vulnerabilities and also enables you to Triage them by using Review Capability. Review Capability includes “Pause”, “Acknowledge” and “Accept Risk” options.
Explore Cloudanix SASTCLOUDANIX
Cloudanix delivers exceptional code security for your crown jewels from PR to runtime.
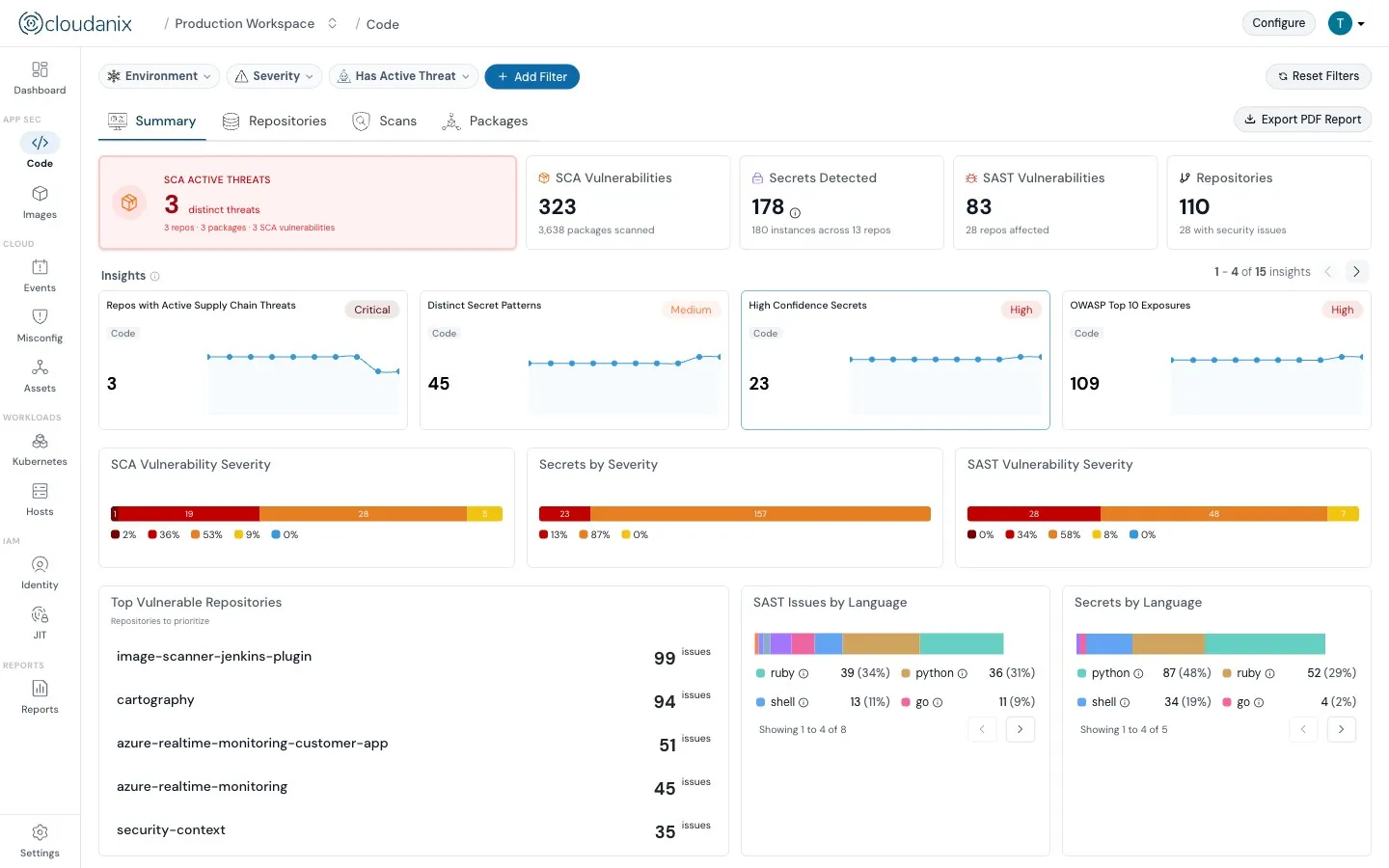
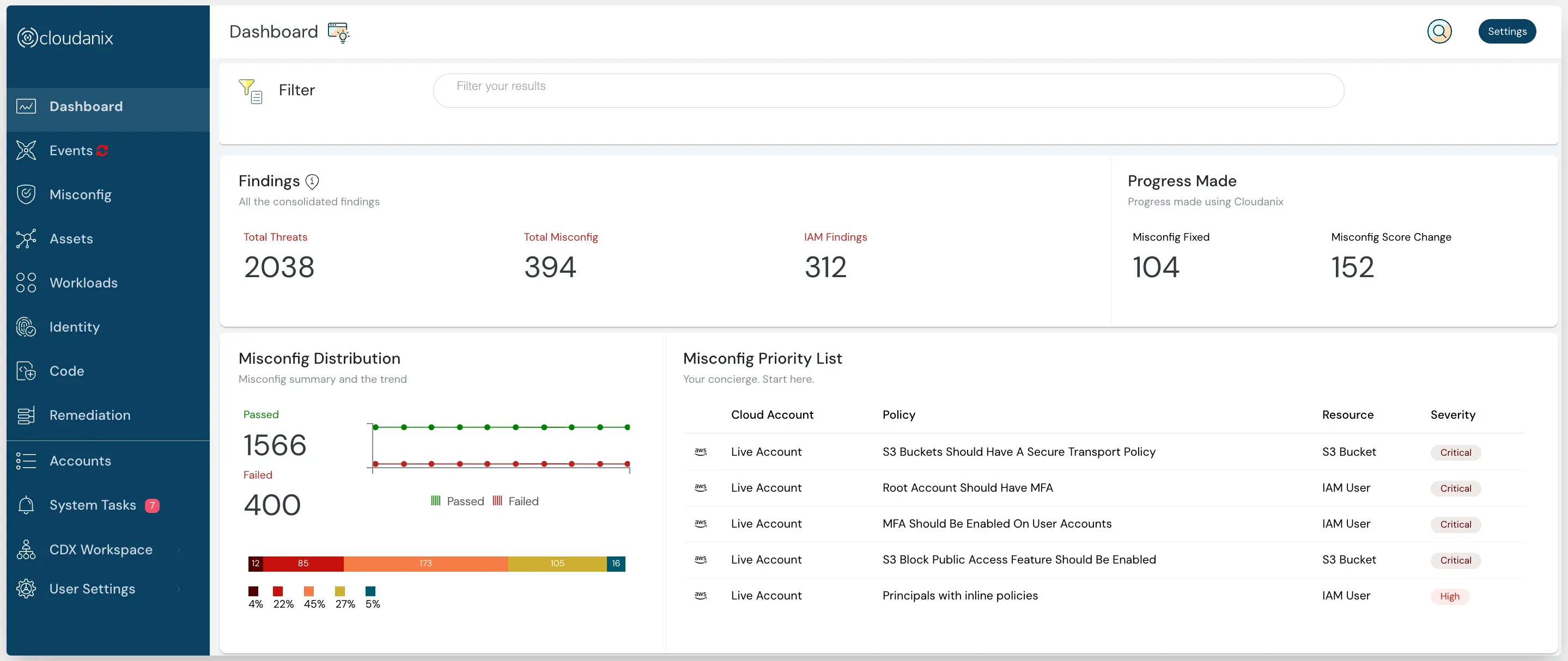
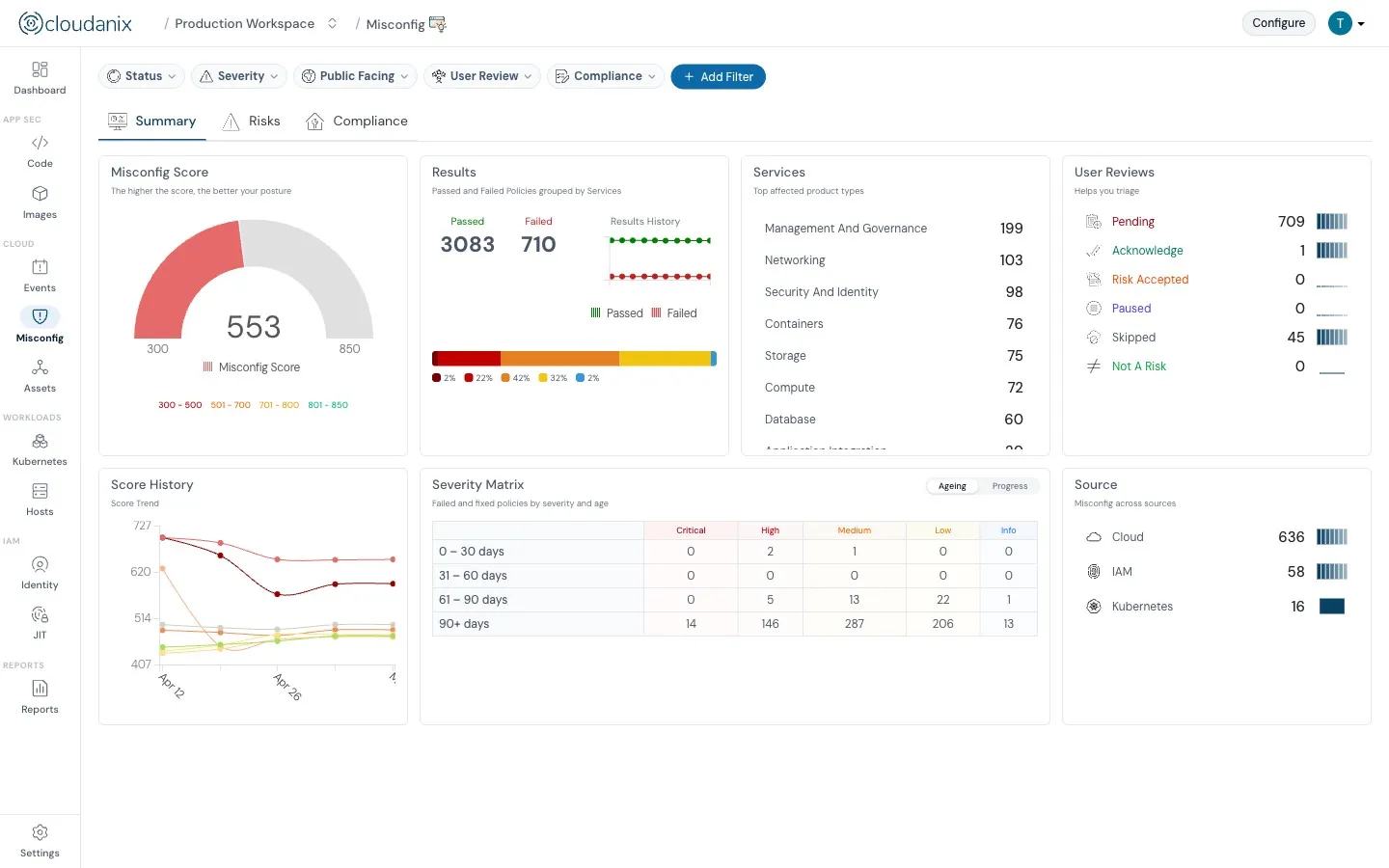
Cloudanix proactively safeguards your codebase against potential security issues by automatic real-time scans of code changes immediately upon the submission of a pull request (PR). Dashboard: Security posture Dashboard: Security posture
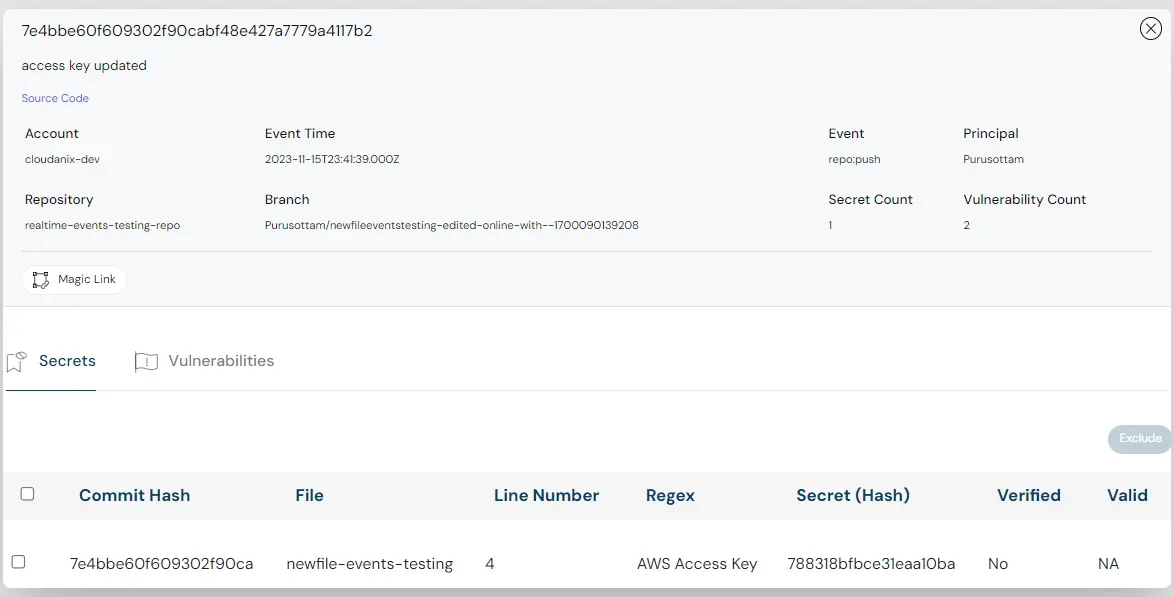
With a neat and easy-to-use dashboard, it helps developers intuitively navigate to the findings while eliminating false positives. Cloudanix starts your security journey from code all the way to cloud, including your identity management until where it runs in your workload.
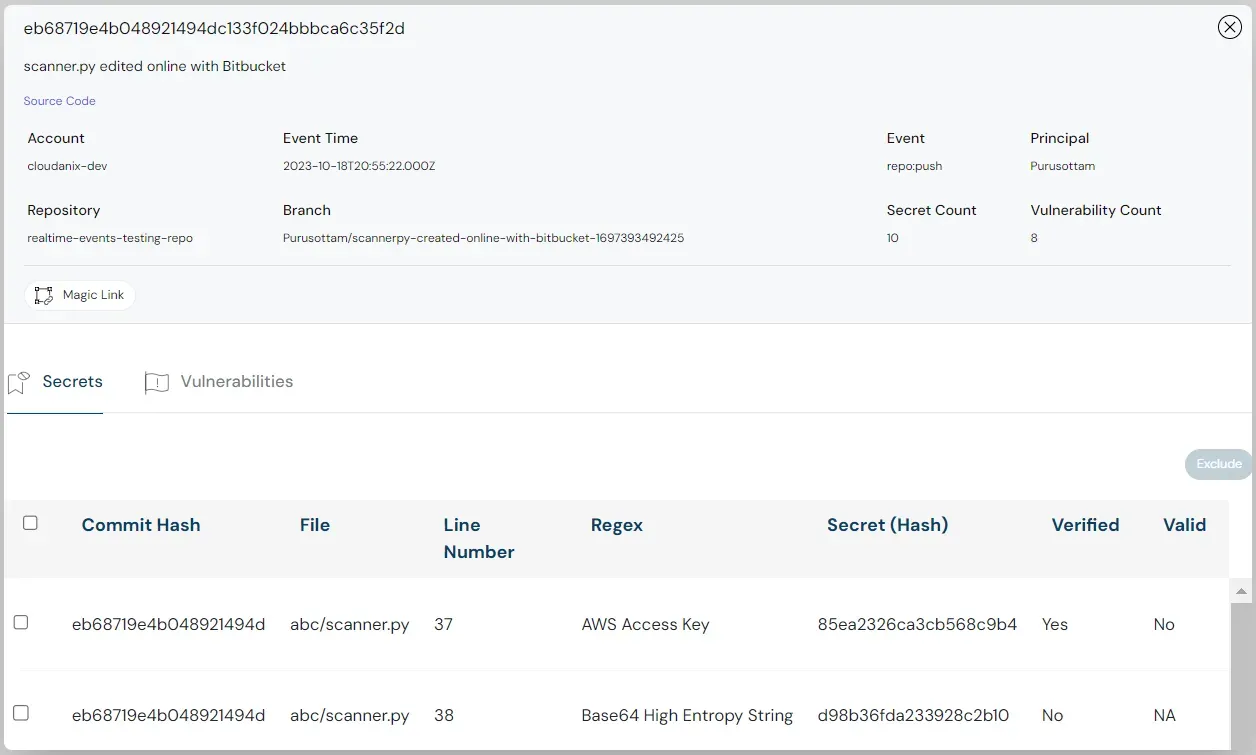
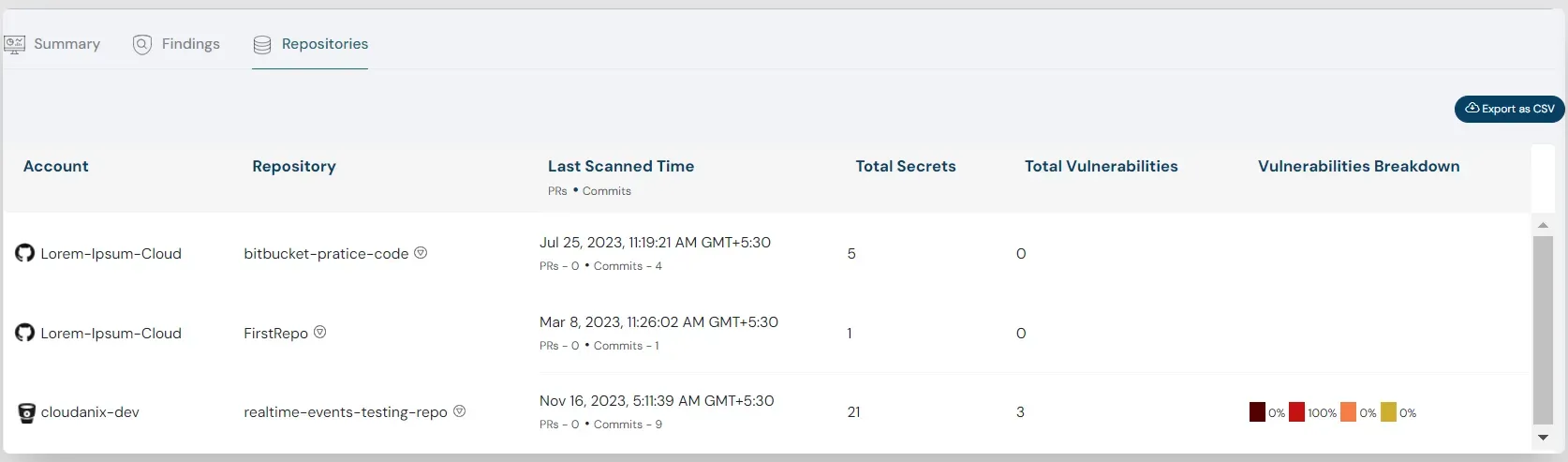
Cloudanix also helps you connect multiple code repositories with one click and shows all the data while correlating with misconfigs, threats, vulnerabilities, checked-in secrets, etc in a single dashboard, reducing the fatigue of switching between screens. Dashboard: Security posture Dashboard: Security posture
Delivering detailed insights and remediation recipes leveraging the power of Gen AI to ensure teams do not waste their time. Blog: Building Security Using Generative AI >
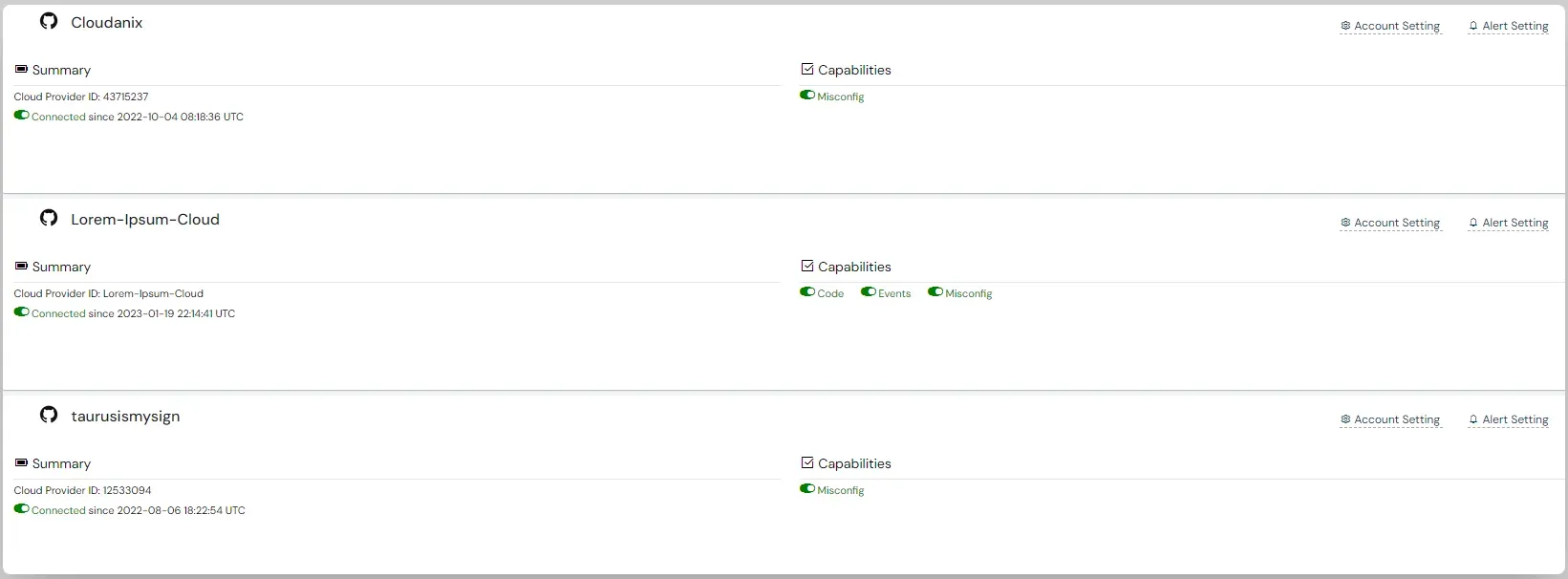
Cloudanix integrates seamlessly with code repositories like GitHub, Bitbucket and brings all your data in one place. Cloudanix creates a productive and collaborative environment that helps teams raise JIRA tickets.
In this interactive video, you will see how Cloudanix Code Security helps you find and fix vulnerabilities in your code.
Customer voice
Cloudanix solves many challenges DevSecOps teams face — multi-cloud coverage, continuous new features like drift detection and SOC 2 compliance, and real operational benefits every day.
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoCLOUDANIX
Explore guides, checklists, and blogs that simplify cloud security and help you secure your infrastructure.
Learn how AI code remediation automates the process of finding and fixing software vulnerabilities. Discover various techniques for intellig…
Read more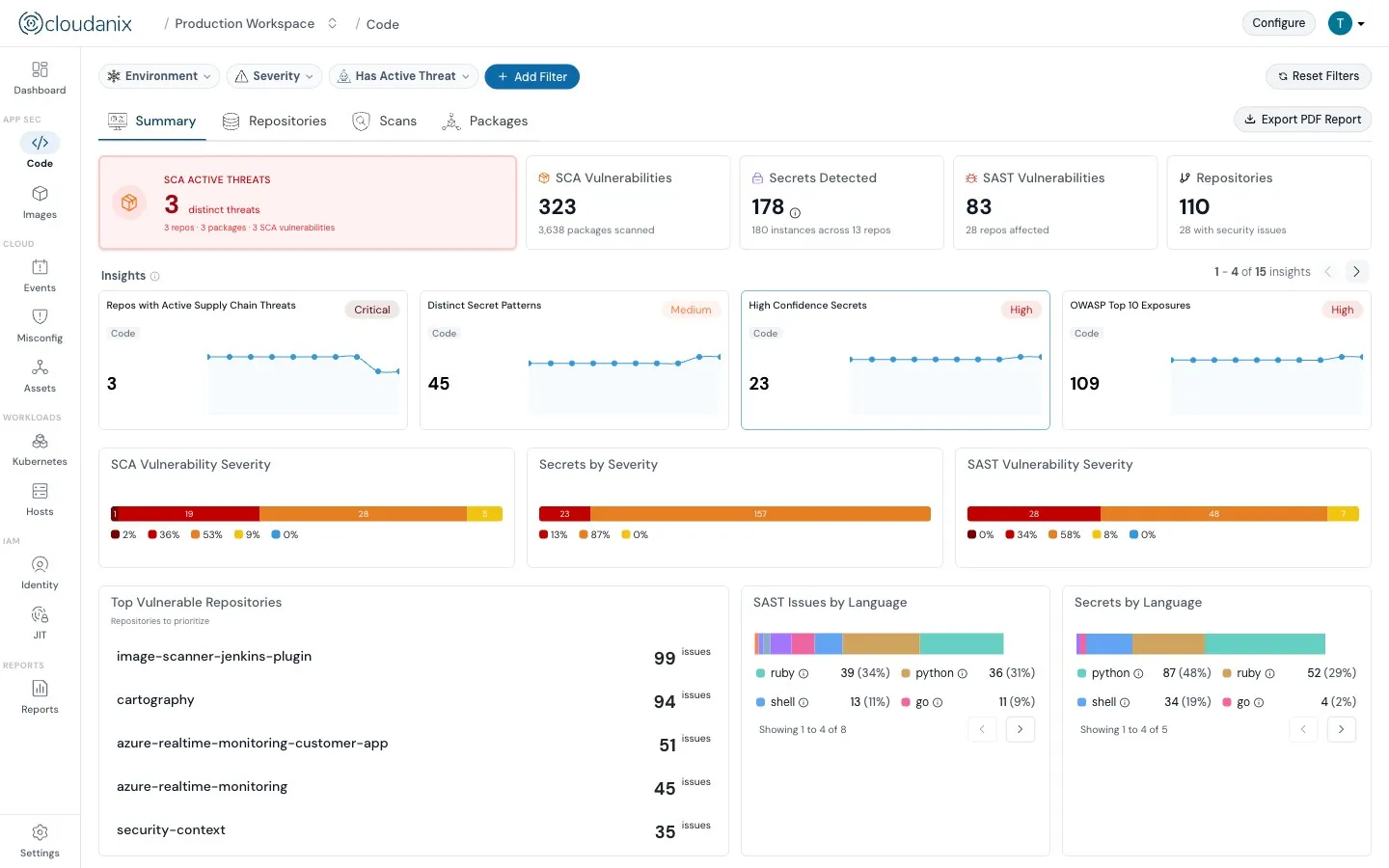
Learn about code security fundamentals, OWASP Top 10, security tools like SAST/DAST, and best practices for embedding security throughout th…
Read the blogCloudanix offers you a single dashboard to secure your workloads. Learn how to set up Cloudanix for your cloud platform from our documentati…
Take a lookA comprehensive guide to secure coding practices, covering vulnerabilities, prevention techniques, and industry standards
Know moreA complete history of changes, improvements, and fixes for Cloudanix. Subscribe to get notified about the latest updates.
View ChangelogA framework for embedding privacy into the entire product development lifecycle, ensuring it is a proactive consideration, not an afterthoug…
Read the blog