Audit and Compliance
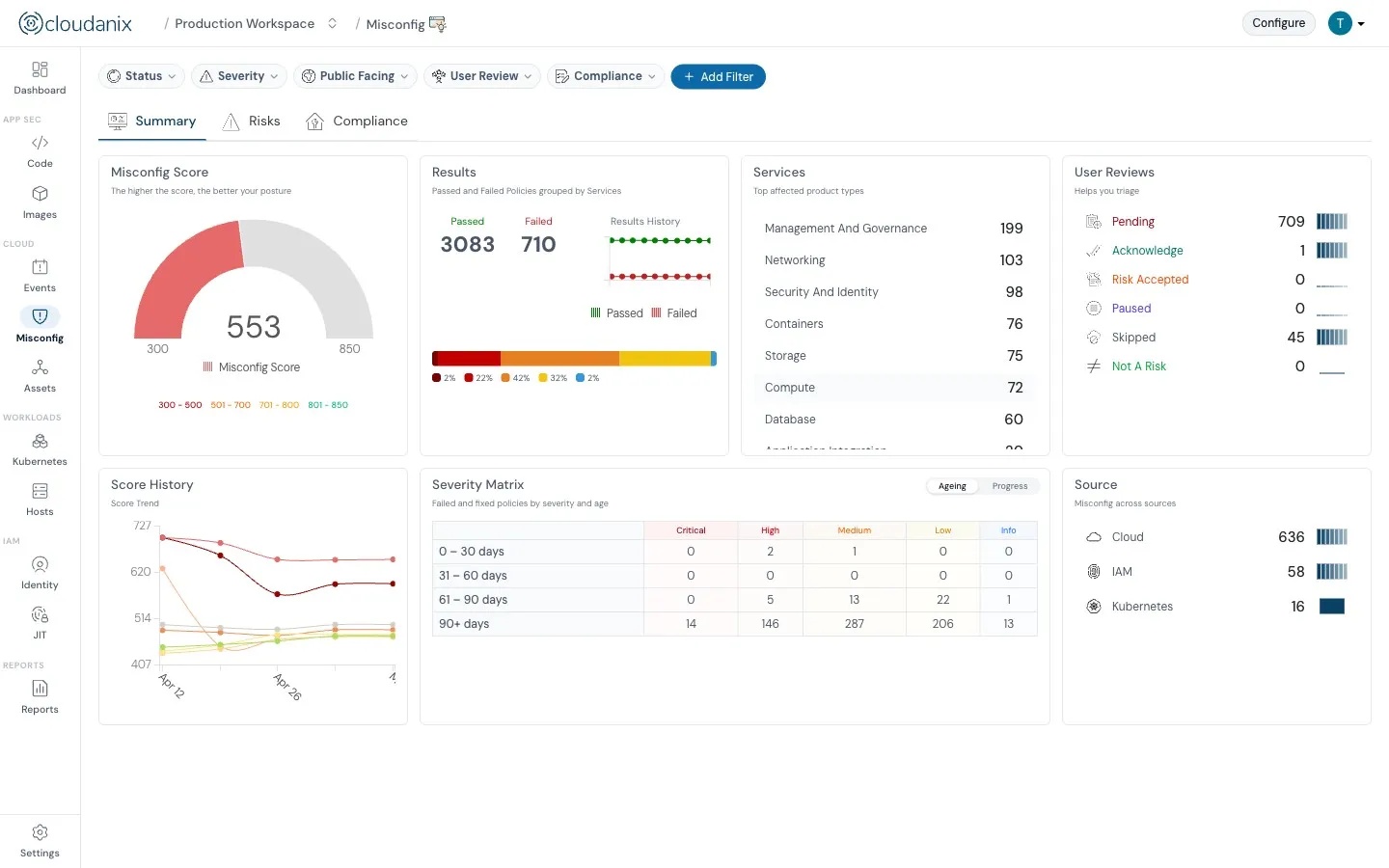
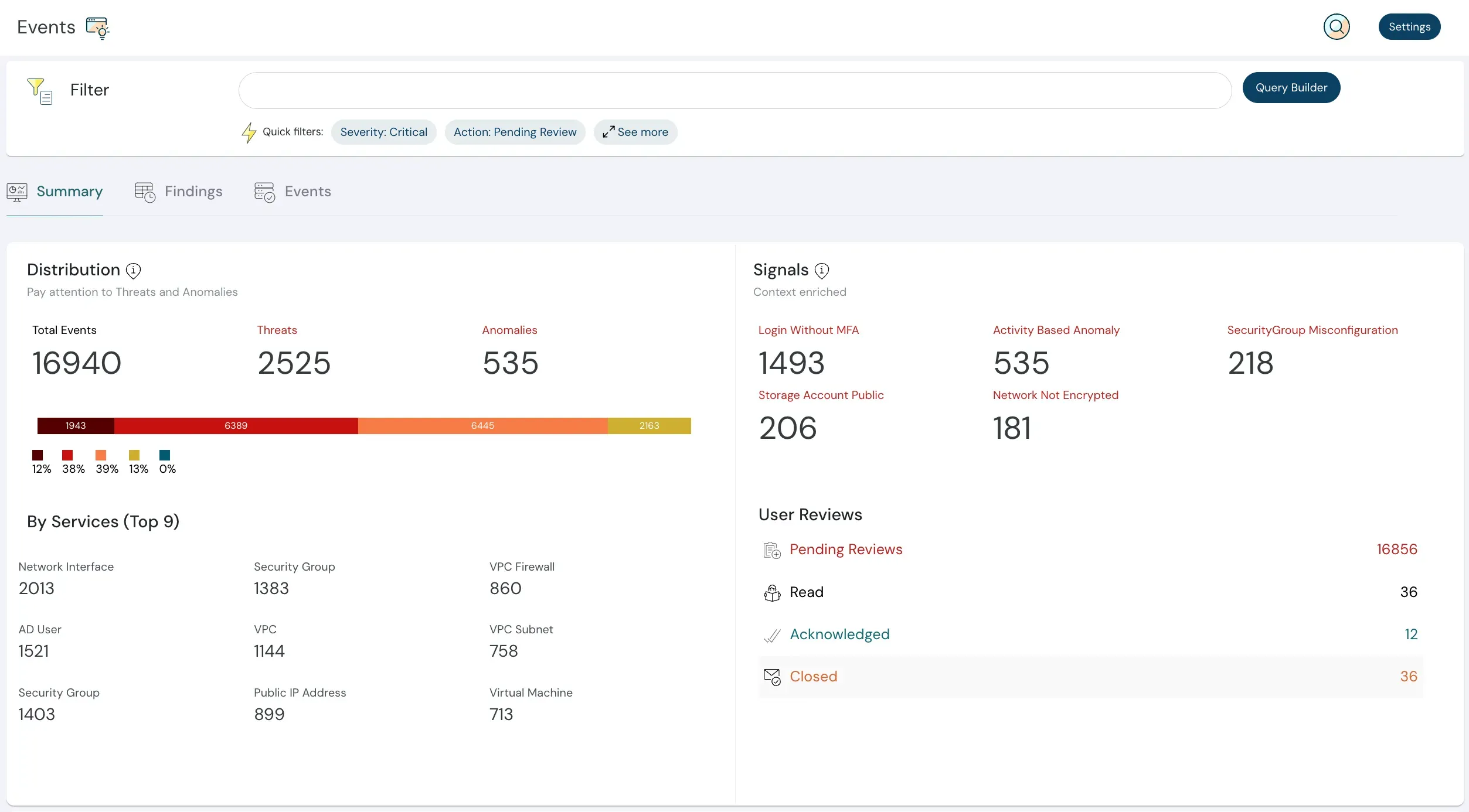
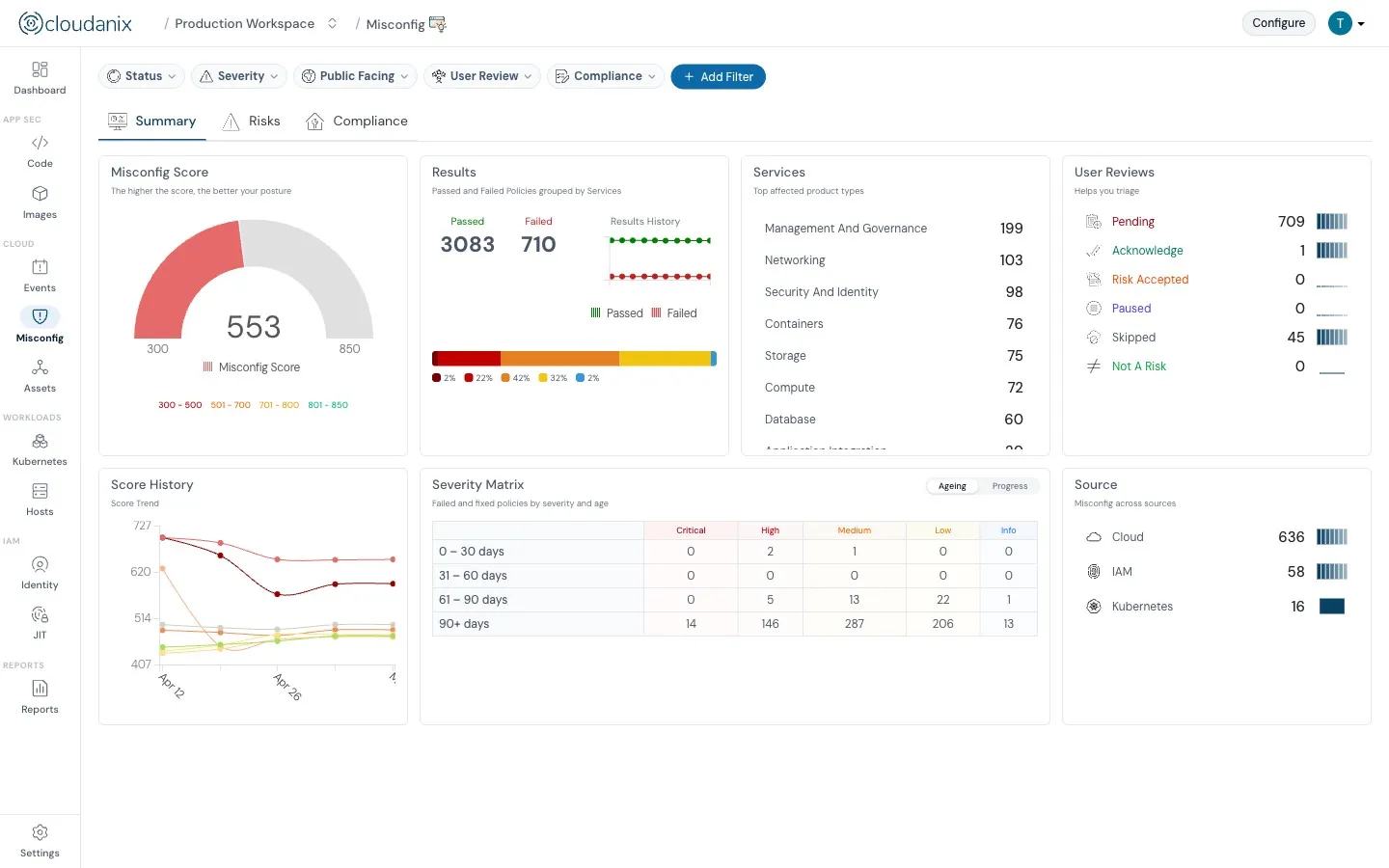
For any enterprise, audit and compliance is essential for stakeholder and customer trust. Meeting legal requirements is no longer optional, and adhering to best practices is equally important. Cloudanix helps you meet standards like HIPAA, SOC 2, GDPR, and ISO 27001.