Why Cloudanix?
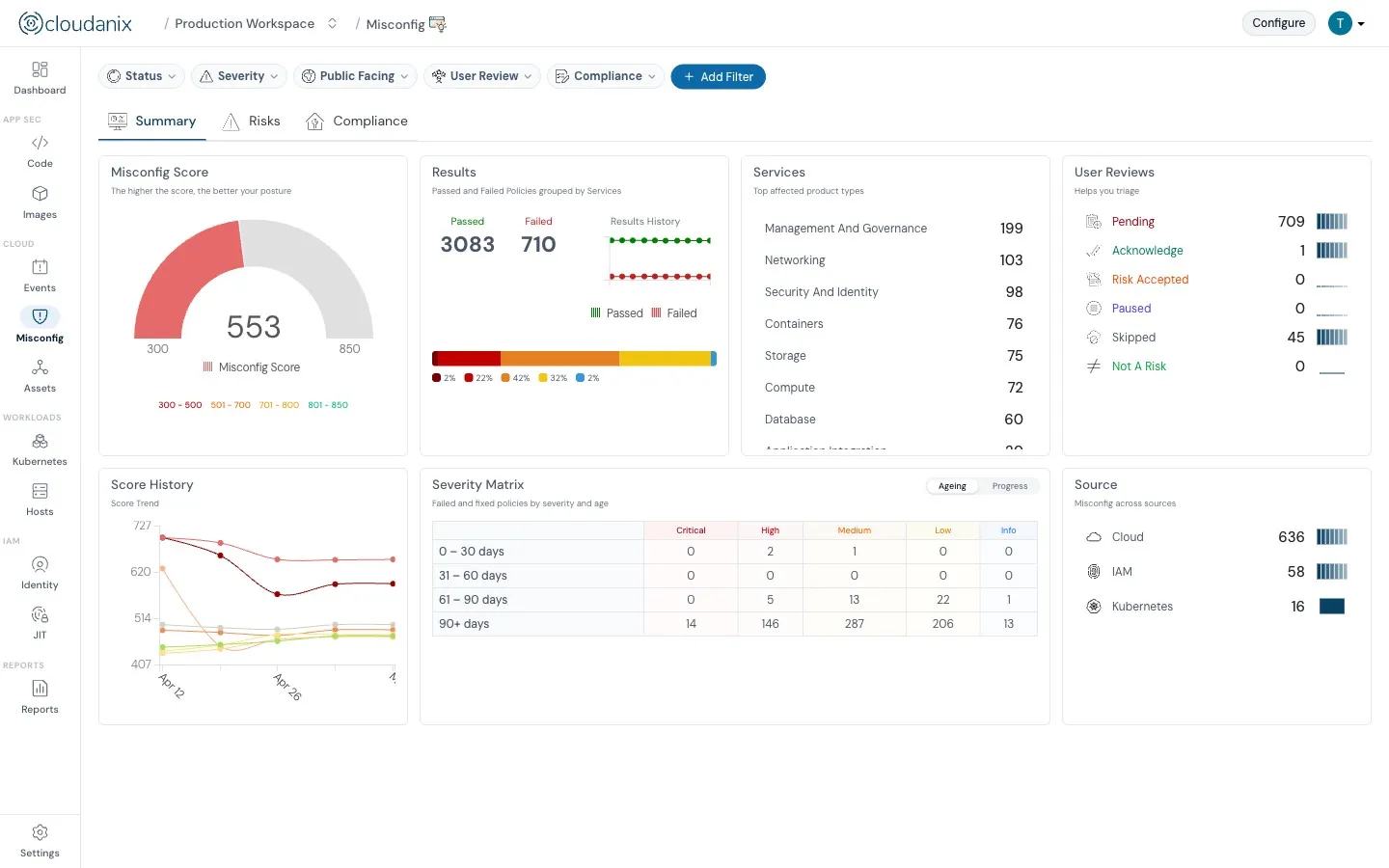
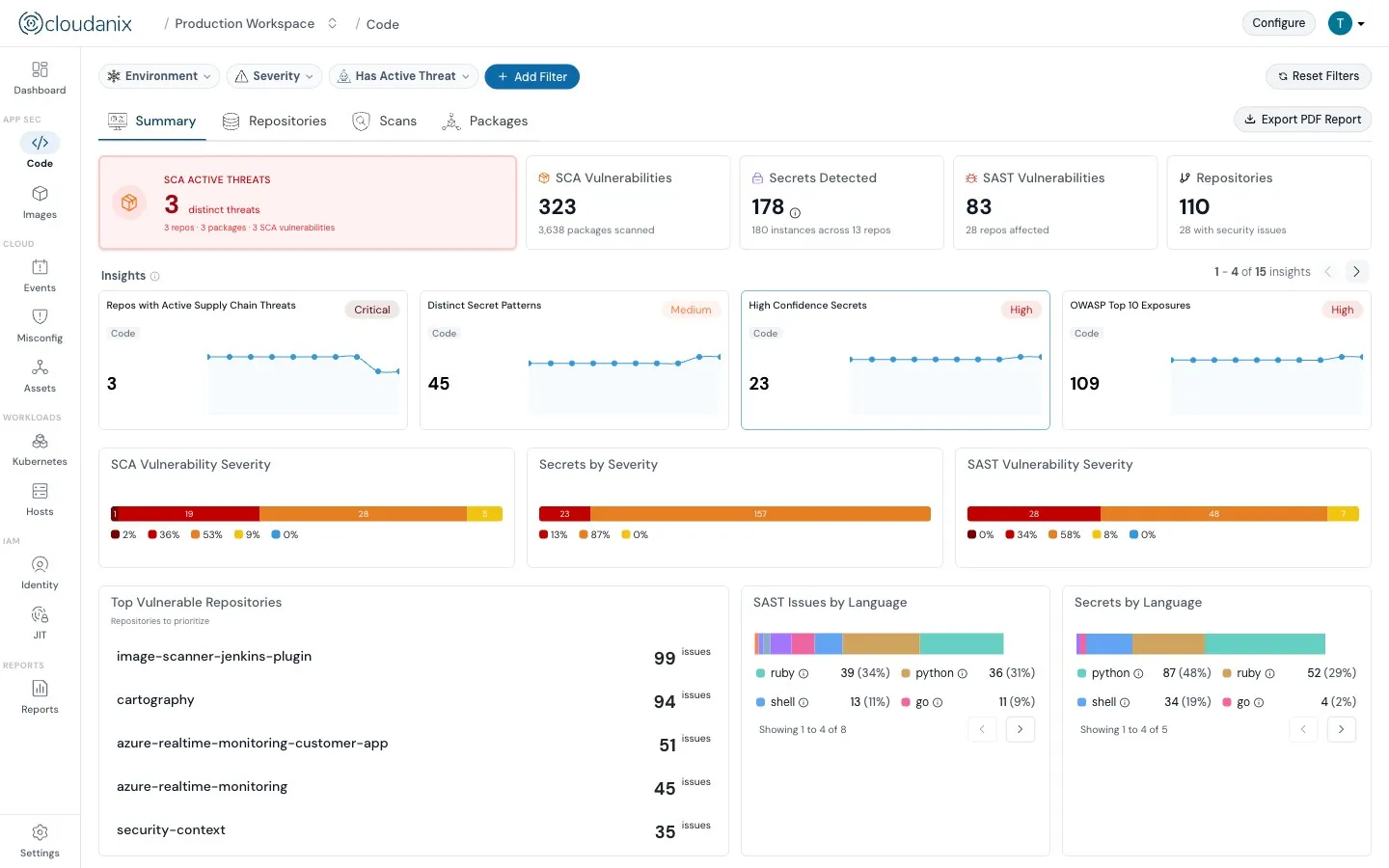
Cloudanix automates audits that perform various checks consisting of different rules on a wide variety of recipes that we provide. For instance, our AWS recipe of EC2 Audit contains several rules like Public Snapshots, Older Instances Running, Default VPC Not In Use, EC2 IAM Roles, EC2 Instance Counts, and many more.
These audit rules help you comply with several compliance controls and take care of assurance processes, data security, and privacy.
We have many other recipes that ensure you stay compliant and build trust with your customers while we are taking care of your security audits!