And with your Risk Score, you'll get a better picture of your security!
According to Forbes, 50% of companies experienced cyber-attack attempts every week, in 2021. We are almost always on the verge of a cyber attack in this industry, which is concerning.
We realized how important it is to understand where we stand in terms of the risk factors. Thus, we introduce you to the latest feature we added to our product — “Risk Score”.
Cloud Compliance | CSPM | Cloudanix
Risk score
The higher the risk score, the safer you are!

Risk score trend
You can get a view of your risk score trend from our dashboard.
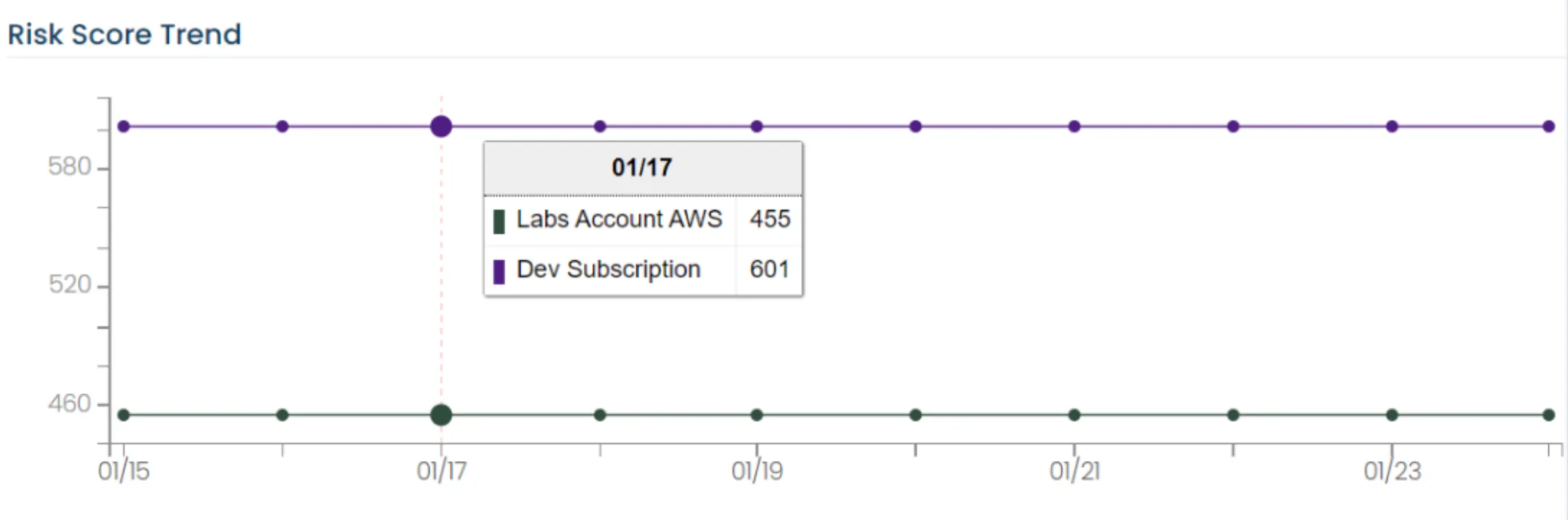
Cloud risk trend | Cloudanix dashboard
Here’s what we have been busy shipping
In case you missed our previous updates, here’s what we have shipped:
- Cloudanix is now on AWS Marketplace — Less friction and delays for your Cloud security teams to fix vulnerabilities and reduce the risks.
- Custom Views — Now you can build custom queries (called as Views) which you can use to load information rather quickly.
- Enhanced Filter Control — The filter control is now enhanced to allow you to filter data using Tags/ Labels, or even an individual policy. This helps you slice and dice the information for better communication.
- Console link — Just looking at the asset name in Cloudanix console isn’t as productive as being able to click on it which takes you to the cloud provider’s console. We are rolling out the Console link which gives you 1-click access to the AWS/ Azure/ GCP console.
- Console project is open-sourced — We feel many in the DevOps and SecOps community will benefit from our work on the Console Link.
Also, in case you missed our previous updates:
Ready to see your graph?
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Tuesday, Apr 14, 2026
Top 15 Cloud Misconfigurations in 2026 - How to Fix Them?
Most cloud breaches today are not the result of sophisticated zero-day exploits. They are the result of misconfiguration
Read MoreMonday, Apr 13, 2026
Top 18 Challenges of Cloud Security in 2026
The rapid adoption of cloud computing has brought unprecedented agility and scalability, making it a cornerstone of mode
Read MoreTuesday, Feb 10, 2026
The 2026 CNAPP Compliance Framework: Turning Audit from Crisis to Continuity
Introduction: The Death of the Point-in-Time Audit In the high-velocity cloud landscape of 2026, the traditional app
Read More