Beyond the Perimeter: How Kapittx Secured the Heart of Fintech AI with Database Activity Monitoring (DAM)
About Kapittx
Kapittx is an AI-powered platform that revolutionizes the Accounts Receivable process. By empowering companies to strengthen their cash flow through faster, AI-driven collections, Kapittx serves as a critical financial engine for its customers. Handling large-scale financial data requires Kapittx to maintain the highest possible standards for code, cloud, and data security.
The Challenge: The Hidden Risks of Standing Access
As a Fintech leader, Kapittx faced the “Double Threat” of infrastructure exposure and data vulnerability:
- The Exposure Gap: Permanent standing access to AWS and Kubernetes environments left a constant attack surface.
- The Data Blind Spot: Traditional security tools could see who logged into a database, but they couldn’t see what they were doing once inside.
- Compliance & Privacy: With a growing list of enterprise customers, Kapittx needed a way to mask sensitive financial data and prevent unauthorized query execution to meet strict privacy mandates.
The Solution: Deep Data Governance with DAM
Kapittx partnered with Cloudanix to implement a “Defense-in-Depth” strategy, centered around Database Activity Monitoring (DAM).
- Database Activity Monitoring (DAM): This became the cornerstone of Kapittx’s security. It provides real-time visibility into database interactions, allowing the team to monitor every activity.
- Data Masking & Prevention: Cloudanix enables Kapittx to automatically mask sensitive information, ensuring that even authorized users only see what is necessary. Furthermore, it allows for Query Prevention, stopping high-risk or unauthorized queries before they can execute.
- Just-In-Time (JIT) Cloud & DB: Kapittx eliminated permanent credentials. Access is now granted only for specific tasks and revoked immediately afterward, reducing the “standing risk” to zero.
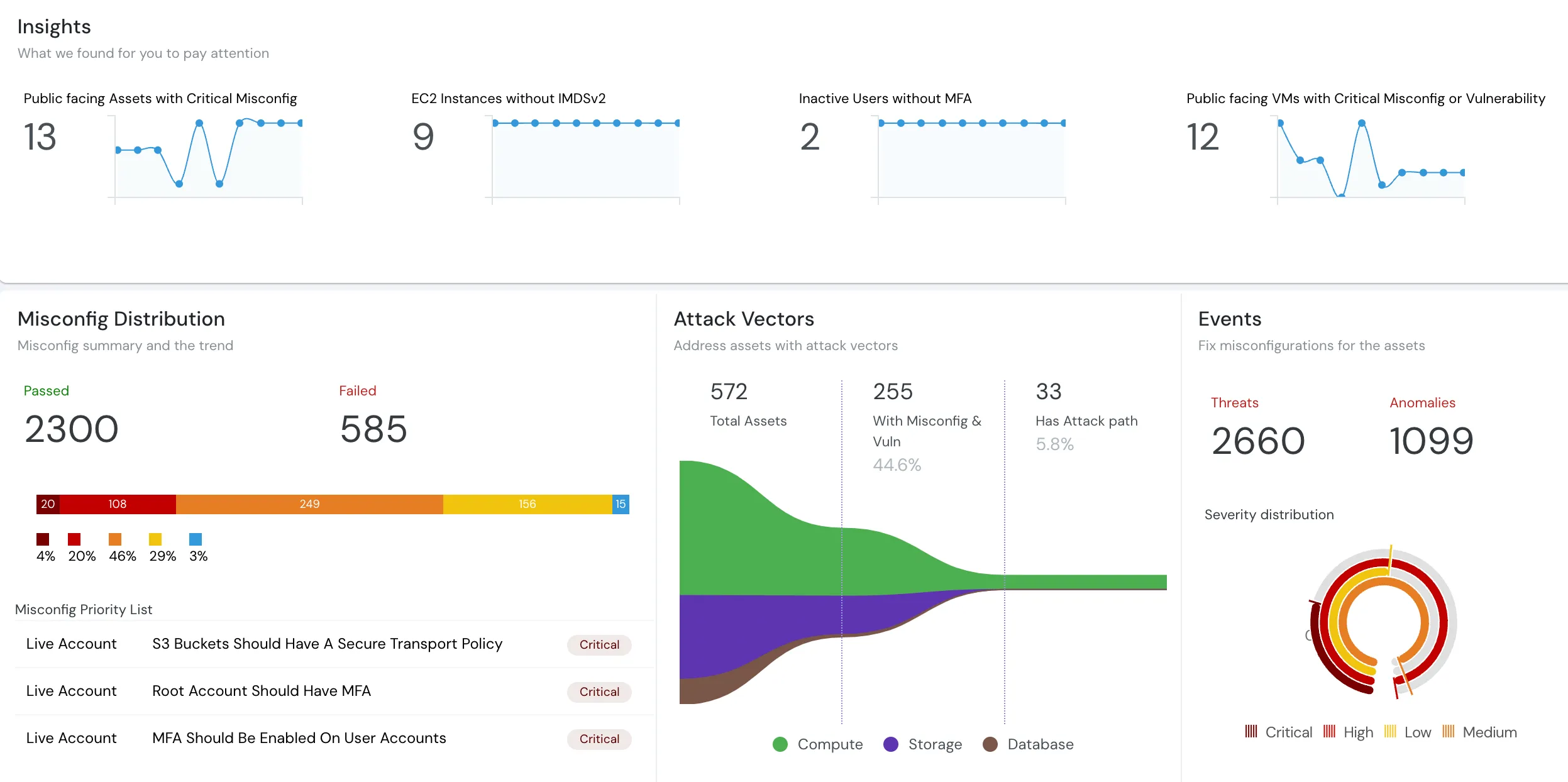
- CSPM & Code Security: Cloudanix’s platform continues to monitor the underlying AWS and Kubernetes infrastructure, identifying open ports and unidentified resources to ensure a clean security posture.
Check our solutions: DAM | IAM JIT | CSPM | Code Security | CNAPP
The Data Security Perspective
“For a Fintech company, data is our most valuable—and most sensitive—asset. Cloudanix DAM hasn’t just improved our visibility; it has given us control. The ability to mask data and prevent unauthorized queries in real-time is a game-changer for our compliance and customer trust.”
— Jiten Gala, President Engineering and Product, Kapittx
The Results: A Fortress for Financial AI
By moving to a data-first security model, Kapittx has successfully balanced AI innovation with enterprise-grade protection:
- Granular Governance: The ability to prevent specific people from executing high-risk queries has added a critical layer of safety to their production databases.
- Audit-Ready Data: With full DAM logs and JIT audit trails, Kapittx can prove compliance to its largest, most security-conscious customers instantly.
- Frictionless Scaling: Kapittx’s security team can now manage complex permissions and monitoring across their entire stack without manual overhead.
Customer Brief
- Customer: Kapittx
- Industry: Fintech / AR Software
- Tech Stack: AWS, Kubernetes, GitLab
- Primary SKU: Database Activity Monitoring (DAM)
- Supporting SKUs: JIT Cloud & DB, CSPM, Code Security
- Challenges: Permanent standing access & data security
- Key Impacts: Real-time data masking & query prevention. Automated privilege management & 100% audit readiness
