Security context, Events anomaly and Bulk reviews
Real-time Events Anomaly Support for GCP & AZURE and Signals in Notifications
This has been an awaited feature by many. We’re glad to announce it’s finally here. With real-time events anomaly alerts for GCP and Azure your cloud infrastructure is safer than ever. Suspicious behavior that you may miss seeing is automatically reported to you for correction. This feature is sure to bring you a good night’s sleep and lay your worries to rest.
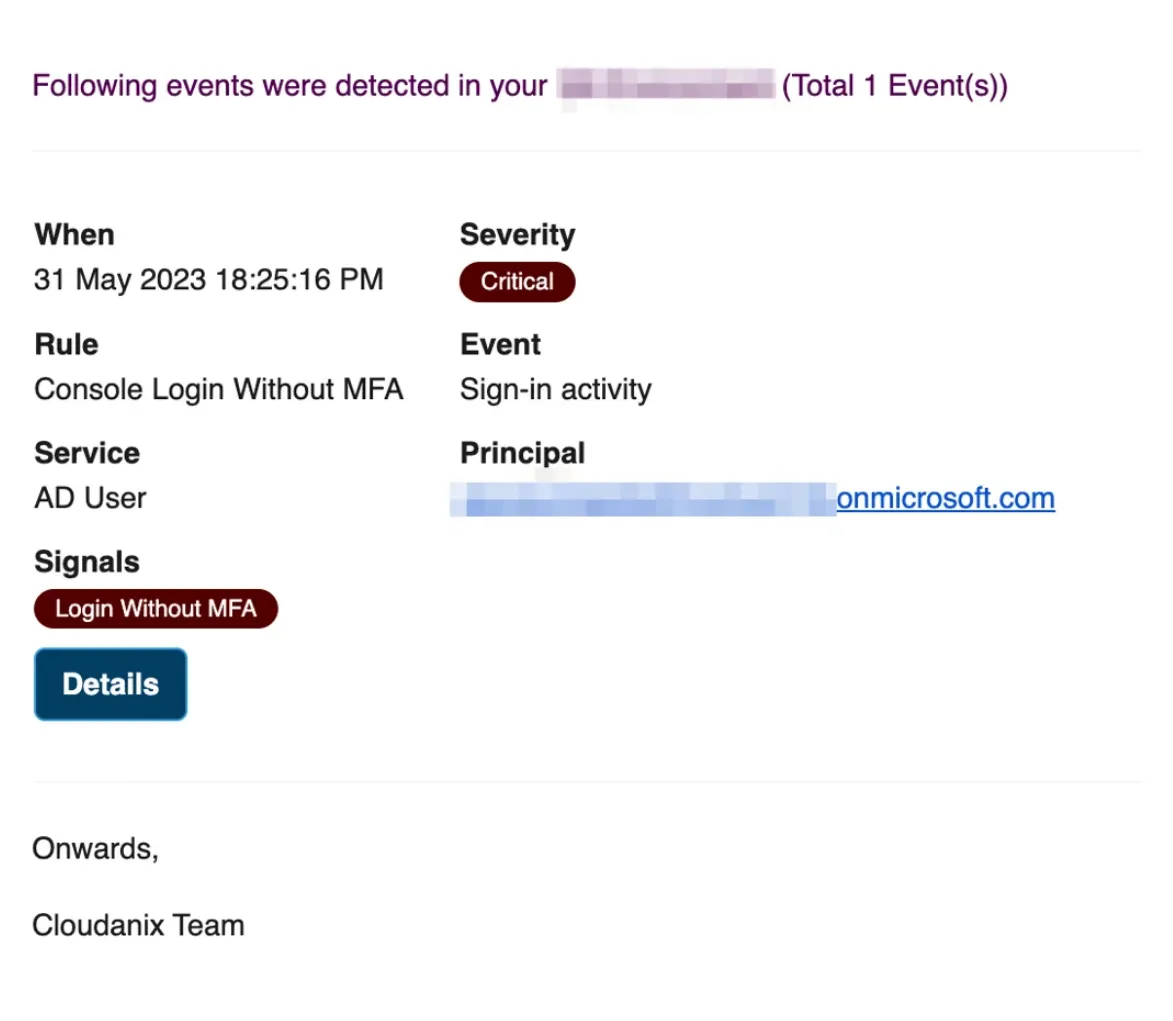
Events signal control dashboard
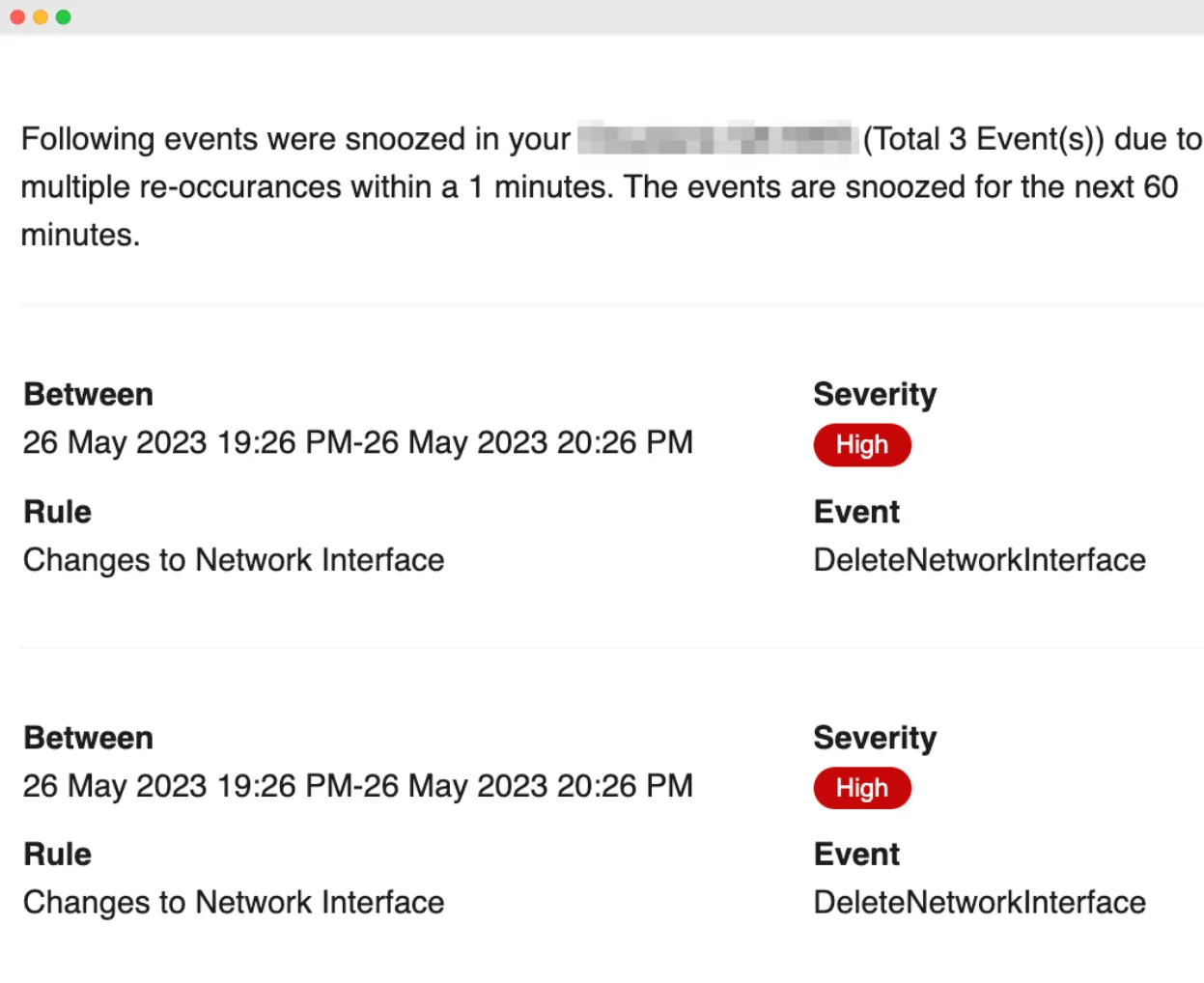
Auto Snooze to Avoid Alerts Fatigue
Don’t we all snooze our alarms every once in a while? Imagine your clock could snooze the days you want it to automatically and ring the other days when you need it to. Crazy right? This is enabled for you and visible in the email.
Event auto snooze feature - dashboard
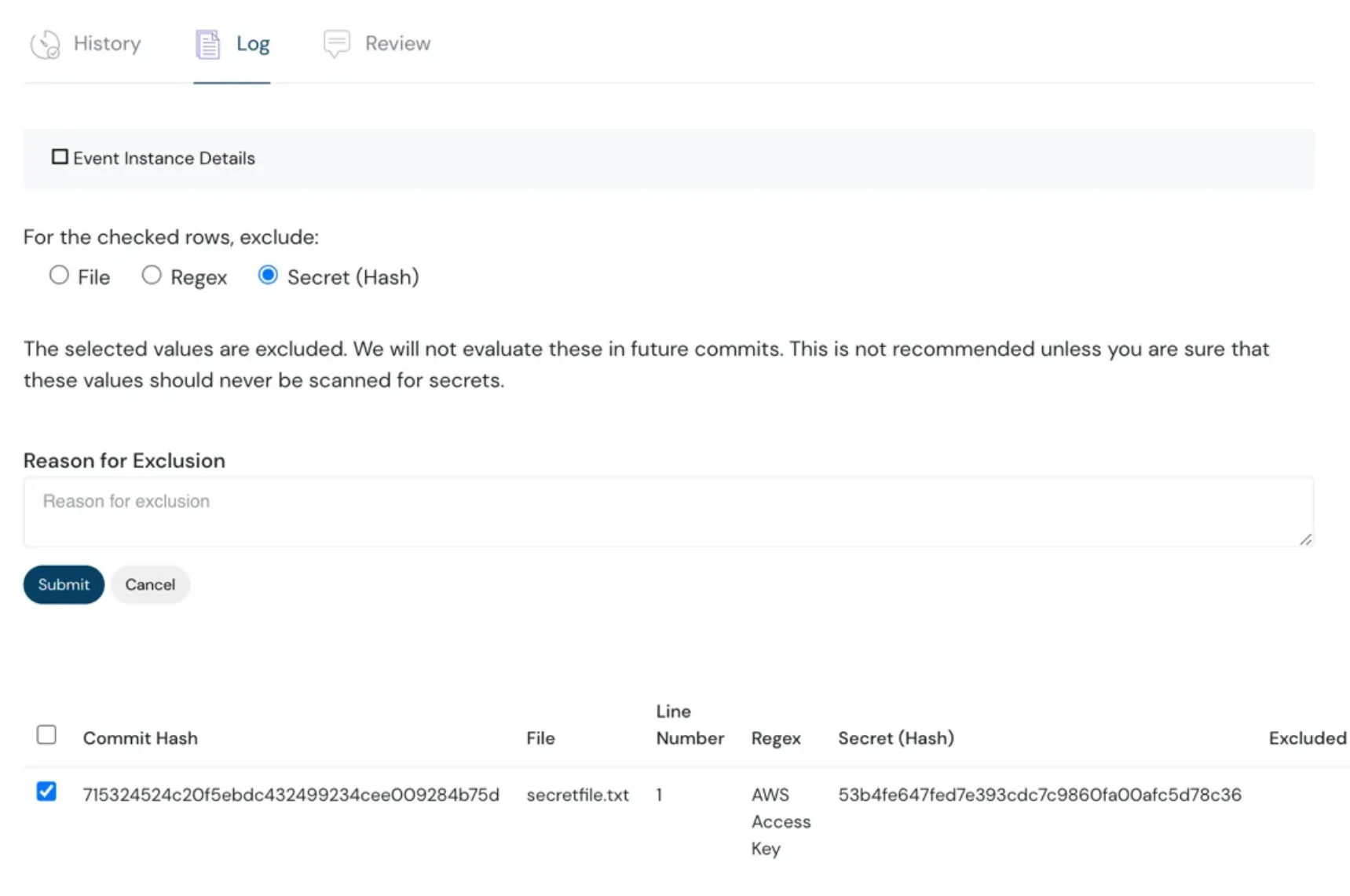
In Secret Scanning Capability – Support for Custom Patterns and Exclusions
Support for custom patterns and exclusions for existing patterns, files, or secrets.
This allows for more flexibility in identifying and managing secrets within files or code repositories. This feature enables organizations to tailor the secret scanning process to their specific needs and requirements.
Bulk Update of Events
This feature allows you to manage multiple events in a click rather than making individual updates to each event separately, saving you time and fatigue. This capability is particularly useful in scenarios where you need to apply a consistent change or modification across a large number of events simultaneously.
Bulk events feature - Cloudanix dashboard
Additional Updates
- Scan full repository for secrets in both Github and Bitbucket.
- Additional Events support for IAM in Azure (e.g., permissions updated for Service Account, User MFA changes, etc.)
Coming Soon
- Attack Path
- VM Security
TODO:// is not an option for Cloud Security**
Ready to see your graph?
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Friday, May 29, 2026
Best Wiz Alternatives in 2026: A Technical Side-by-Side Comparison for Security Teams
Wiz changed how the industry thinks about agentless cloud security. It also left four major surfaces uncovered. And in 2
Read MoreThursday, May 21, 2026
Cloud Asset Management: The Complete 2026 Guide for Multi-Cloud Teams
As we navigate through 2026, the role of the security leader has shifted from being a "gatekeeper" to becoming a strateg
Read MoreWednesday, May 20, 2026
Kubernetes Security Checklist 2026: Hardening EKS, AKS & GKE
The 2026 K8s Threat Landscape Kubernetes has become the backbone of modern cloud infrastructure, and attackers know
Read More