How to secure AWS IAM?
It takes one mistake on your part for a malicious actor to damage your brand!
MoreCloudanix
Comprehensive AWS cloud security auditing services to protect your entire cloud workload from misconfigurations and security vulnerabilities.
It takes one mistake on your part for a malicious actor to damage your brand!
MoreYour data needs highest level of protection. Cloudanix can provide that to you.
MoreProtect your EC2 and your entire Cloud workload
MoreProtect your Lambda and your entire Cloud workload
MoreProtect your S3 buckets, files and your entire Cloud workload
MoreProtect your data and your entire Cloud workload
MoreProtect your Elastic Load Balancers and your entire Cloud workload
MoreProtect your Elastic Search instances and your entire Cloud workload
MoreProtect your KMS and your entire Cloud workload
MoreProtect your EKS and your entire Cloud workload
MoreProtect your SES and your entire Cloud workload
MoreProtect your SNS and your entire Cloud workload
MoreProtect your SQS and your entire Cloud workload
MoreProtect your AWS API Gateway and your entire Cloud workload
MoreProtect your Cloudfront and your entire Cloud workload
MoreProtect your Cloudtrail and your entire Cloud workload
MoreProtect your Redshift instances and your entire Cloud workload
MoreProtect your Cloudformation and your entire Cloud workload
MoreProtect your Cloudwatch and your entire Cloud workload
MoreProtect your Route53 and your entire Cloud workload
MoreProtect your Network and your entire Cloud workload
MoreConnect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoCLOUDANIX
Explore guides, checklists, and blogs that simplify cloud security and help you secure your infrastructure.
Real-world success stories where Cloudanix helped organizations secure their cloud infrastructure. Watch how we made a difference across ind…
Read Case Studies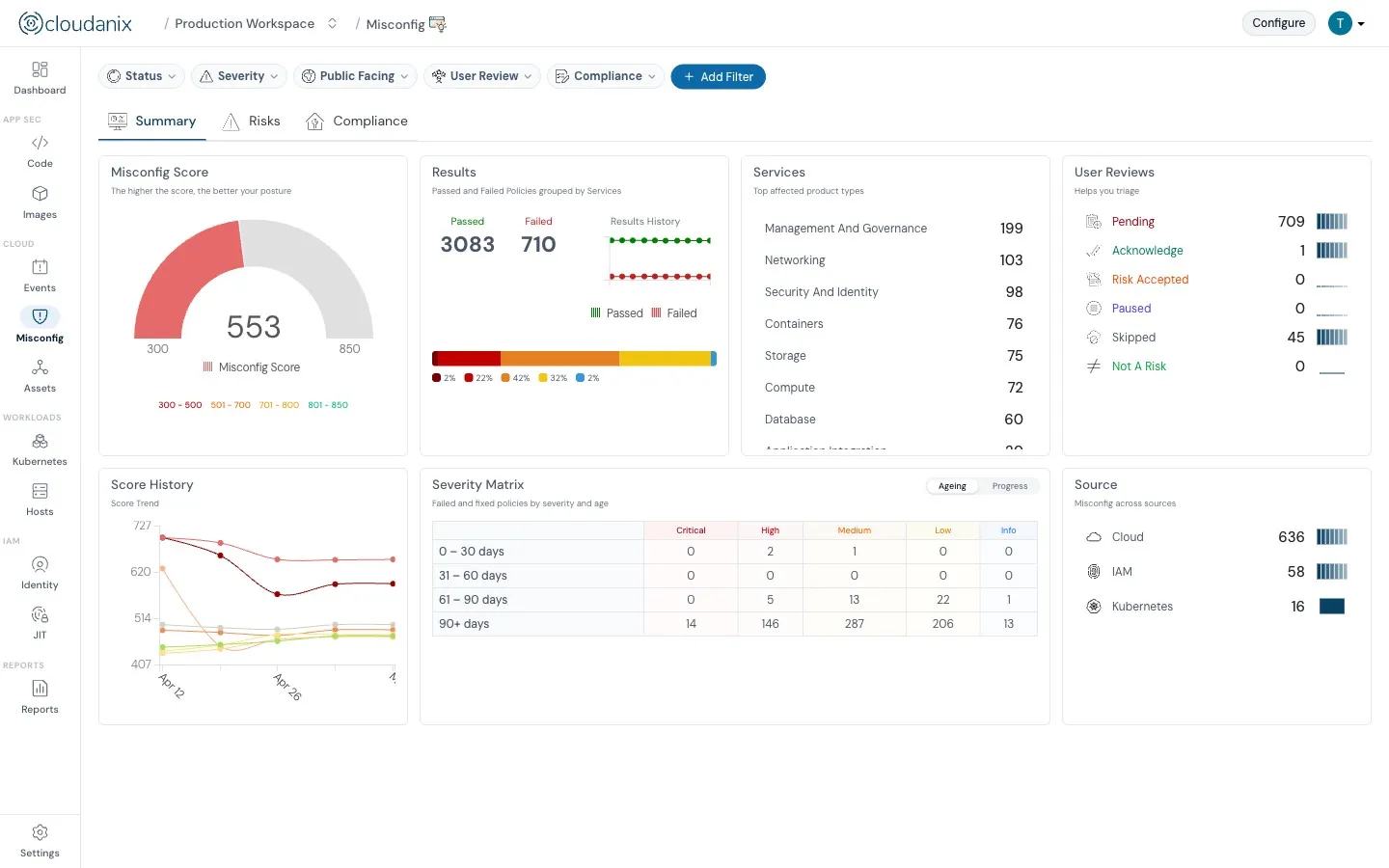
Understand what Cloud Security Posture Management (CSPM) is and how it automates security and compliance across cloud environments.
Read moreUnderstand how CASB, CSPM, and SIEM work together to enhance your cloud security posture and ensure better governance.
Read the blogIn-depth assessment of cloud environment for security, compliance, and optimization. Identify vulnerabilities, ensure data protection, and o…
Read the blogCloud environments are getting more complex and dynamic day by day, making it difficult to gain complete visibility into all assets and thei…
Read the blogCloudanix offers you a single dashboard to secure your workloads. Learn how to set up Cloudanix for your cloud platform from our documentati…
Take a lookA complete history of changes, improvements, and fixes for Cloudanix. Subscribe to get notified about the latest updates.
View Changelog