Attack Vector Enhancement, Image Security with Prioritization, Code Blocks and Workflows
January was a busy month for both the business and technical teams. At Cloudanix, we know that user experience is critical, especially for small teams aiming to achieve more with less. This update, shaped by customer feedback, focuses on efficiency and usability.
Guided Tours
We’ve introduced interactive Guided Tours across the platform, helping you navigate with ease and focus on the most critical insights. Designed to enhance learning and onboarding for new users.
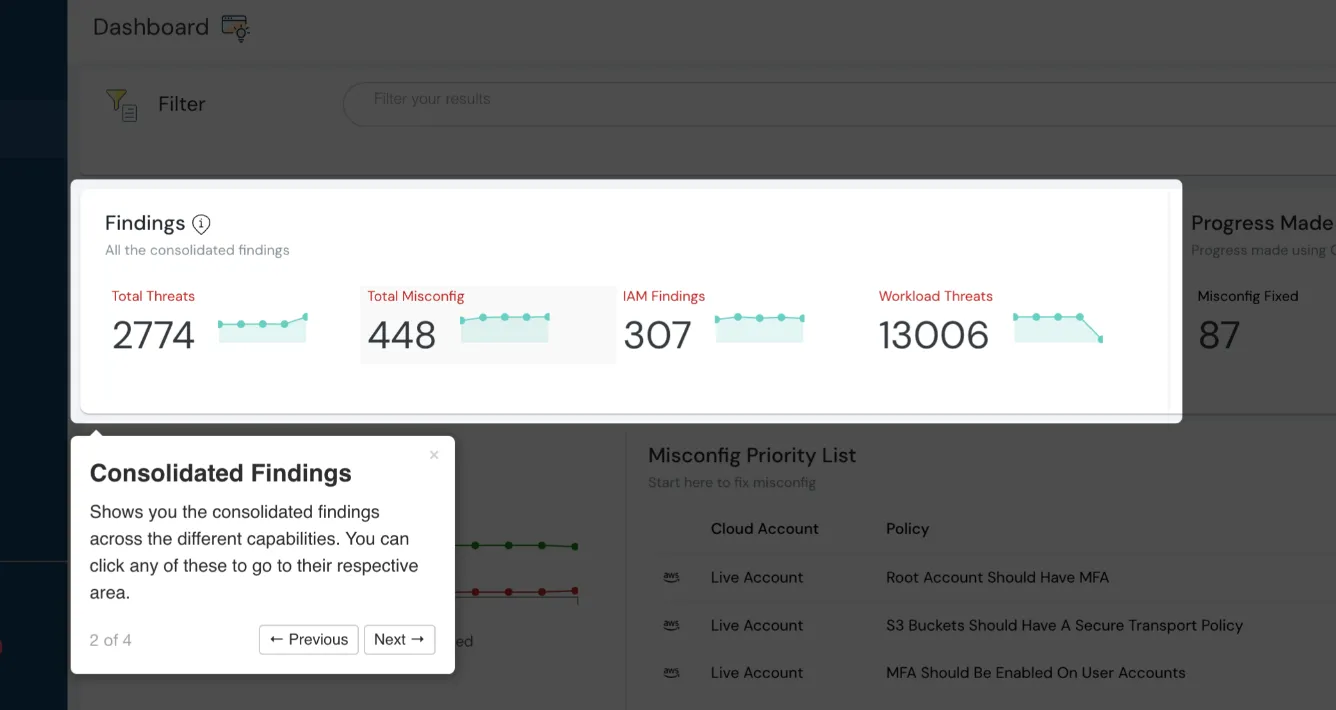
Consolidated findings at glance
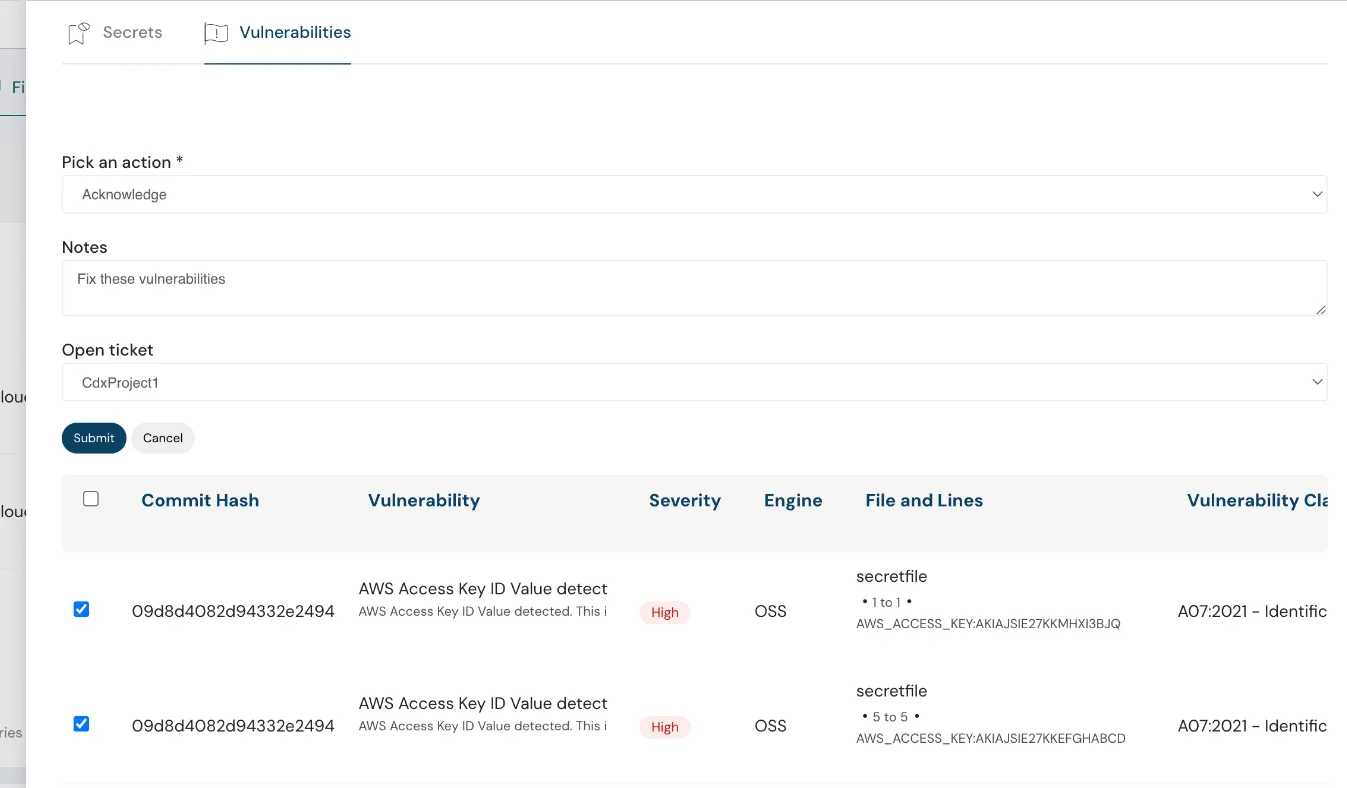
Code Blocks and Workflows
Code Security now displays code blocks affected by vulnerabilities and enables triaging via the new Review Capability, which includes:
- Pause
- Acknowledge
- Accept Risk
This allows security teams to manage findings more efficiently.
 Code security showcasing affected vulnerabilities
Code security showcasing affected vulnerabilities
 Code security feature open ticket option
Code security feature open ticket option
Time-Based Filters for Events
Events, Threats & Anomalies now support a Time-based “Events Since” filter, allowing you to quickly view and analyze recent activity for faster response.
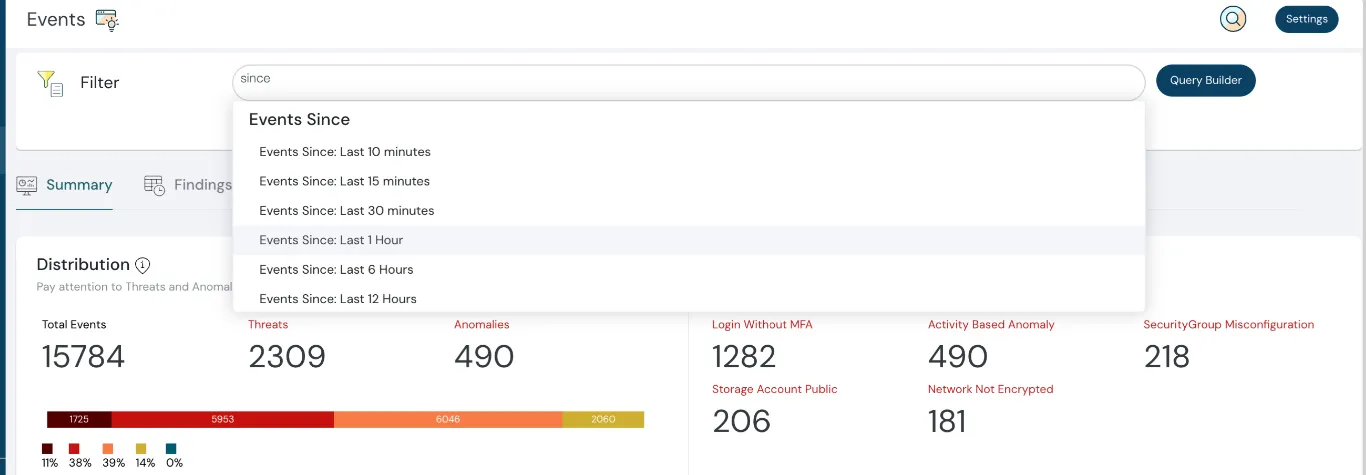 Events based filters now available
Events based filters now available
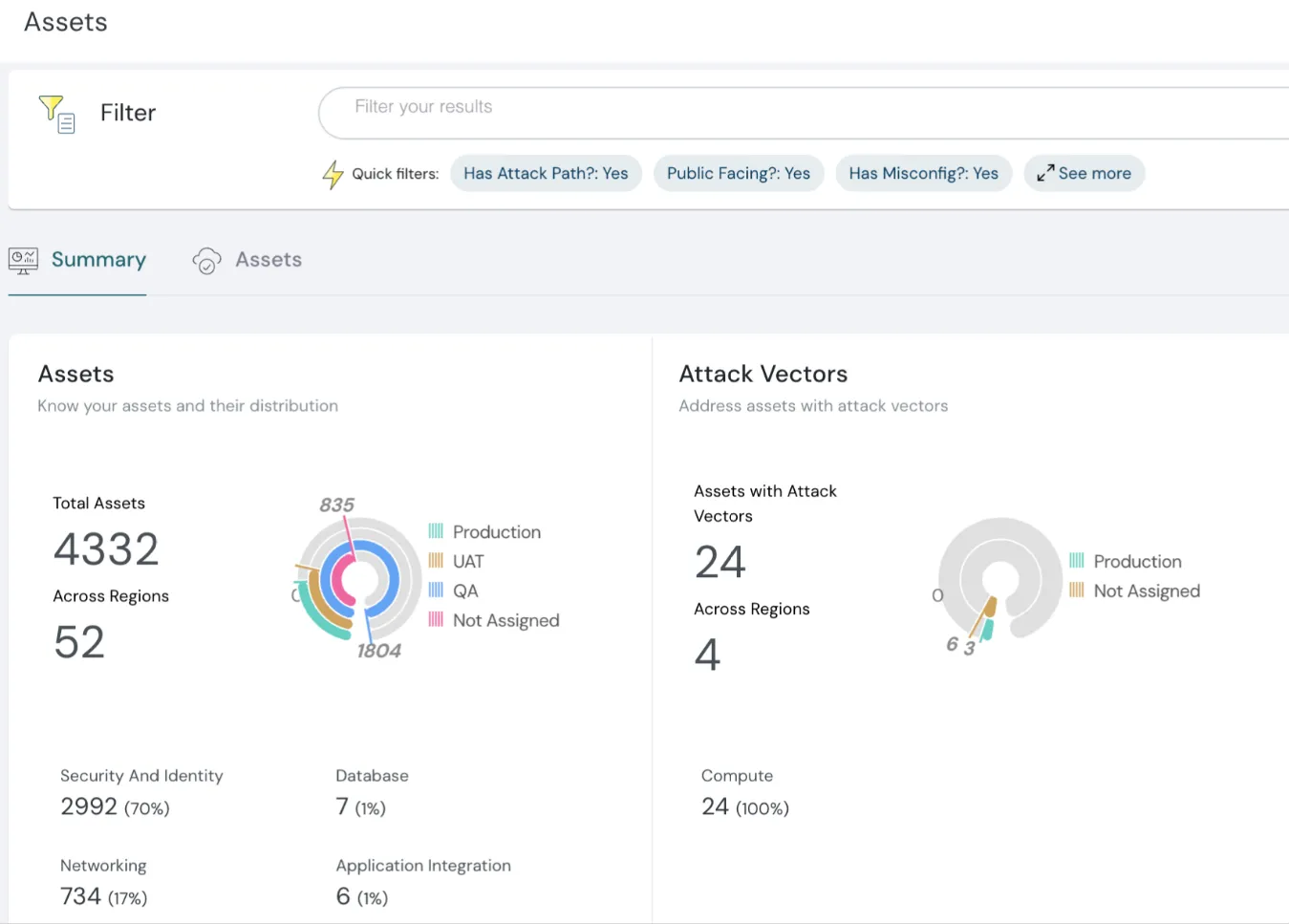
Attack Vectors Include Subdomain Findings
Attack Vectors are now extended to include findings from vulnerable subdomains, broadening visibility into potential attack surfaces.
 Assets with attack vectors
Assets with attack vectors
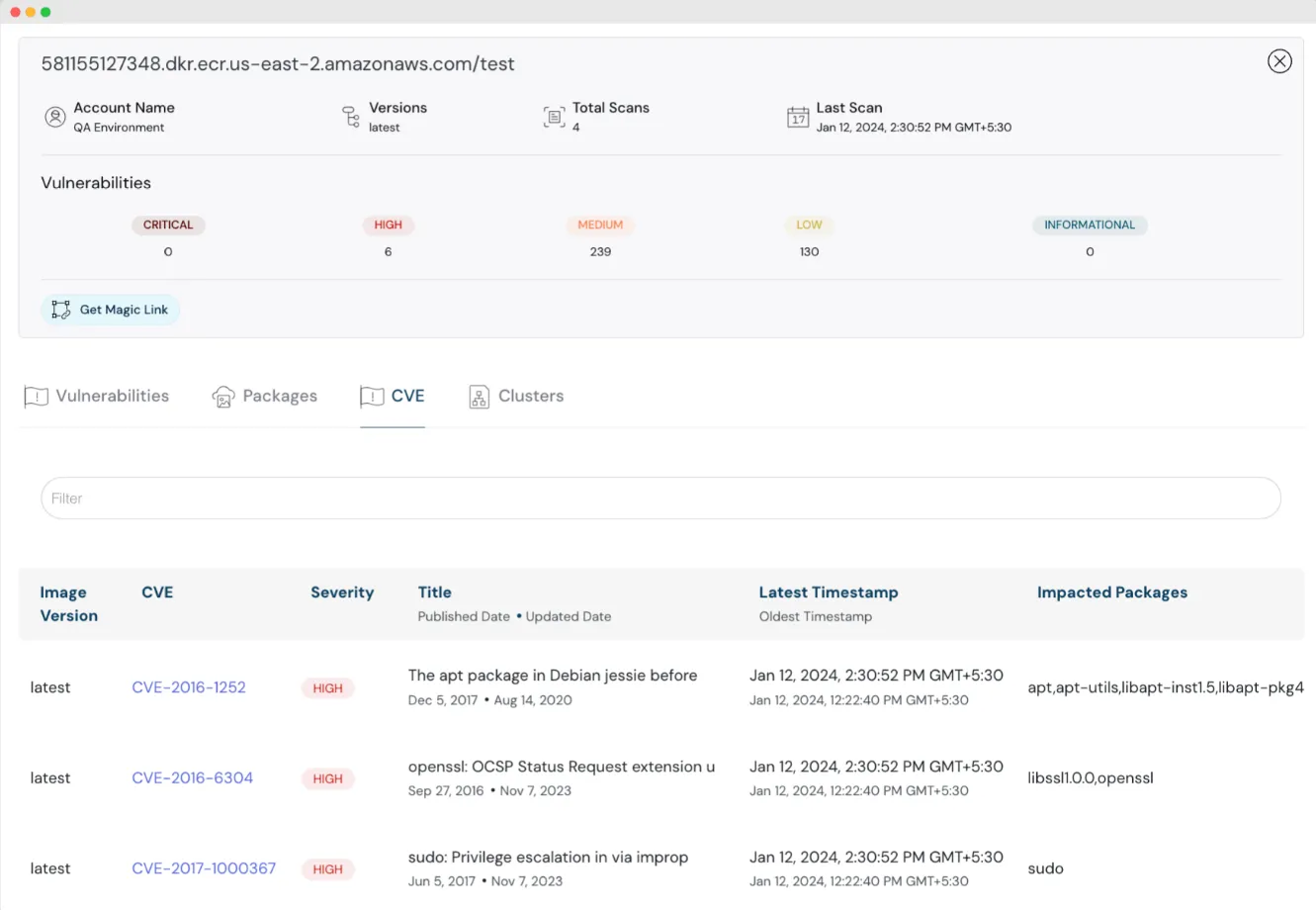
Image Security Prioritization
Image Security now supports grouping findings by vulnerabilities, packages, and CVEs, along with active cluster usage data, enabling prioritization of remediation.
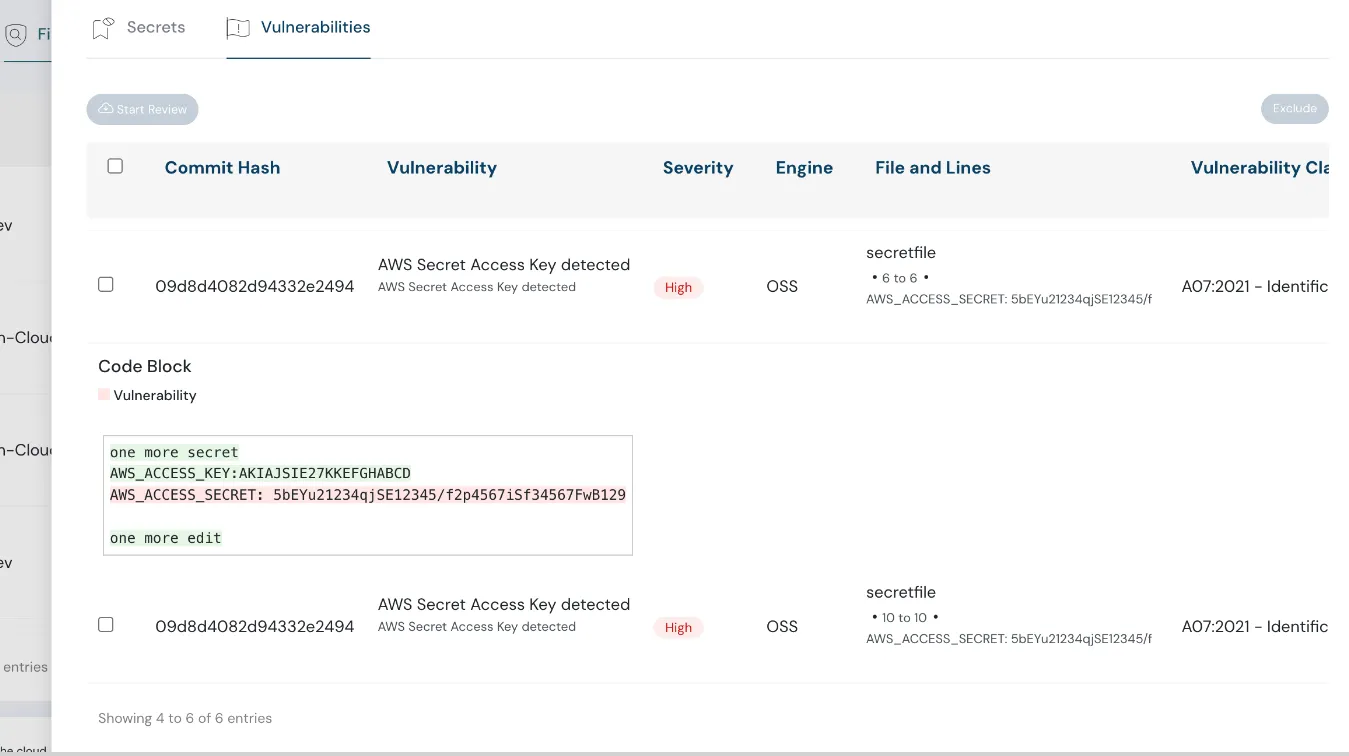 Image security is more enhanced
Image security is more enhanced
Multiple and Area-Specific Jira Projects
Cloudanix now integrates with multiple Jira projects, allowing you to assign specific projects to specific capabilities (e.g., code security vs. misconfiguration). This improves task organization and streamlines workflows.
Cloudanix Blogs
- AWS & Cloudanix: Real-Time Threat and Anomaly Detection for Workloads on AWS
- AWS & Cloudanix: How Cloudanix Secures Containerized Applications Running on Amazon EKS
- Launching Cloud Console Link Open Source Project
Additional Resources
Industry News
- AWS to Charge for Public IPv4 from Feb 01
- Azure Attack Paths
- AWS re:Invent Security Recap
- Securing Google Cloud Admins
- Dependency Confusion Supply Chain Attack
TODO:// is not an option for Cloud Security
Ready to see your graph?
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Wednesday, Apr 29, 2026
Code Security Best Practices for DevSecOps Teams in 2026
In 2026, the speed of software development has reached a point where traditional security methods can no longer keep up.
Read MoreWednesday, Apr 29, 2026
Integrating Security into Every Stage: A Blueprint for Secure Software Development
The escalating frequency and severity of software vulnerabilities exploited in the wild forced a paradigm shift in how a
Read MoreTuesday, Apr 14, 2026
Top 15 Cloud Misconfigurations in 2026 - How to Fix Them?
Most cloud breaches today are not the result of sophisticated zero-day exploits. They are the result of misconfiguration
Read More