Request Temporary Access
Partner requests access to a specific customer resource (Cloud console, Database, VM, or Kubernetes cluster) via Cloudanix JIT portal.
SECURE ACCESS PROGRAM
Partners use Cloudanix JIT (Just-In-Time) access to securely access customer environments — eliminating process overhead, reducing risk of mistakes, and removing training and paperwork burden. Customers happily grant access with zero friction. Up to 5 free JIT seats per customer.
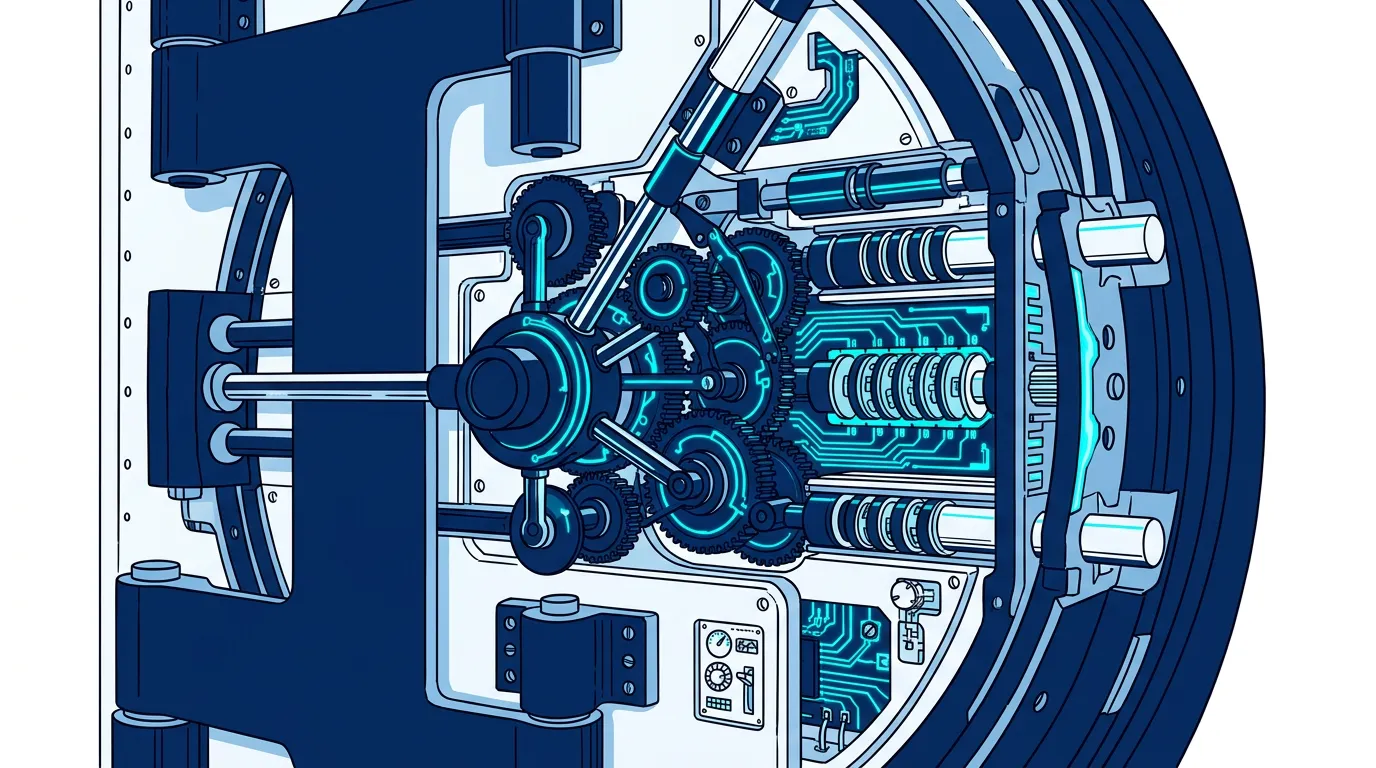
HOW IT WORKS
Cloudanix JIT eliminates the friction of accessing customer environments — no standing privileges, no paperwork, full audit trail.
Partner requests access to a specific customer resource (Cloud console, Database, VM, or Kubernetes cluster) via Cloudanix JIT portal.
Customer receives the request and approves with a single click. No forms, no tickets, no training required.
Access is granted for the requested duration only. When time is up, access is automatically revoked — no standing privileges, ever.
Every access request, approval, and action is logged. Complete audit trail for compliance — no manual tracking needed.
Eliminate Third-Party Risk
Accessing customer environments is one of the biggest friction points for partners. Cloudanix JIT eliminates it entirely.
Customer Voice
One day, I changed the password of a root account, and my CTO called me within less than a minute to confirm if I did so. I was not expecting a reaction this quick. He told me Cloudanix alerted him of this password change and that he wanted to confirm as it was a critical security notification. I couldn't believe it!

Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoCLOUDANIX PARTNERS
Explore resources to help you succeed as a Cloudanix partner.
See how partners and customers leverage Cloudanix to secure cloud environments, achieve compliance, and drive business outcomes.
Read Case StudiesExplore our structured GTM programs designed to help partners generate revenue and win customers with concrete business cases.
View ProgramsAccess technical documentation, integration guides, and platform walkthroughs to get up to speed quickly.
View DocumentationStay updated with the latest features, improvements, and capabilities added to the Cloudanix platform.
View ChangelogRead insights on cloud security trends, partner success stories, and best practices from the Cloudanix team.
Read Blog