KMS Keys Should Not Be Exposed
Any publicly accessible AWS Key Management Service master keys should be identified and their access policy should be updated in order to stop any unsigned requests made to these resources.
Cloudanix
Any publicly accessible AWS Key Management Service master keys should be identified and their access policy should be updated in order to stop any unsigned requests made to these resources.
Any publicly accessible AWS Key Management Service master keys should be identified and their access policy should be updated in order to stop any unsigned requests made to these resources.
When you enable automatic key rotation, AWS KMS rotates the CMK 365 days after the enable date and every 365 days thereafter.
Any disabled KMS Customer Master Keys in your AWS account should be removed in order to lower the cost of your monthly AWS bill.
KMS key policies should be designed to limit the number of users who can perform encrypt and decrypt operations. Each application should use its own key to avoid over exposure.
Any disabled AWS KMS Customer Master Keys (CMK) that have been accidentally or intentionally scheduled for deletion should be recovered in order to prevent losing any data encrypted with these keys.
There should be one Amazon KMS Customer Master Key (CMK) created in your AWS account for the app tier in order to protect data that transits your AWS application stack, have full control over encryption process, and meet security and compliance requirements.
There should be one Amazon KMS Customer Master Key (CMK) created in your AWS account for the database tier in order to protect data-at-rest available within your AWS web stack, have full control over encryption/decryption process, and meet security and compliance requirements.
Ensure that a specific list of AWS KMS Customer Master Keys (CMKs) are available for use in your AWS account in order to meet strict security and compliance requirements in your organization.
All your AWS Key Management Service keys should be configured to be accessed only by trusted AWS accounts in order to protect against unauthorized cross account access. This will help prevent data breaches and loss.
You should have KMS CMK customer-managed keys in use in your account instead of AWS managed-keys in order to have full control over your data encryption and decryption process.
There should be one Amazon KMS Customer Master Key (CMK) created in your AWS account for the web tier in order to protect data that transits your AWS web stack, have full control over data encryption/decryption process, and meet compliance requirements.
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoCLOUDANIX
Explore guides, checklists, and blogs that simplify cloud security and help you secure your infrastructure.
Real-world success stories where Cloudanix helped organizations secure their cloud infrastructure. Watch how we made a difference across ind…
Read Case Studies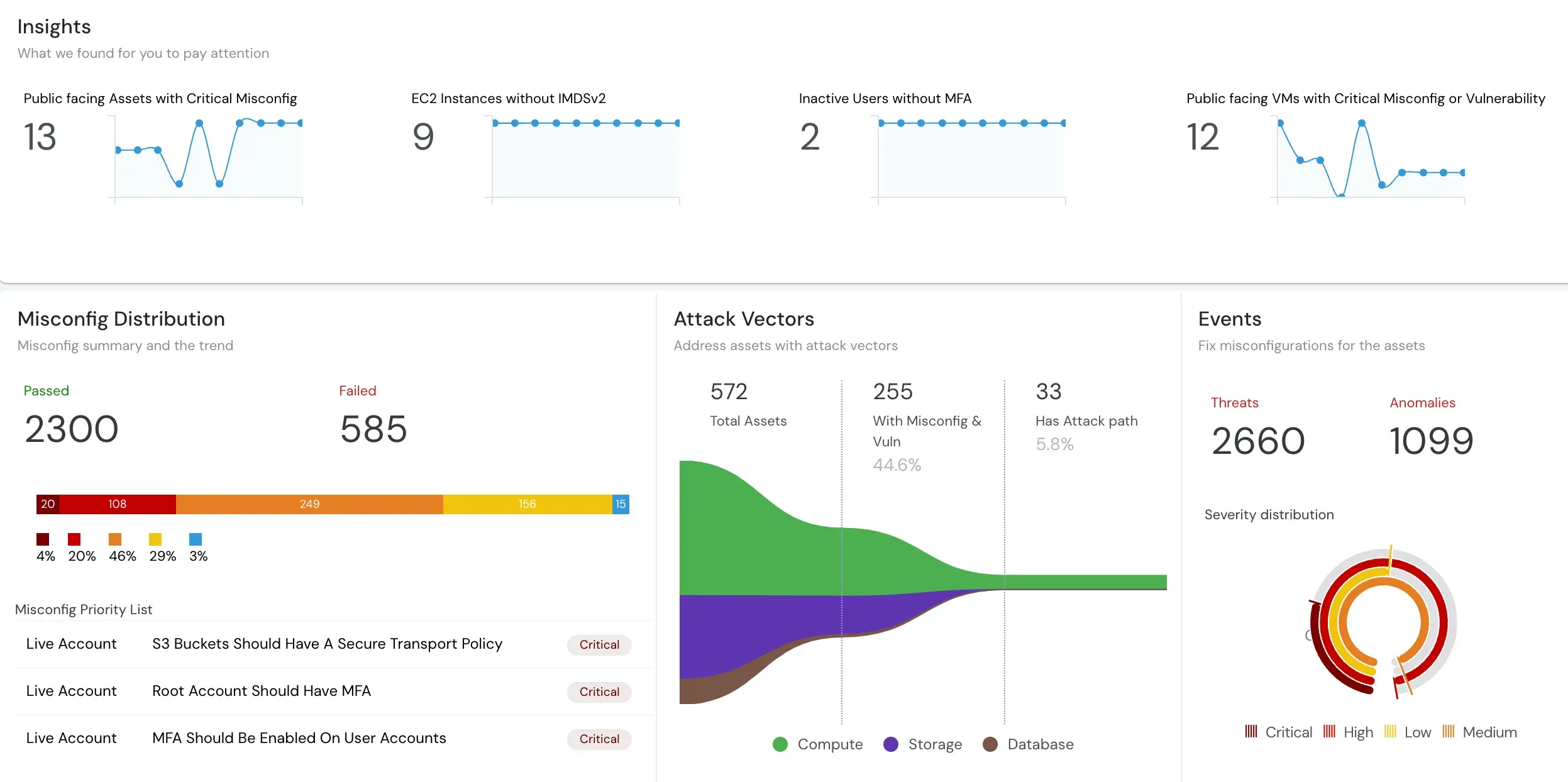
Understand what Cloud Security Posture Management (CSPM) is and how it automates security and compliance across cloud environments.
Read moreUnderstand how CASB, CSPM, and SIEM work together to enhance your cloud security posture and ensure better governance.
Read the blogIn-depth assessment of cloud environment for security, compliance, and optimization. Identify vulnerabilities, ensure data protection, and o…
Read the blogCloud environments are getting more complex and dynamic day by day, making it difficult to gain complete visibility into all assets and thei…
Read the blogCloudanix offers you a single dashboard to secure your workloads. Learn how to set up Cloudanix for your cloud platform from our documentati…
Take a lookA complete history of changes, improvements, and fixes for Cloudanix. Subscribe to get notified about the latest updates.
View Changelog