Web Dashboard Should Be Disabled
Ensures all Kubernetes clusters have the web dashboard disabled. It is recommended to disable the web dashboard because it is backed by a highly privileged service account.
Cloudanix
Ensures all Kubernetes clusters have the web dashboard disabled. It is recommended to disable the web dashboard because it is backed by a highly privileged service account.
Ensures all Kubernetes clusters have the web dashboard disabled. It is recommended to disable the web dashboard because it is backed by a highly privileged service account.
Ensures the private endpoint setting is enabled for kubernetes clusters. Kubernetes private endpoints can be used to route all traffic between the Kubernetes worker and control plane nodes over a private VPC endpoint rather than across the public internet.
Ensures private cluster is enabled for all Kubernetes clusters. Kubernetes private clusters only have internal ip ranges, which ensures that their workloads are isolated from the public internet.
Ensures pod security policy is enabled for all Kubernetes clusters. Kubernetes pod security policy is a resource that controls security sensitive aspects of the pod configuration.
Ensures all Kubernetes clusters have network policy enabled. Kubernetes network policy creates isolation between cluster pods, this creates a more secure environment with only specified connections allowed.
Ensures all Kubernetes clusters have monitoring enabled.
Ensures master authorized networks is set to enabled on Kubernetes clusters
Ensures all Kubernetes clusters have logging enabled. This setting should be enabled to ensure Kubernetes control plane logs are properly recorded.
Ensure legacy authorization is set to disabled on Kubernetes clusters. The legacy authorizer in Kubernetes grants broad, statically defined permissions.
Ensure Kubernetes cluster nodes do use the default service account. Kubernetes cluster nodes should use customized service accounts that have minimal privileges to run. This reduces the attack surface in the case of a malicious attack on the cluster.
Ensures all Kubernetes cluster nodes have Container-Optimized OS enabled. Container-Optimized OS is optimized to enhance node security. It is backed by a team at Google that can quickly patch it.
Ensures Kubernetes clusters are created with limited service account access scopes. Kubernetes service accounts should be limited in scope to the services necessary to operate the clusters.
Ensure basic authentication is set to disabled on Kubernetes clusters.
Ensures all Kubernetes cluster nodes have automatic upgrades enabled. Enabling automatic upgrades on nodes ensures that each node stays current with the latest version of the master branch, also ensuring that the latest security patches are installed to provide the most secure environment.
Ensures all Kubernetes cluster nodes have automatic repair enabled. When automatic repair on nodes is enabled, the Kubernetes engine performs health checks on all nodes, automatically repairing nodes that fail health checks. This ensures that the Kubernetes environment stays optimal.
Ensures all Kubernetes clusters have alias IP ranges enabled. Alias IP ranges allow users to assign ranges of internal IP addresses as alias to a network interface.
Ensure that node pool autoscaling is enabled
Ensure that boot disk on k8 node pools are encrypted with CMK
Ensure that kubernetes node pools have Integrity Monitoring enabled
Ensure that kubernetes node pools have secure boot enabled
Ensure that shielded nodes are used in node pools
Ensure that cluster autoscaling profile is set to OPTIMIZE_UTILIZATION or BALANCED for optimal resource utilization
Ensure that the endpoint of cluster master in not public
Ensure that the kubernetes version is up to date
Kubernetes provides the option to use client certificates for user authentication. However as there is no way to revoke these certificates when a user leaves an organization or loses their credential, they are not suitable for this purpose. It is not possible to fully disable client certificate use within a cluster as it is used for component to component authentication.
Scan images stored in Google Container Registry (GCR) for vulnerabilities.
Configure the Cluster Service Account with Storage Object Viewer Role to only allow readonly access to GCR.
Use Binary Authorization to allowlist (whitelist) only approved container registries
Create and use minimally privileged Service accounts to run GKE cluster nodes instead of using the Compute Engine default Service account. Unnecessary permissions could be abused in the case of a node compromise.
Kubernetes workloads should not use cluster node service accounts to authenticate to Google Cloud APIs. Each Kubernetes Workload that needs to authenticate to other Google services using Cloud IAM should be provisioned a dedicated Service account. Enabling Workload Identity manages the distribution and rotation of Service account keys for the workloads to use.
Encrypt Kubernetes secrets, stored in etcd, at the application-layer using a customermanaged key in Cloud KMS.
Disable the legacy GCE instance metadata APIs for GKE nodes. Under some circumstances, these can be used from within a pod to extract the node's credentials
Running the GKE Metadata Server prevents workloads from accessing sensitive instance metadata and facilitates Workload Identity
Subscribe to the Regular or Stable Release Channel to automate version upgrades to the GKE cluster and to reduce version management complexity to the number of features and level of stability required.
Enable Integrity Monitoring for Shielded GKE Nodes to be notified of inconsistencies during the node boot sequence.
Enable VPC Flow Logs and Intranode Visibility to see pod-level traffic, even for traffic within a worker node.
Create Alias IPs for the node network CIDR range in order to subsequently configure IPbased policies and firewalling for pods. A cluster that uses Alias IPs is called a 'VPC-native' cluster
Send logs and metrics to a remote aggregator to mitigate the risk of local tampering in the event of a breach.
Disable Client Certificates, which require certificate rotation, for authentication. Instead, use another authentication method like OpenID Connect.
Cluster Administrators should leverage G Suite Groups and Cloud IAM to assign Kubernetes user roles to a collection of users, instead of to individual emails using only Cloud IAM.
The Kubernetes Web UI (Dashboard) has been a historical source of vulnerability and should only be deployed when necessary.
Alpha clusters are not covered by an SLA and are not production-ready.
Use GKE Sandbox to restrict untrusted workloads as an additional layer of protection when running in a multi-tenant environment.
Binary Authorization helps to protect supply-chain security by only allowing images with verifiable cryptographically signed metadata into the cluster.
GKE cluster should schedule maintenance windows and exclusions to upgrade predictability and to align updates with off-peak business hours.
GKE cluster should be proactively receive updates about GKE upgrades and GKE versions
Control Plane endpoint access should be limited to authorized networks only
GKE cluster should be regional for maximum availability of control plane during upgrades and zonal outages
GKE cluster should use GKE L4 ILB Subsetting if nodes > 250
GKE cluster should have Network Policies or Dataplane V2 enabled
GKE cluster should use node local DNS cache
GKE node pools should be regional (multiple zones) for maximum nodes availability during zonal outages
GKE cluster should have Workload Identity enabled
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoCLOUDANIX
Explore guides, checklists, and blogs that simplify cloud security and help you secure your infrastructure.
Real-world success stories where Cloudanix helped organizations secure their cloud infrastructure. Watch how we made a difference across ind…
Read Case Studies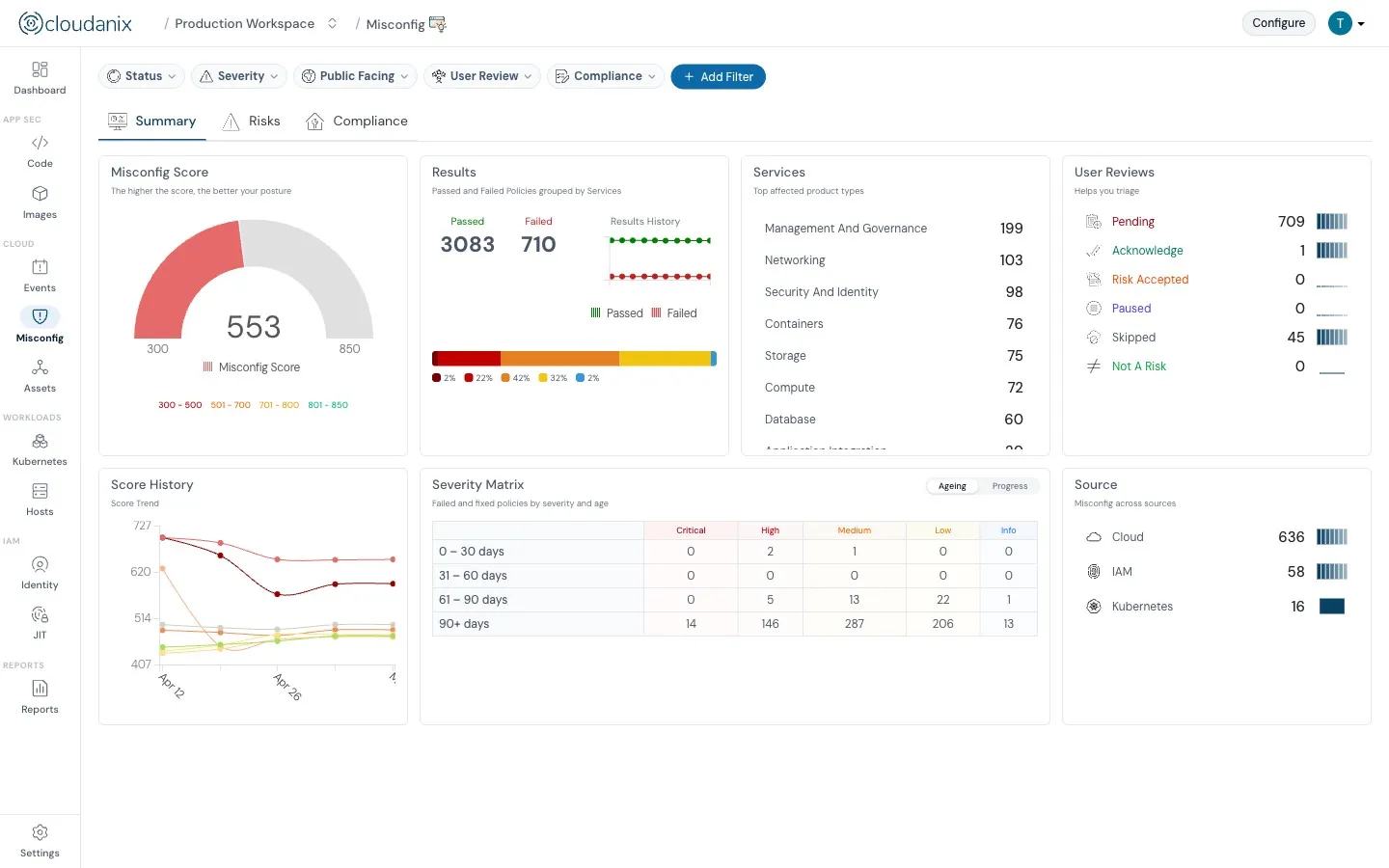
Understand what Cloud Security Posture Management (CSPM) is and how it automates security and compliance across cloud environments.
Read moreUnderstand how CASB, CSPM, and SIEM work together to enhance your cloud security posture and ensure better governance.
Read the blogIn-depth assessment of cloud environment for security, compliance, and optimization. Identify vulnerabilities, ensure data protection, and o…
Read the blogCloud environments are getting more complex and dynamic day by day, making it difficult to gain complete visibility into all assets and thei…
Read the blogCloudanix offers you a single dashboard to secure your workloads. Learn how to set up Cloudanix for your cloud platform from our documentati…
Take a lookA complete history of changes, improvements, and fixes for Cloudanix. Subscribe to get notified about the latest updates.
View Changelog