Guest Users in Use
Avoid creating guest users, as they are typically added outside your employee on-boarding/off-boarding process and could potentially be overlooked indefinitely leading to a potential vulnerability.
Cloudanix
Avoid creating guest users, as they are typically added outside your employee on-boarding/off-boarding process and could potentially be overlooked indefinitely leading to a potential vulnerability.
Avoid creating guest users, as they are typically added outside your employee on-boarding/off-boarding process and could potentially be overlooked indefinitely leading to a potential vulnerability.
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoCLOUDANIX
Explore guides, checklists, and blogs that simplify cloud security and help you secure your infrastructure.
Real-world success stories where Cloudanix helped organizations secure their cloud infrastructure. Watch how we made a difference across ind…
Read Case Studies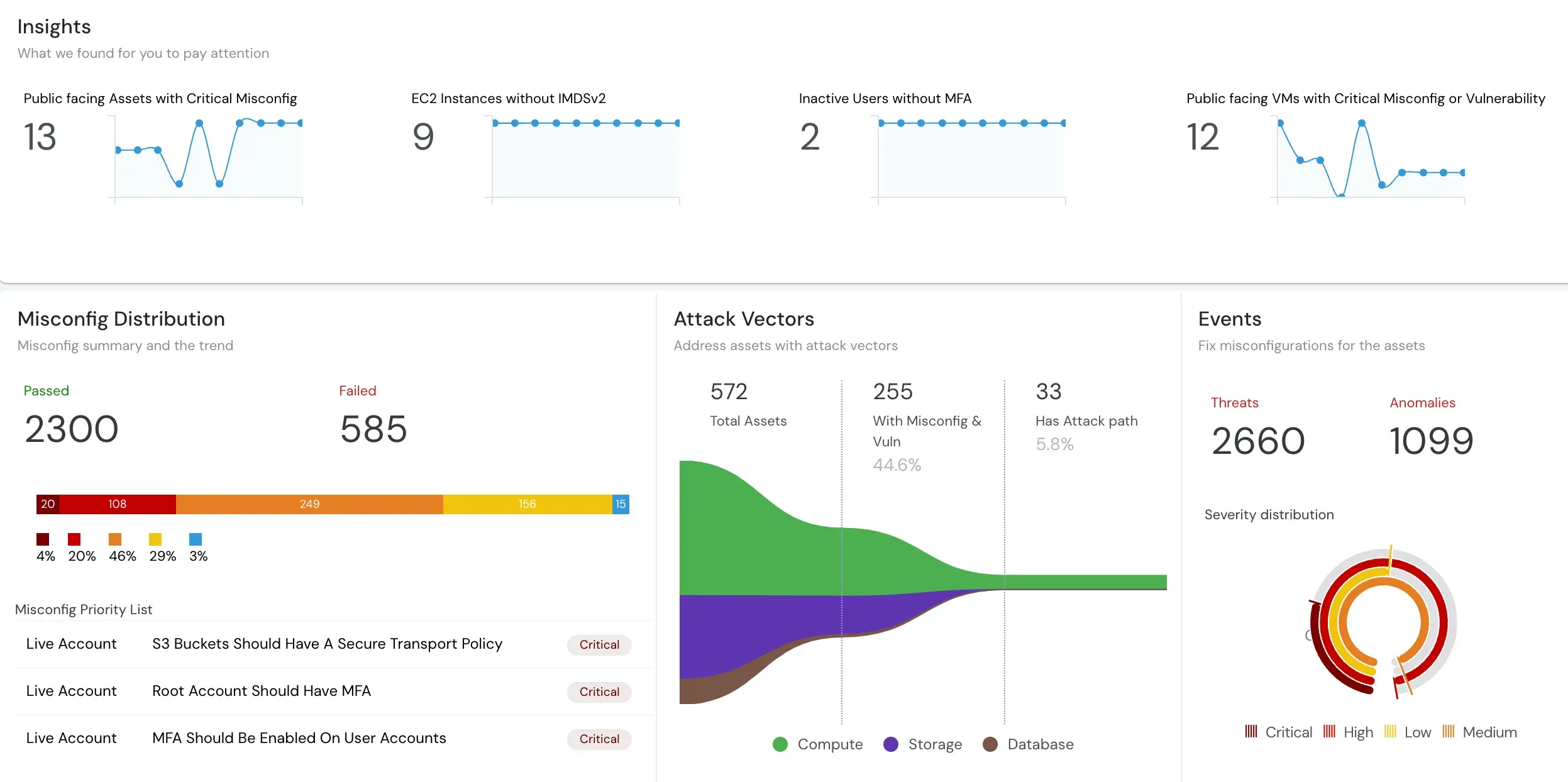
Understand what Cloud Security Posture Management (CSPM) is and how it automates security and compliance across cloud environments.
Read moreUnderstand how CASB, CSPM, and SIEM work together to enhance your cloud security posture and ensure better governance.
Read the blogIn-depth assessment of cloud environment for security, compliance, and optimization. Identify vulnerabilities, ensure data protection, and o…
Read the blogCloud environments are getting more complex and dynamic day by day, making it difficult to gain complete visibility into all assets and thei…
Read the blogCloudanix offers you a single dashboard to secure your workloads. Learn how to set up Cloudanix for your cloud platform from our documentati…
Take a lookA complete history of changes, improvements, and fixes for Cloudanix. Subscribe to get notified about the latest updates.
View Changelog