Just In Time access is a Zero Trust security approach that grants users temporary, time-bound permissions only when needed. Instead of permanent standing privileges, users request access for specific resources which automatically expires after use. This dramatically reduces your attack surface and eliminates the risks of permanent over-privileged accounts.
Cloudanix JIT can be integrated with your IAM, Identity Center, or cloud provider setup in approximately 30 minutes. The deployment requires no changes to your existing tooling or workflows, making adoption seamless for your teams. You can start with a pilot group and expand gradually.
Yes, Cloudanix JIT is ideal for managing third-party access. You can grant temporary access to vendors and contractors without creating permanent accounts or sharing long-term credentials. Every access request, approval, and action is logged, giving you complete visibility into vendor activities for compliance and security.
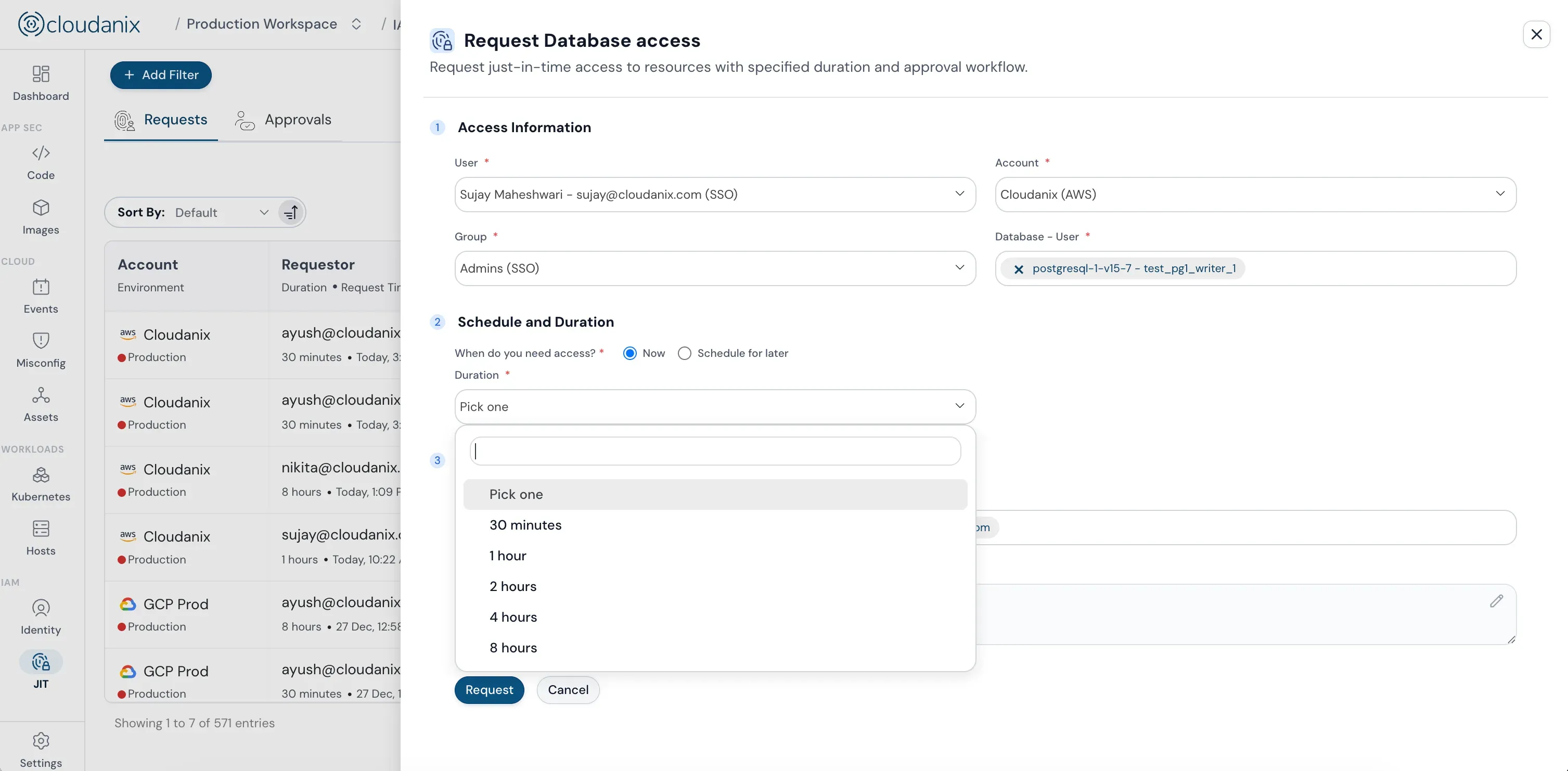
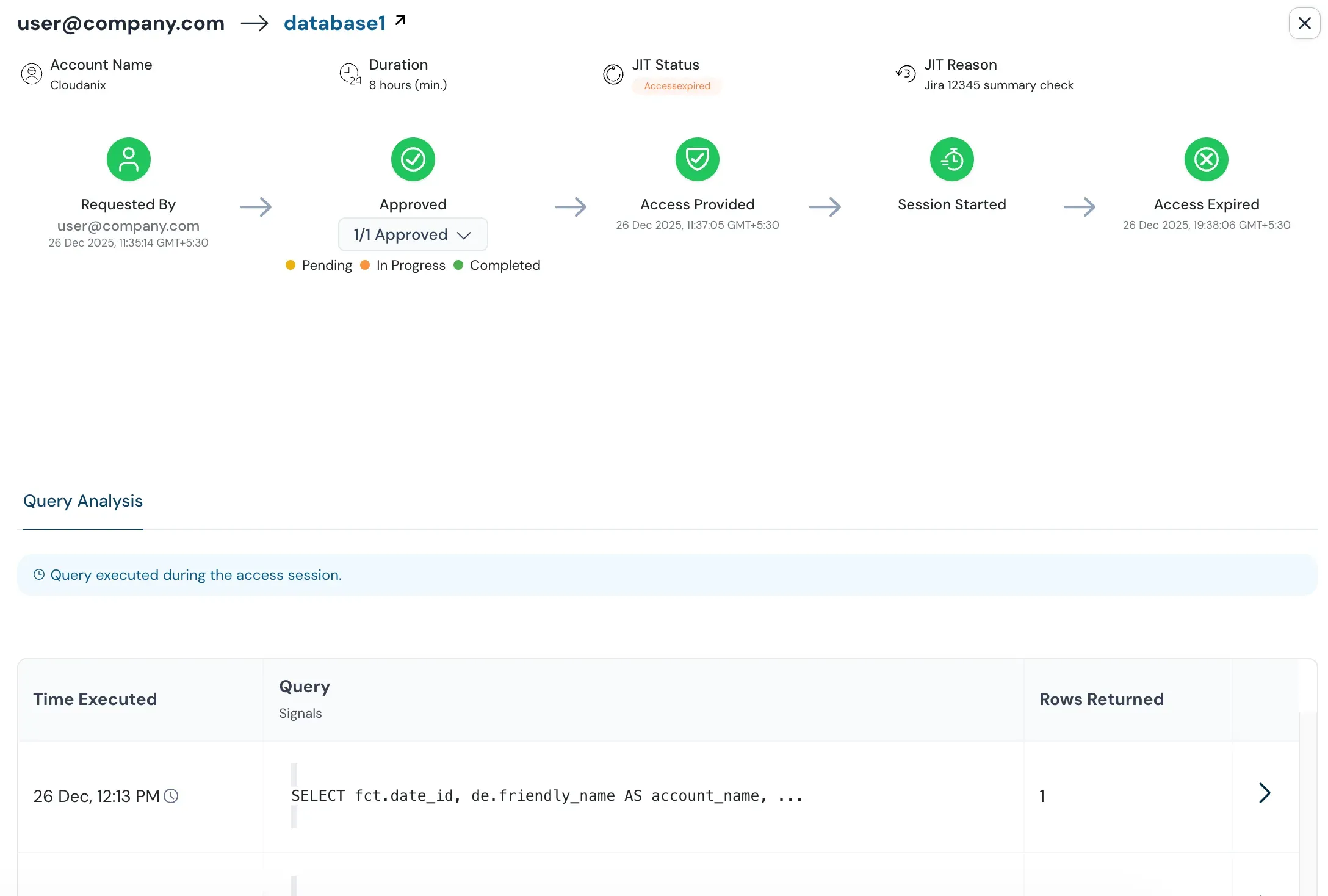
Cloudanix generates temporary, time-bound passwords for each approved database access request. Users connect from their local machines through secure tunneling—no jump boxes or public IP exposure required. All database queries are logged for audit and compliance. When the session expires, the temporary password is automatically revoked.
Cloudanix JIT helps you meet requirements for SOC 2, HIPAA, PCI DSS, GDPR, ISO 27001, NIST, and other major compliance frameworks. The platform provides complete audit trails showing who requested access, who approved it, what actions were taken, and when access expired—essential evidence for audits.
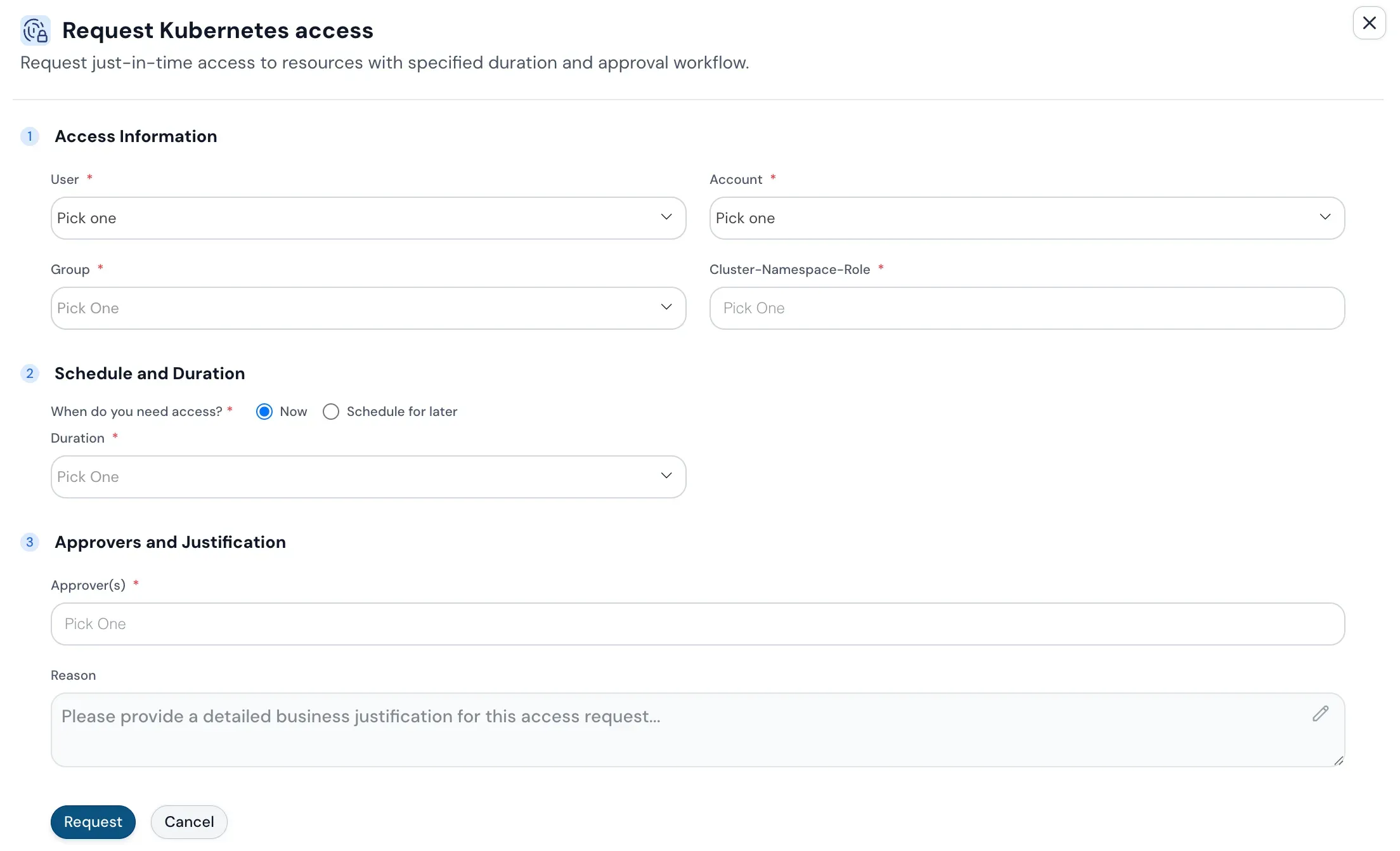
Absolutely. Users continue using their familiar tools like SSH, SSM, kubectl, database clients, and cloud CLIs. Cloudanix JIT works behind the scenes to provide temporary credentials without disrupting existing workflows. There's no need to learn new interfaces or change how teams work.
The Cloudanix Slack integration enables users to request access directly within Slack using simple commands. Approvers receive instant notifications in Slack and can approve or deny requests with a single click—no need to switch contexts or log into separate consoles. All actions are still recorded for compliance.
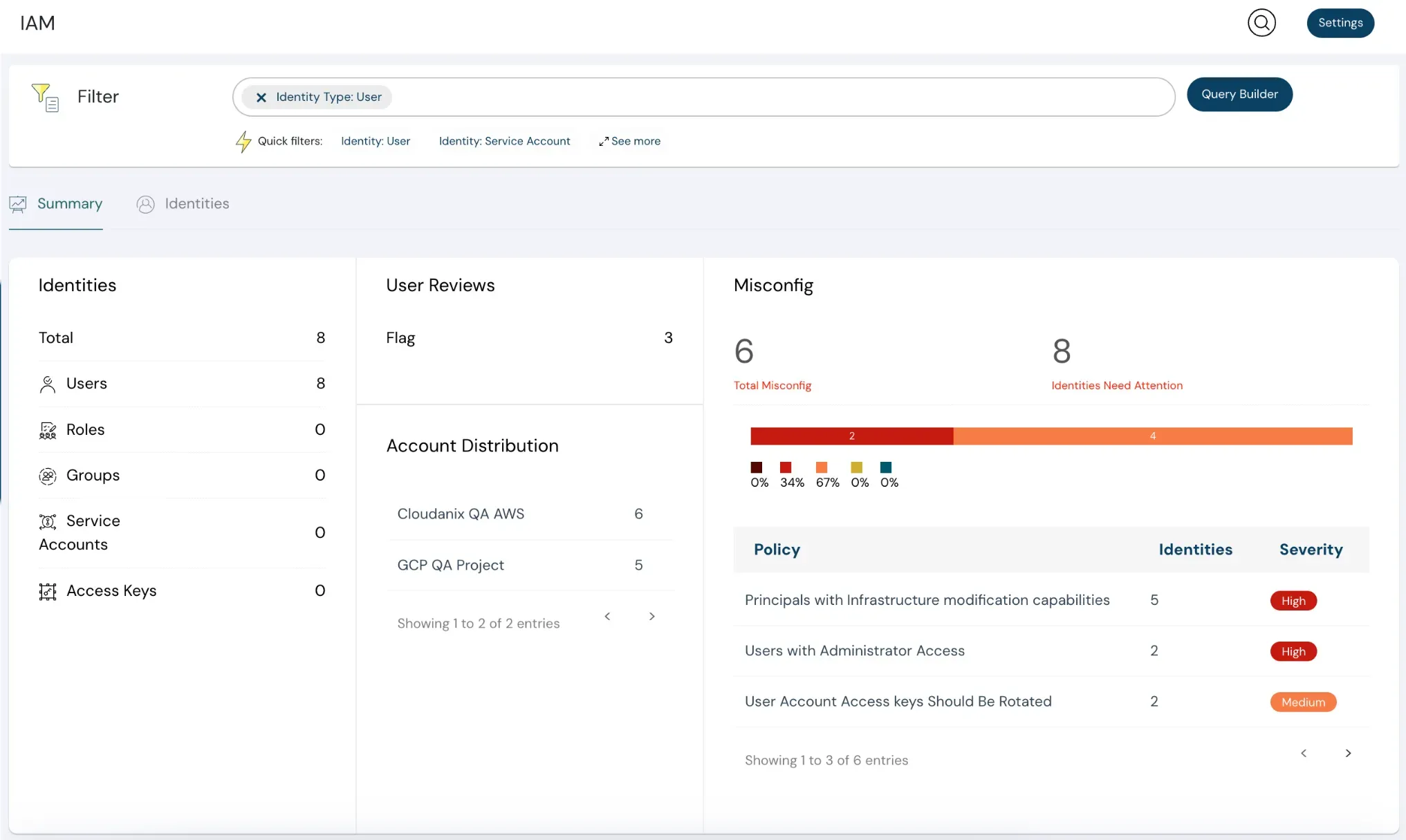
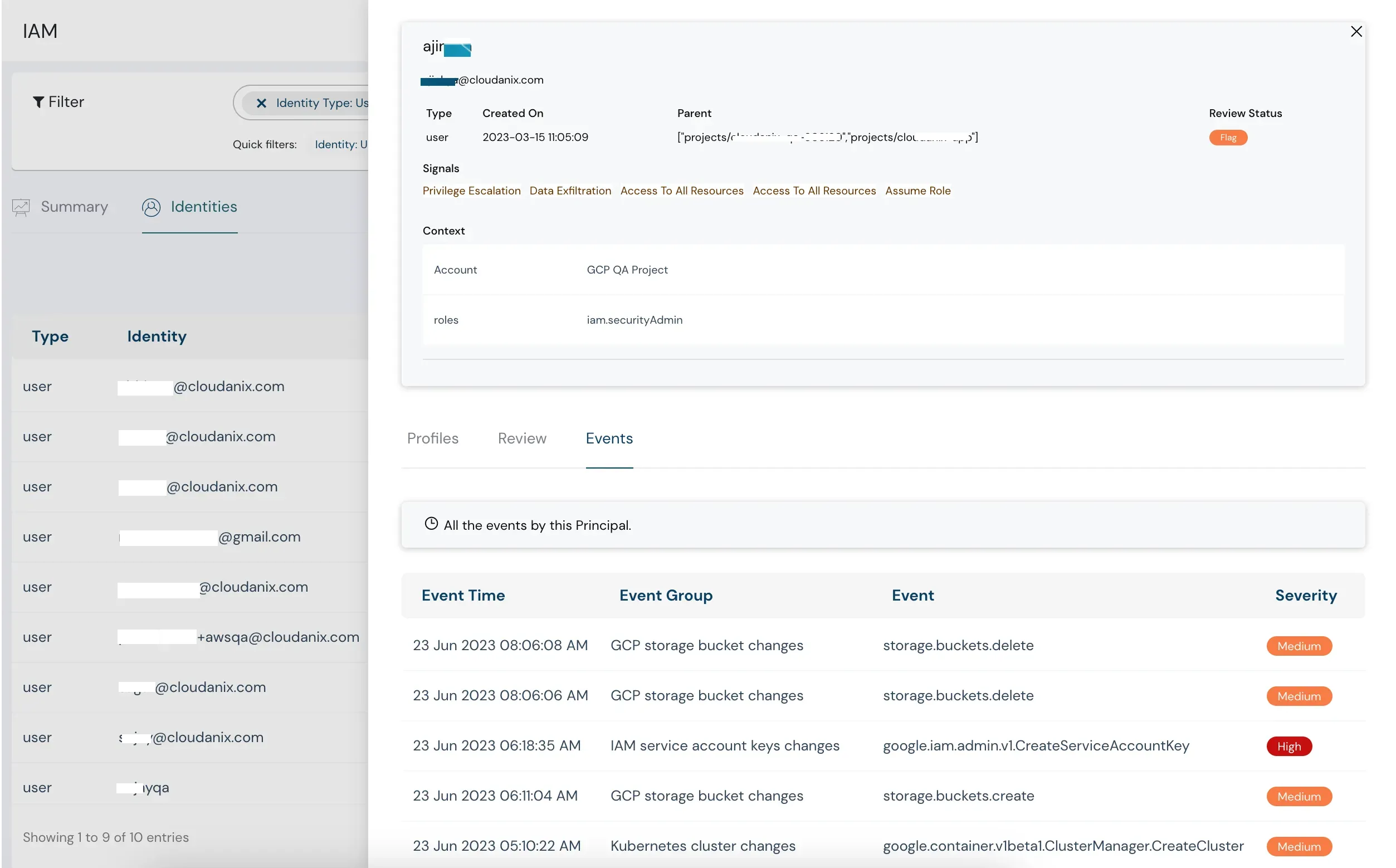
JIT (Just In Time access) provides temporary, on-demand access with approval workflows, eliminating standing privileges. CIEM (Cloud Infrastructure Entitlement Management) analyzes existing permissions to identify over-privileged identities, excessive entitlements, and access risks. Together, they form a comprehensive identity security strategy—CIEM identifies what needs fixing, and JIT prevents the problem from recurring.
Cloudanix enforces multiple security layers: approval workflows for every request, time-bound credentials that auto-expire, role-based access control (RBAC), complete activity logging, and real-time monitoring. For databases and VMs, connections are secured through encrypted tunnels. All access is granted based on least privilege principles.
Yes, Cloudanix provides fully customizable approval workflows. You can define different approval chains based on resource sensitivity, user roles, permission levels, or business hours. Set up multi-step approvals, require manager sign-off, or enable auto-approval for low-risk requests. The platform adapts to your organization's specific security policies.