Just-In-Time (JIT) Access
Discover the importance of Just-in-Time access in cybersecurity, its benefits, implementation, types, and challenges.
Read moreJust In Time IAM | Cloudanix
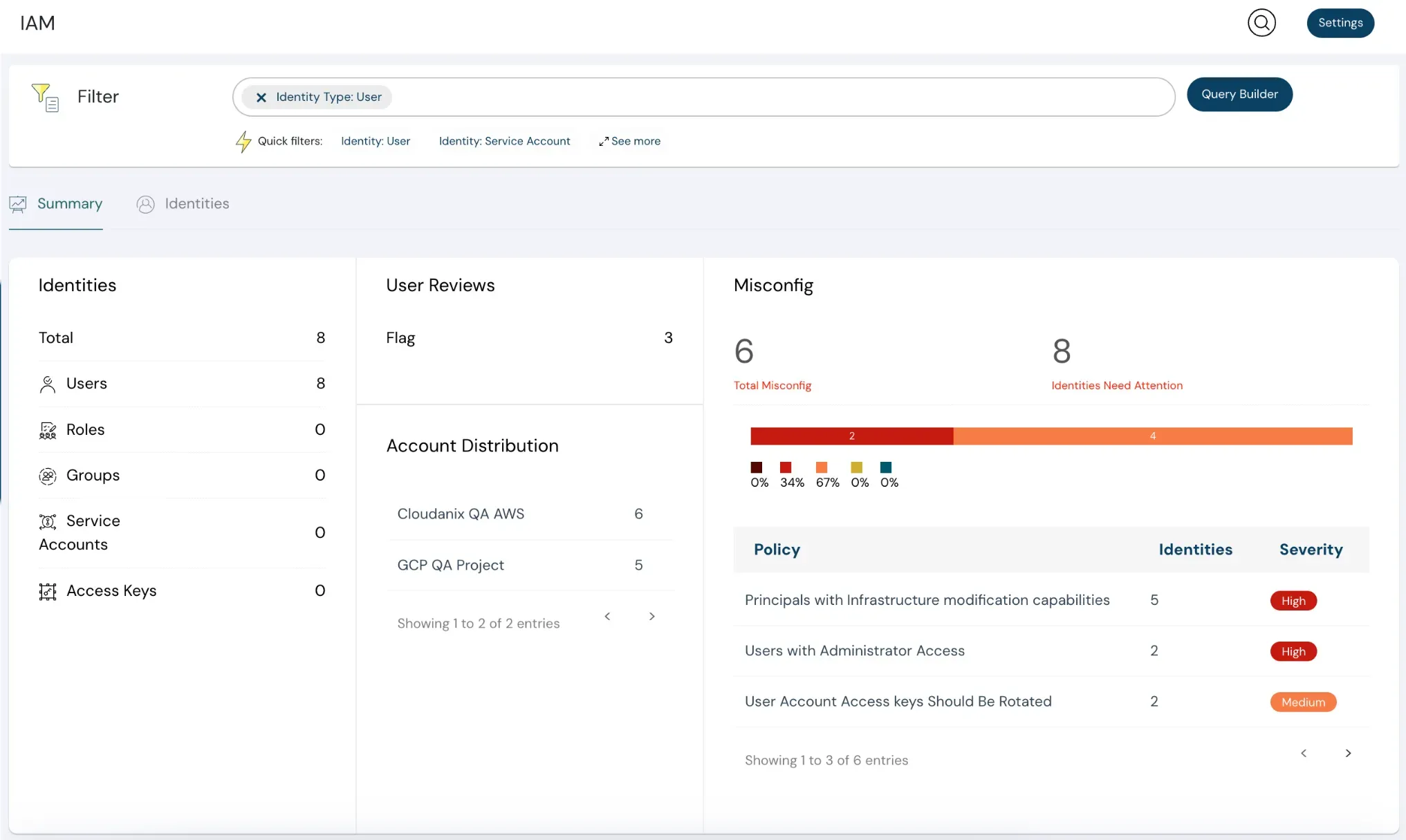
The IAM perimeter is the new cloud security boundary. Cloudanix Just In Time (JIT) IAM ensures that your team gets the right access only when needed—no more, no less. Boost security, reduce IAM risks, and make access approvals seamless across your organization.
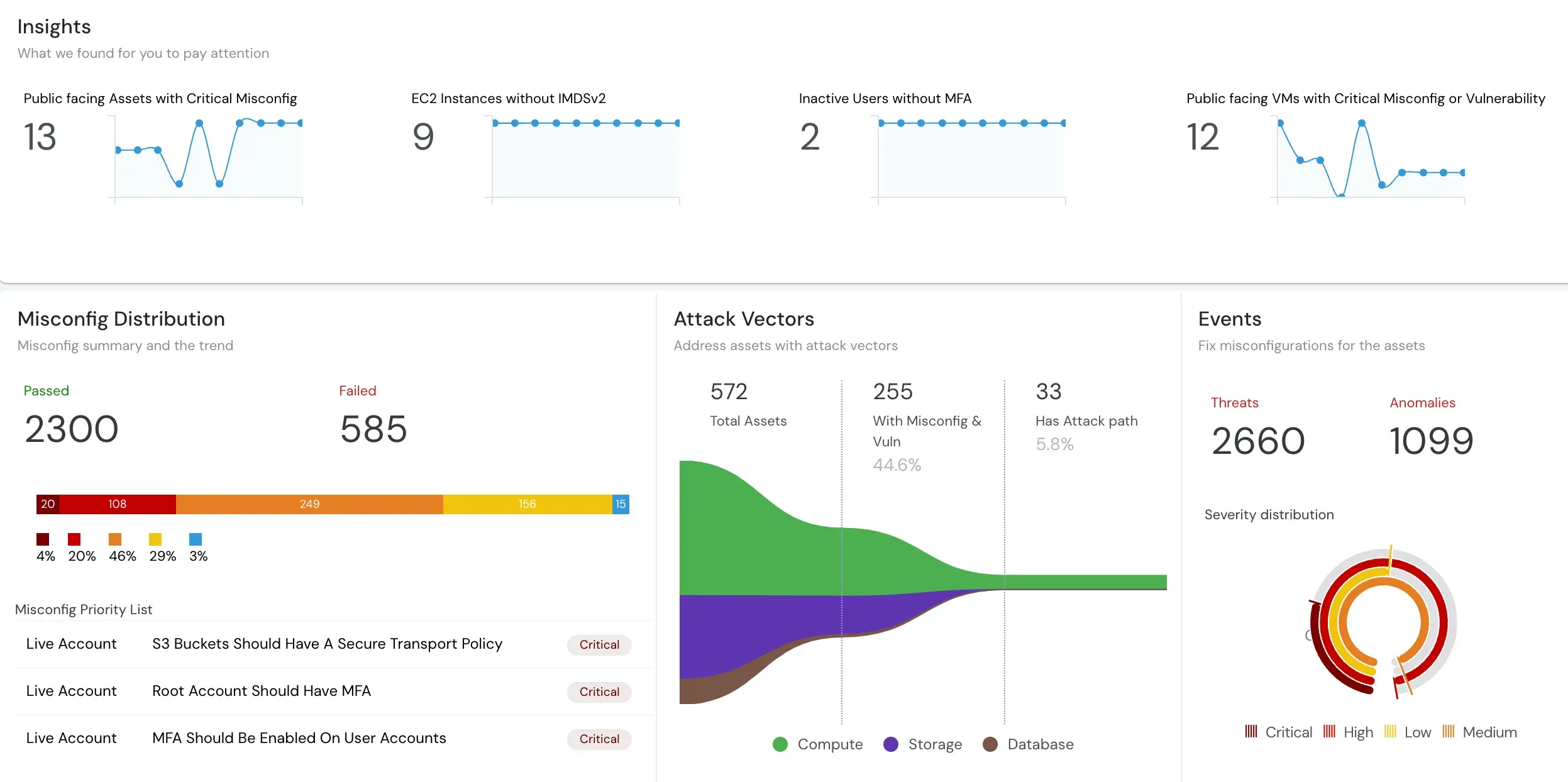
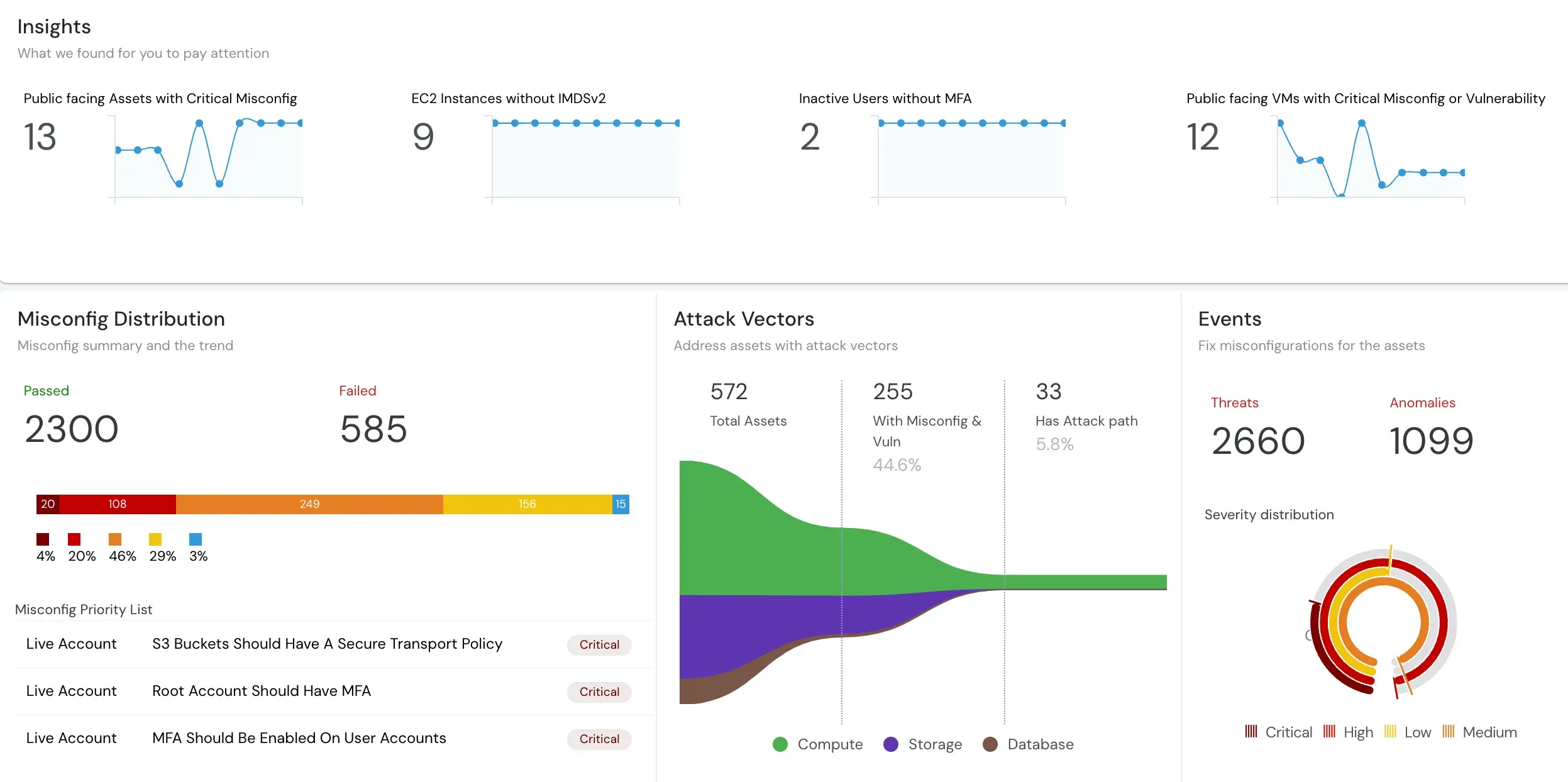
In the cloud, the network is no longer the perimeter—identity is. Over-permissive IAM roles create one of the largest attack surfaces in modern cloud environments. Cloudanix eliminates “always-on” permissions by granting access only when they are genuinely needed. This prevents privilege creep, reduces IAM toxicity, and strengthens your security posture without slowing teams down. Your developers get the right access at the right time, security teams get complete visibility and audit trails, and your overall cloud risk is significantly reduced. Simplified JIT Workflow Your Team Will Love — Request, approve, and audit—all in a frictionless experience. Cloudanix removes clunky request flows and replaces them with a few quick clicks for both developers and security teams.
Talk to an Expert & Get Started Today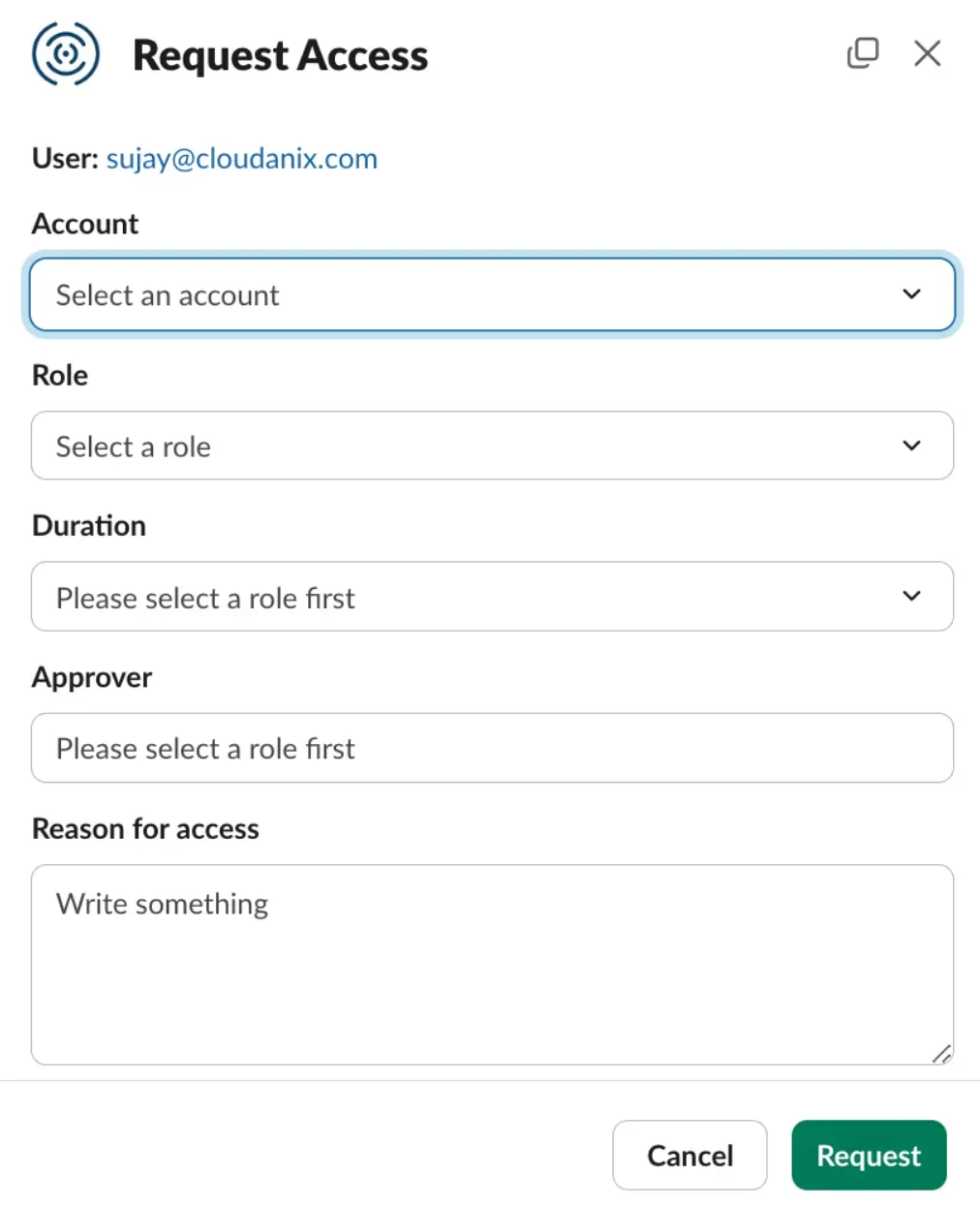
Team members can request temporary access for specific resources, with permissions auto-expiring once the task is complete. This ensures that no principal retains privileges indefinitely. Every request follows an approval workflow and every action is logged for compliance, enabling a healthy IAM posture.
JIT via Slack makes it quick to request and approve access without leaving your workflow. Simply invoke the Cloudanix JIT app in Slack, notify approvers instantly, and approve or deny with a click—speeding up access while keeping full security controls in place.
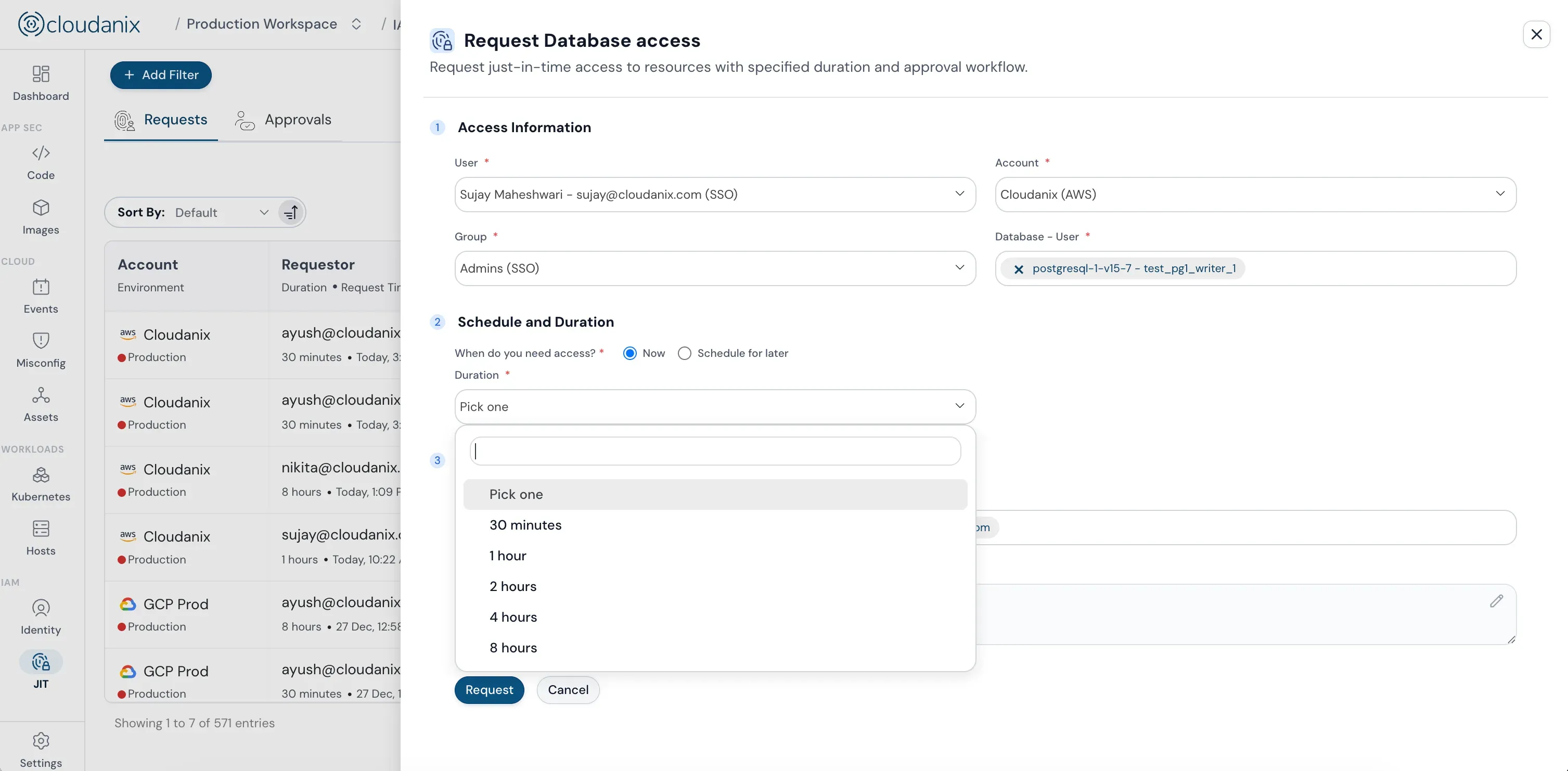
Cloudanix JIT Database access eliminates standing privileges and insecure jump boxes. Developers connect securely from their local machine to private databases via secure tunneling—no public IP exposure. All queries are logged for audit and compliance, and the process integrates seamlessly with Slack and the Cloudanix console.
Improve Security Without Compromising Speed
JIT access allows users to get permissions only when needed, reducing standing privileges and improving overall cloud security. Explore how you can integrate and implement it.
In this 2 minute interactive video, you will see how Cloudanix DAM ensures that your sensitive data is protected.
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoCLOUDANIX
Explore guides, checklists, and blogs that simplify cloud security and help you secure your infrastructure.
Discover the importance of Just-in-Time access in cybersecurity, its benefits, implementation, types, and challenges.
Read more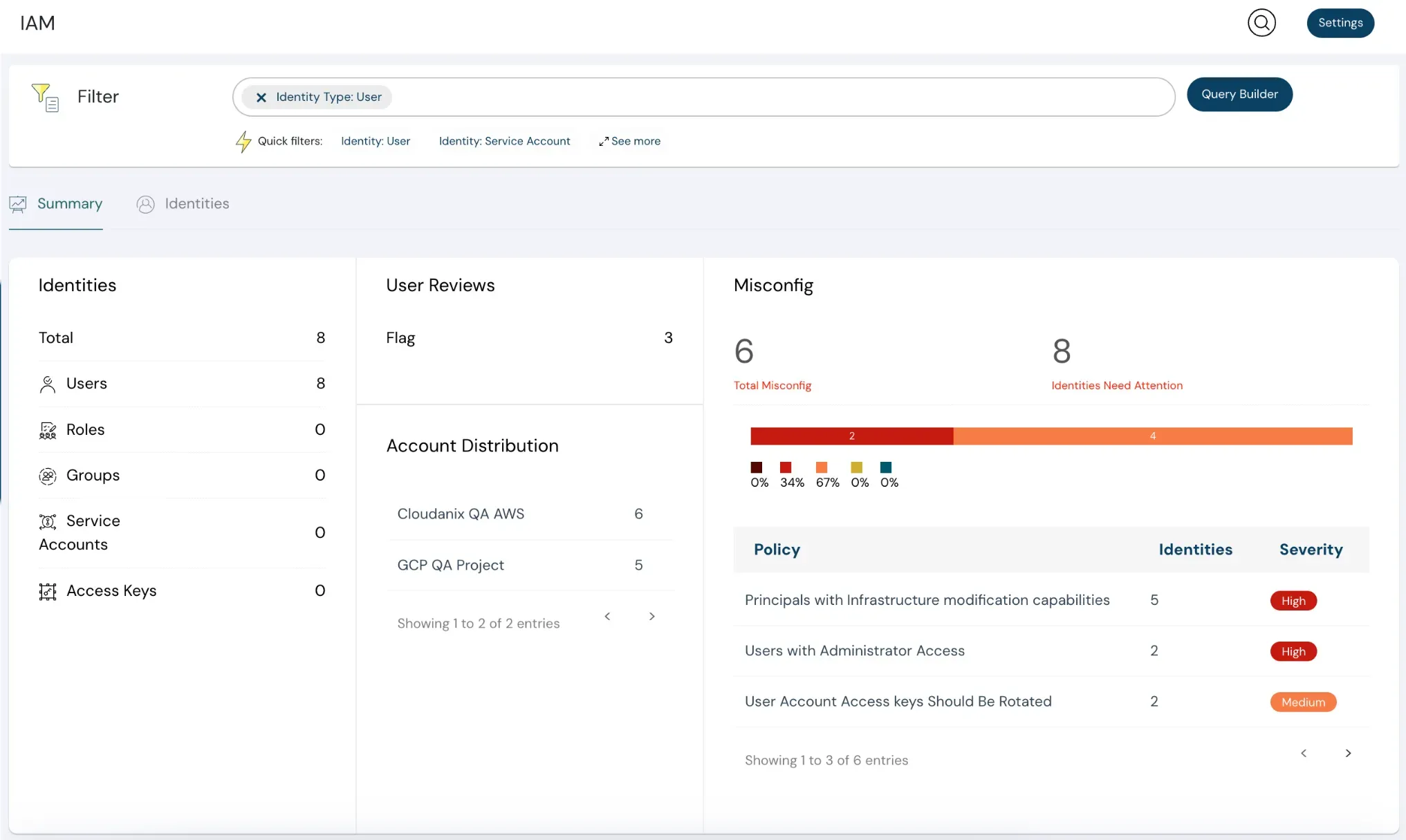
Dynamic landscape of cloud computing, effective Identity and Access Management (IAM) is crucial for safeguarding your organization's resourc…
Read the blogEliminate standing privileges with granular JIT access. Implement SQL-level auditing and JEP across hybrid databases to simplify GDPR and HI…
Read the blogCloudanix offers you a single dashboard to secure your workloads. Learn how to set up Cloudanix for your cloud platform from our documentati…
Take a lookA complete history of changes, improvements, and fixes for Cloudanix. Subscribe to get notified about the latest updates.
View Changelog