Capability
Cloudanix JIT ensures your Cloud, Databases, and other cloud resources are protected with mature approval workflows and detailed logging to meet audit and compliance requirements.
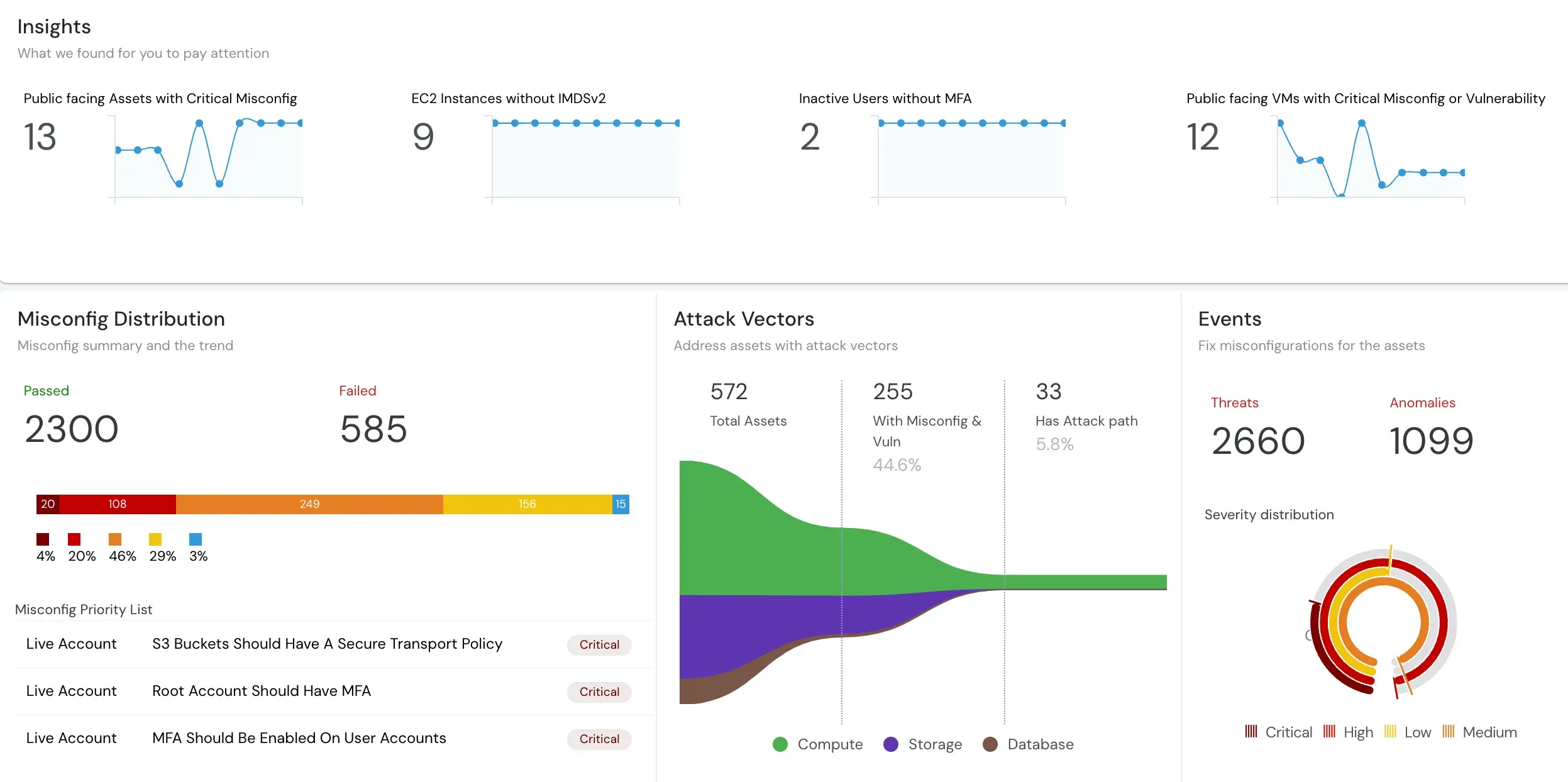
Choose Contextual Visibility Over Complexity
Efficient security teams need an effective tool for contextual visibility, not merely a brand which is difficult to adopt and operate. See why hundreds of companies choose Cloudanix over StrongDM to correlate their security findings from Code, Cloud, Workloads and Identity.
StrongDM Alternative | Just In Time (JIT) Access Management | Cloudanix
Organizations are choosing Cloudanix over StrongDM for a combination of capability, ease of use, and unmatched customer support. Cloudanix delivers a mature Just In Time (JIT) access management solution that’s simple to adopt, integrates seamlessly into workflows, and is backed by a support team that operates as an extension of yours.
Cloudanix JIT ensures your Cloud, Databases, and other cloud resources are protected with mature approval workflows and detailed logging to meet audit and compliance requirements.
Onboarding takes just 30 minutes. Once complete, your teams can use JIT access via our intuitive UI or Slack app—ensuring fast adoption and immediate value.
We believe support delayed is support denied. Every customer gets a dedicated Slack channel, enabling real-time communication and making our team an extension of yours.
Compare our features with the competition
A quick look at how Cloudanix stacks up against StrongDM in Just In Time (JIT) access, cloud security, and compliance.
| Feature | Cloudanix | StrongDM |
|---|---|---|
| Just In Time - Cloud | Yes | Yes |
| Just In Time - Database | Yes | Yes |
| Native and Slack Workflows | Yes | Yes |
| Anomaly & Threat Detection | Yes | No |
| CloudPrem Audit Storage | Yes | No |
| CNAPP Capability | Horizontal integration with CNAPP | No |
| CIEM | Yes | No |
| Data Perimeter and Visualization | Yes | No |
| Right Sizing Identities | Yes | No |
| Onboarding | White Glove | Regular |
| Support | Dedicated Slack channel | Regular |
| Dedicated Account Manager | Yes | Limited Support |
What Our Users Are Saying
Cloudanix is trusted by security leaders worldwide to deliver proactive, reliable, and cutting-edge cloud security.
Cloudanix completed the misconfiguration assessment of our AWS accounts even before we could fill up the subscription page with our credit card details!
The speed and efficiency of Cloudanix’s security checks have been unmatched in our experience.
We are excited to leverage the comprehensive multi-cloud DevSecOps solution by Cloudanix to secure our production workloads on AWS.
Cloudanix has demonstrated that it can solve many challenges that DevSecOps teams face, while continually adding new features such as SOC2 compliance and drift detection, which drive daily security and operational benefits.
We are a Fintech company and Cloudanix has been an absolute bliss.
It not only tells you what's wrong but also helps you fix it. Security is very crucial for us and Cloudanix, with minimal investment of our time, helps us achieve it.
Seamless migration without disrupting your workflow
Cloudanix onboarding takes just 30 minutes, no matter which IdP you use. With an agentless installation, there’s zero change to your existing IAM setup. We integrate seamlessly with your current tools and workflows, including Slack-based JIT access requests.
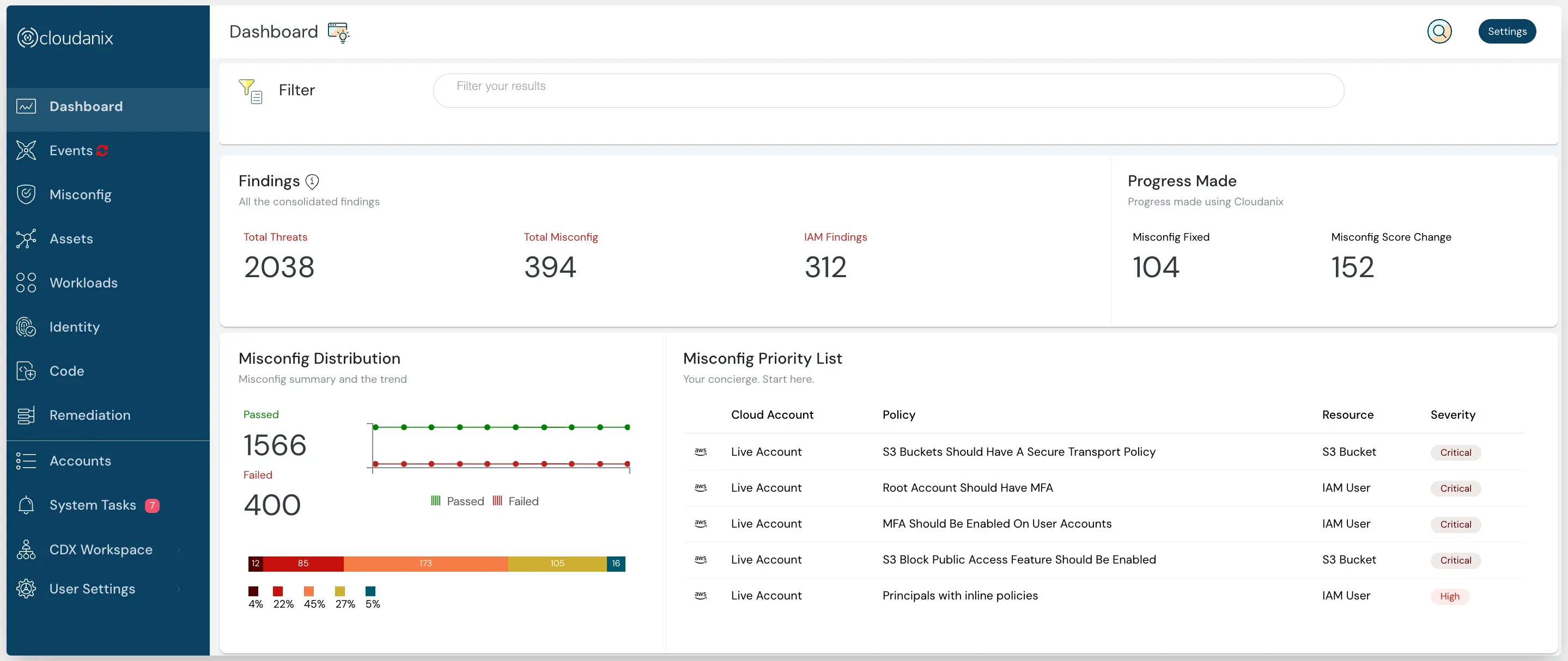
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoCLOUDANIX
Explore how Cloudanix compares to other access management platforms and discover resources to secure your cloud infrastructure.
See how Cloudanix provides a true multi-cloud CNAPP alternative to Wiz with independent, vendor-neutral security coverage.
Compare Now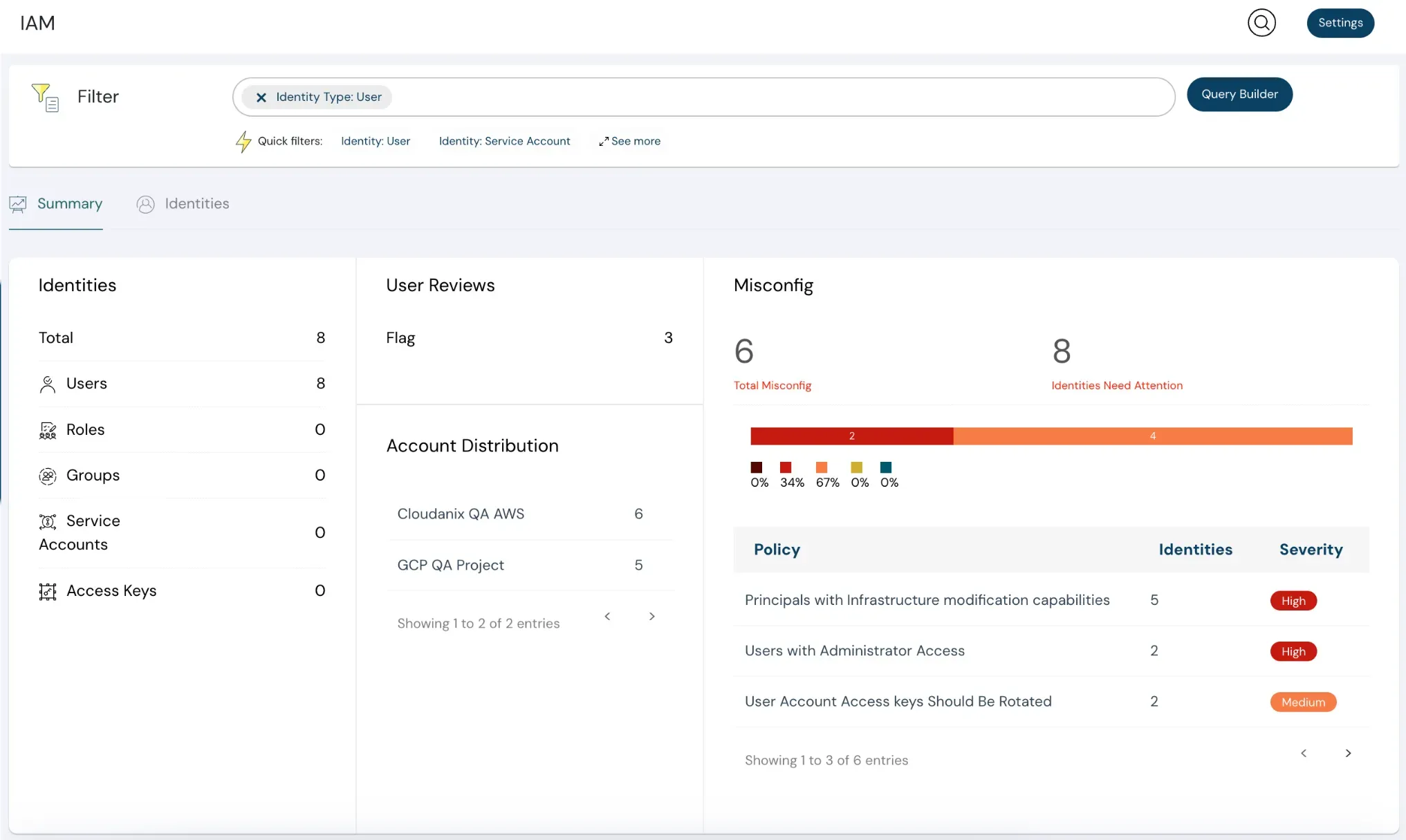
Compare Cloudanix and Commonfate.io for Just-in-Time access management with seamless IdP integration and Slack-based workflows.
Compare Now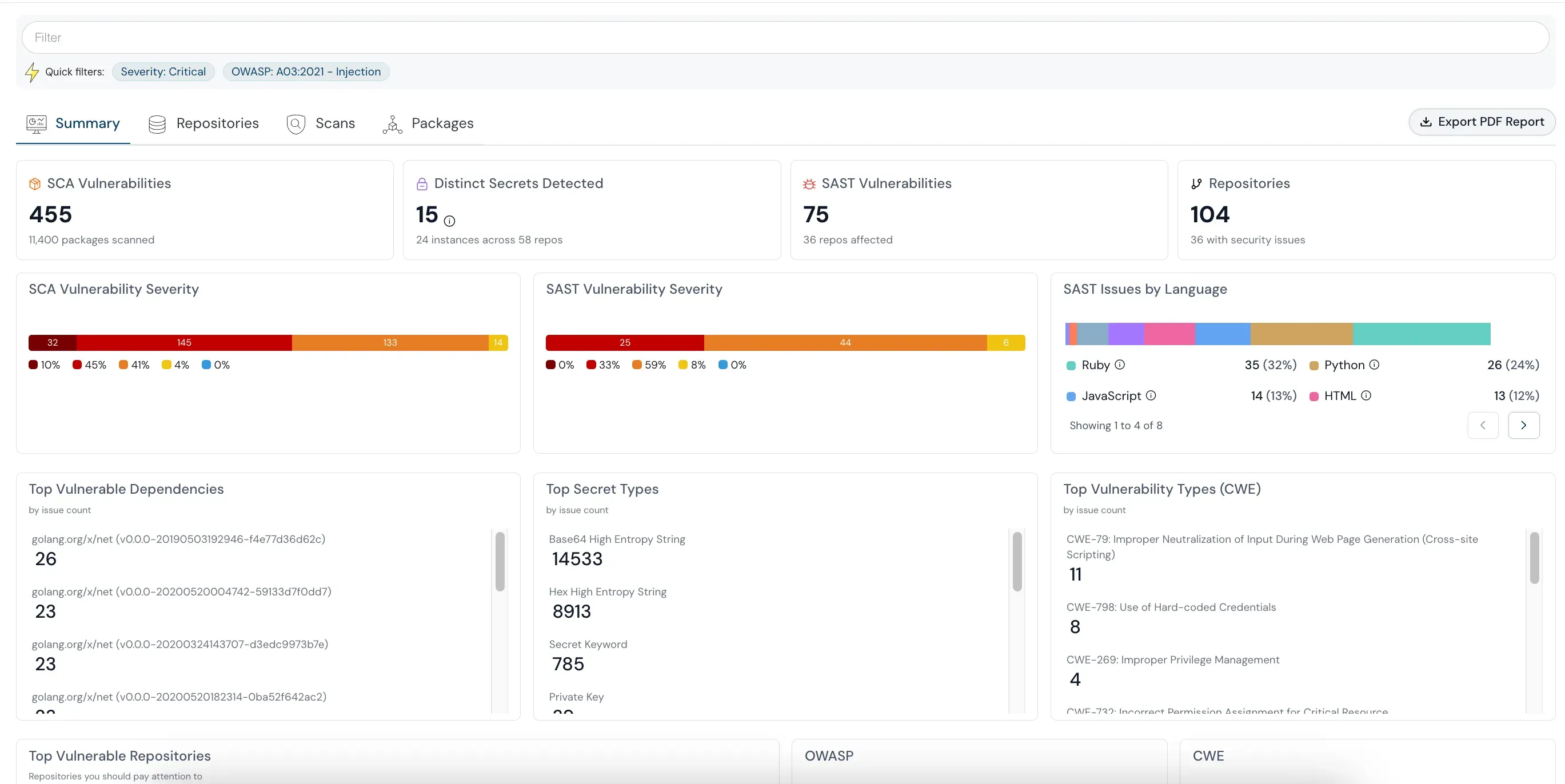
Compare Cloudanix and BeyondTrust Entitle for privileged access management, JIT workflows, and multi-cloud identity security.
Compare NowA step-by-step guide for security leaders to implement Just-in-Time access across all major cloud providers.
Read the Use CaseLearn how JIT access eliminates standing privileges and reduces your cloud attack surface with time-bound, approved access.
Read the Blog