OS Login Configuration
Enable OS login to ensure that SSH keys used to connect to instances are mapped with IAM users for enhanced security and access control.
Cloudanix
Comprehensive Google Cloud security auditing services to protect your compute instances from misconfigurations and security vulnerabilities.
Enable OS login to ensure that SSH keys used to connect to instances are mapped with IAM users for enhanced security and access control.
IP forwarding should be disabled on all instances to ensure proper packet routing and prevent unauthorized network traffic.
Ensure instances are configured across multiple availability zones to eliminate single points of failure and ensure proper failover capabilities.
Monitor and control the total number of VM instances to prevent unauthorized resource consumption and ensure only approved applications are running.
Implement instance-specific SSH keys instead of project-wide keys to enforce the principle of least privilege and prevent privilege escalation.
Prevent instances from using default service accounts with full API access and ensure proper service account configuration with least privilege principles.
Enable Customer Supplied Encryption Keys for disks to ensure only authorized team members can access disk data, including protection from Google access.
Disable serial port connections for VM instances to prevent unrestricted IP access and enhance instance security.
Ensure Compute instances are launched with Shielded VM enabled for advanced security protections against rootkits and boot-level attacks.
Prevent compute instances from being configured with external IP addresses to reduce attack surface and enhance network security.
Configure instances to avoid using default Compute Engine service accounts with excessive Editor role permissions on projects.
Monitor resource usage against Google Cloud account limits to prevent service disruptions and ensure resource availability.
Enable Confidential Computing to protect sensitive code and data encrypted in memory during processing, preventing Google access to encryption keys.
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoCLOUDANIX
Explore guides, checklists, and blogs that simplify cloud security and help you secure your infrastructure.
Real-world success stories where Cloudanix helped organizations secure their cloud infrastructure. Watch how we made a difference across ind…
Read Case Studies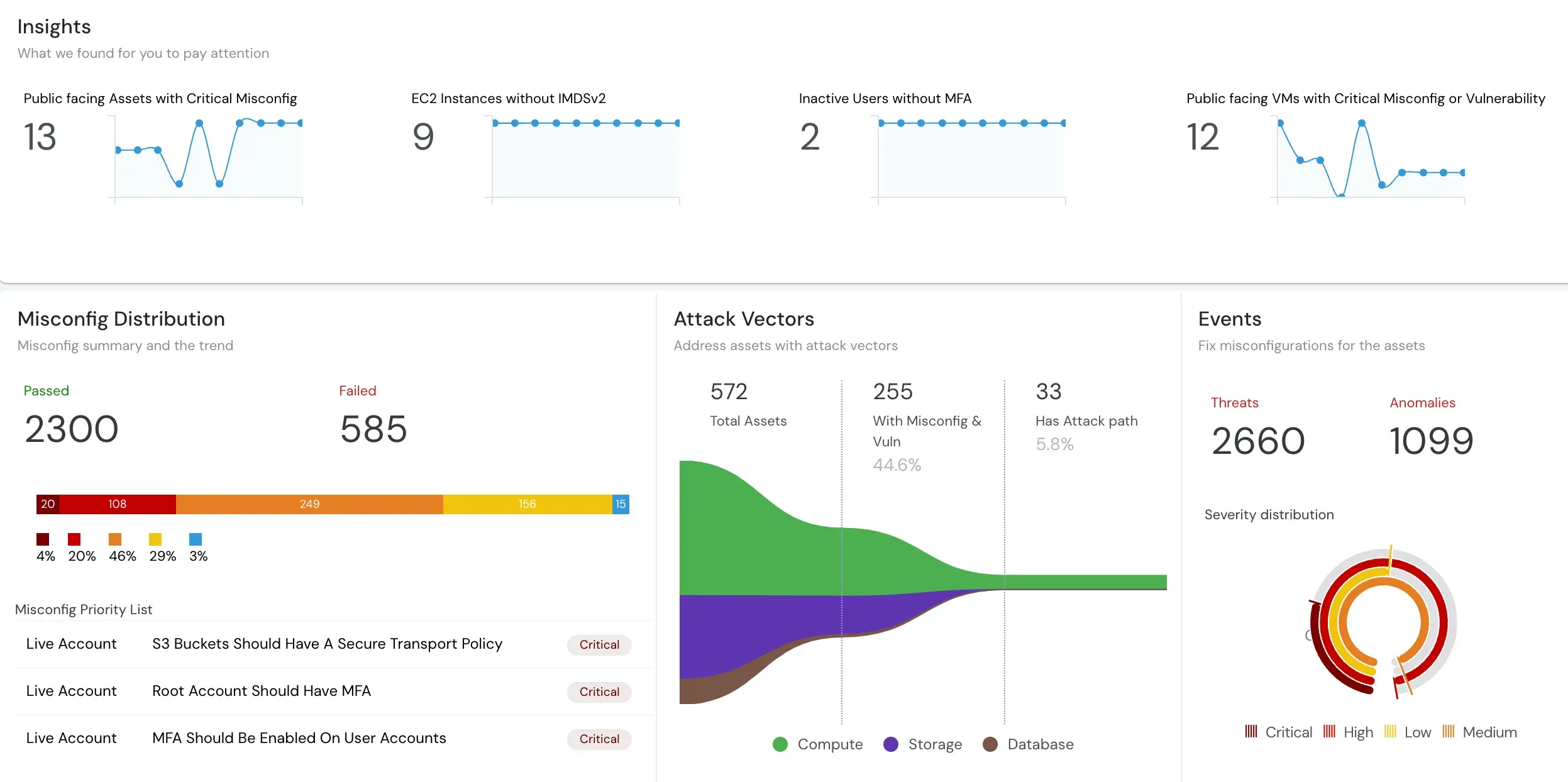
Understand what Cloud Security Posture Management (CSPM) is and how it automates security and compliance across cloud environments.
Read moreUnderstand how CASB, CSPM, and SIEM work together to enhance your cloud security posture and ensure better governance.
Read the blogIn-depth assessment of cloud environment for security, compliance, and optimization. Identify vulnerabilities, ensure data protection, and o…
Read the blogCloud environments are getting more complex and dynamic day by day, making it difficult to gain complete visibility into all assets and thei…
Read the blogCloudanix offers you a single dashboard to secure your workloads. Learn how to set up Cloudanix for your cloud platform from our documentati…
Take a lookA complete history of changes, improvements, and fixes for Cloudanix. Subscribe to get notified about the latest updates.
View Changelog