Root Account Should Not Have Access Keys
Root account has full permissions across the entire account. Root account should not have access keys. Also, it certainly shouldn't access any service. Instead, create IAM users with predefined roles.
Cloudanix
Root account has full permissions across the entire account. Root account should not have access keys. Also, it certainly shouldn't access any service. Instead, create IAM users with predefined roles.
Root account has full permissions across the entire account. Root account should not have access keys. Also, it certainly shouldn't access any service. Instead, create IAM users with predefined roles.
Root account should not have access keys. If at all you have that, then the keys should be rotated periodically.
Certificates should not be tied with root accounts.
Certificates tied with root accounts needs rotation.
Multifactor Authentication is strongly recommended to be enabled for every account with no exceptions in order to secure your AWS environment and adhere to IAM security best practices.
Ensure that your root account password is rotated every few days.
Your AWS account should have minimum number of admins
Your AWS account has too many admins.
Any unused IAM user without console access and API access should be removed as an extra security measure for protecting your AWS resources against unapproved access.
MFA must be enabled on user accounts. AWS recommends that you configure multi-factor authentication (MFA) to help protect your AWS resources.
The access keys should rotated periodically.
The certificates should be rotated periodically.
Inactive access keys should be dropped.
Users who are infrequent or do not need access to console, their account access should be cleared off.
Checks inactivity of any user on a service. Those priviledges should be removed for better security posture.
IAM users should not have Inline policies. It is recommended that IAM policies be applied directly to groups and roles but not users.
Multiple access keys for the same user should be avoided. There should be just 1 access key per user account.
Inactive roles should be cleaned up.
Roles which have access to services but have not used in past several days should be looked into and cleaned up.
Role should not have inline policies attached to them.
Empty groups should be cleaned up and should not linger around.
Ensures that you rotate your certificate before the set configurable days.
Password policy should be complex enough so that users can set passwords which are not easy to guess and crack.
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoCLOUDANIX
Explore guides, checklists, and blogs that simplify cloud security and help you secure your infrastructure.
Real-world success stories where Cloudanix helped organizations secure their cloud infrastructure. Watch how we made a difference across ind…
Read Case Studies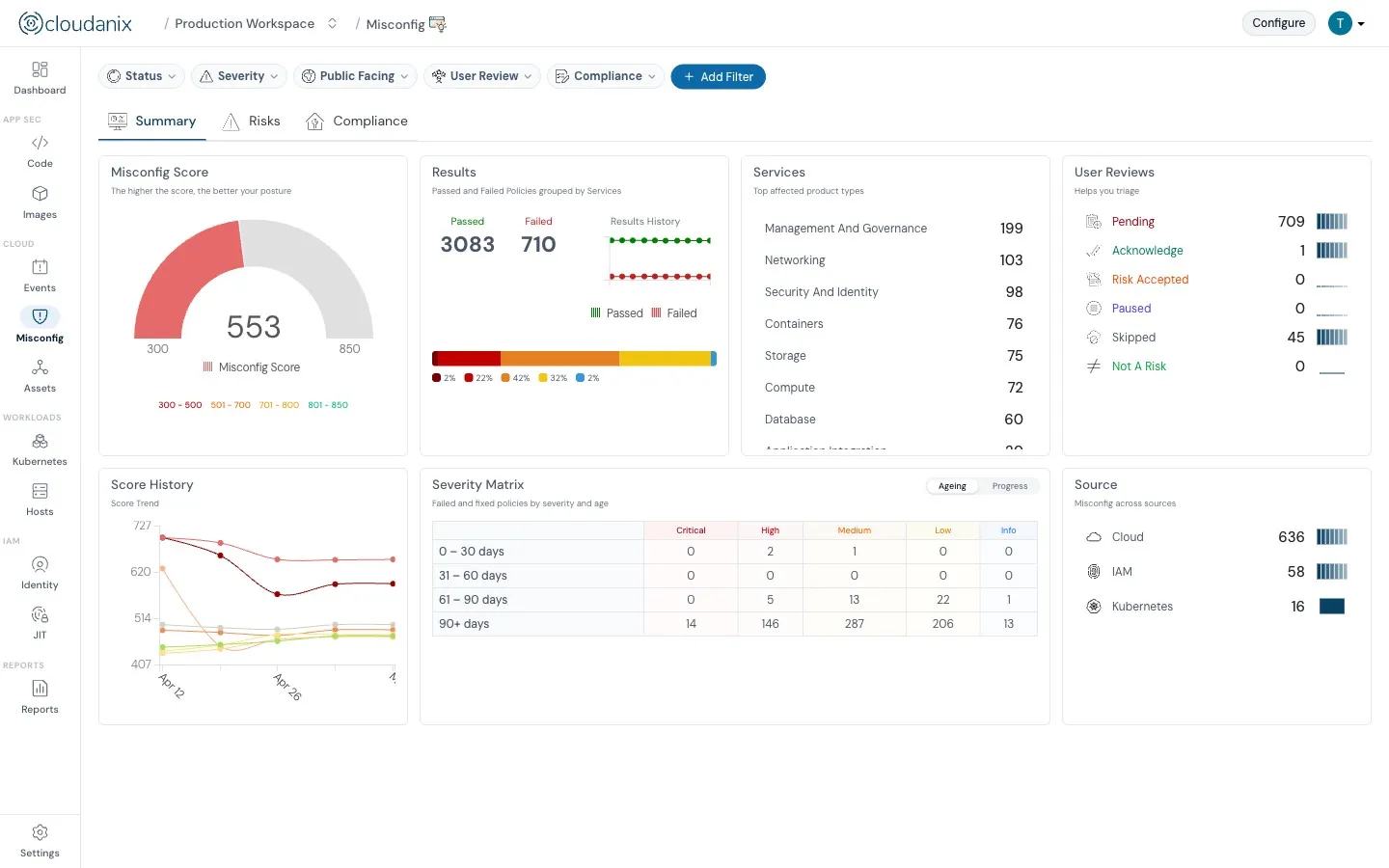
Understand what Cloud Security Posture Management (CSPM) is and how it automates security and compliance across cloud environments.
Read moreUnderstand how CASB, CSPM, and SIEM work together to enhance your cloud security posture and ensure better governance.
Read the blogIn-depth assessment of cloud environment for security, compliance, and optimization. Identify vulnerabilities, ensure data protection, and o…
Read the blogCloud environments are getting more complex and dynamic day by day, making it difficult to gain complete visibility into all assets and thei…
Read the blogCloudanix offers you a single dashboard to secure your workloads. Learn how to set up Cloudanix for your cloud platform from our documentati…
Take a lookA complete history of changes, improvements, and fixes for Cloudanix. Subscribe to get notified about the latest updates.
View Changelog