Fortify Supply Chain, Contextualization at Runtime and Prioritization on Exploitability
In today’s interconnected world, securing your open source dependencies is paramount to safeguarding your applications. Cloudanix introduces a powerful solution that empowers you to identify and address vulnerabilities, gain contextual understanding of your security landscape, and prioritize risks based on their impact. With Cloudanix, you can confidently protect your applications and safeguard your organization.
Identify and Address Vulnerabilities in Your Open Source Dependencies to Improve Supply Chain Security
Cloudanix SCA helps identify vulnerabilities and compliance issues (License, Maintenance, Security Practices, etc.). Automatically scan your code repositories for Software Bill Of Materials (SBOM) and find out vulnerabilities and compliance issues associated with the SBOM for supply chain security. Cloudanix highlights fixes and provides recommendations for updates to open source vulnerabilities.
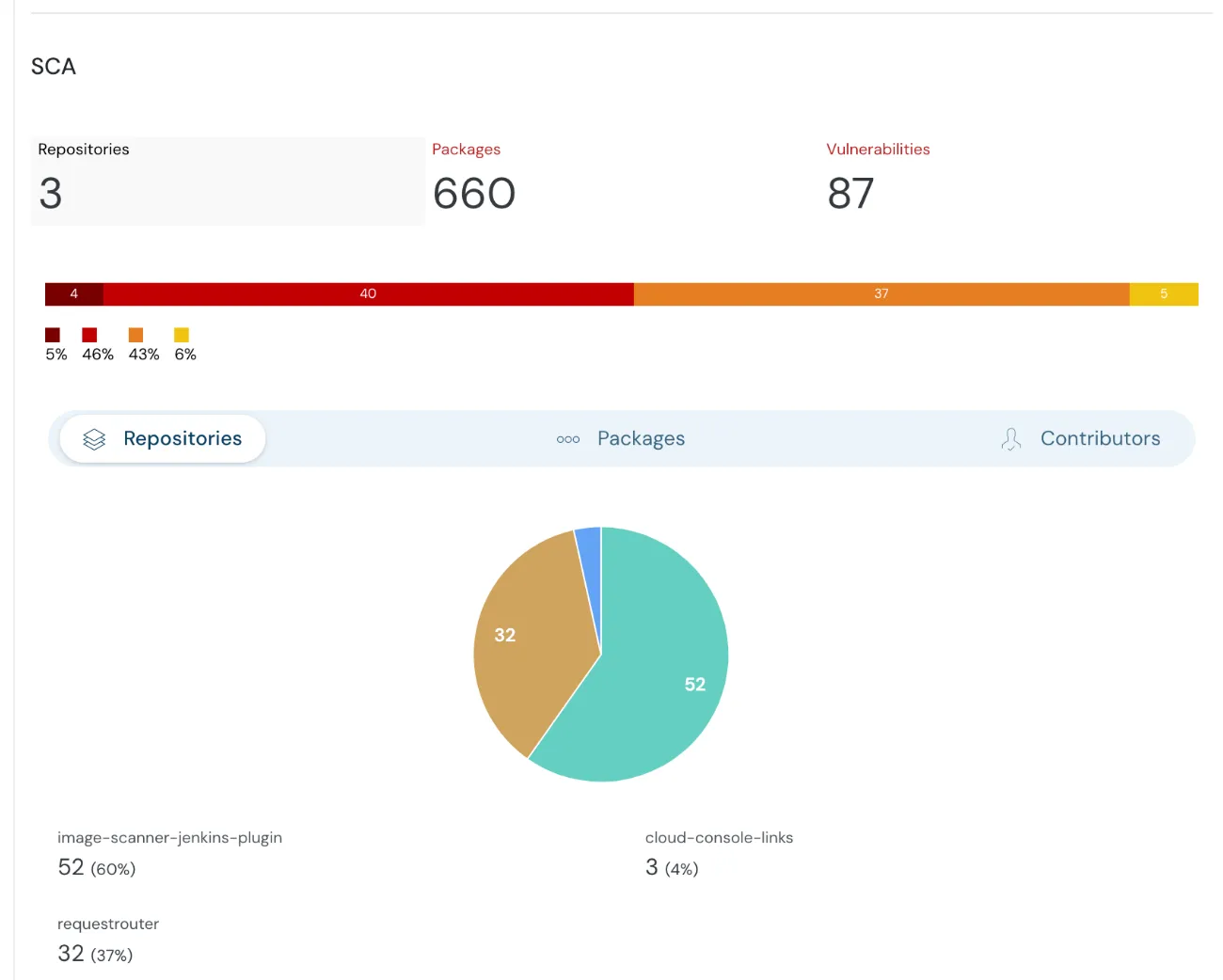 Summary of SCA in Cloudanix dashboard
Summary of SCA in Cloudanix dashboard
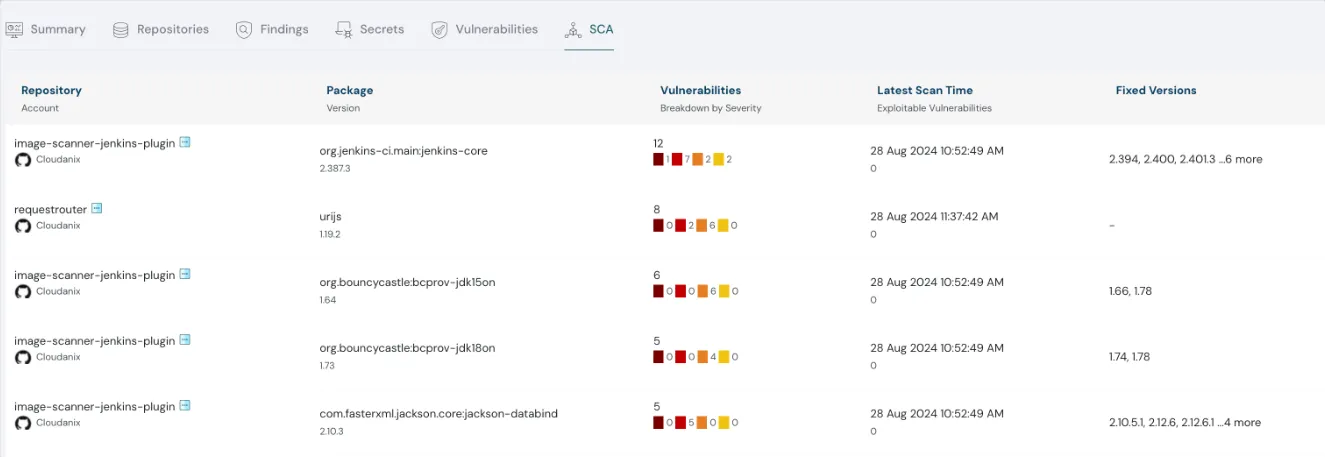
Cloudanix showing details of SCA in dashboard
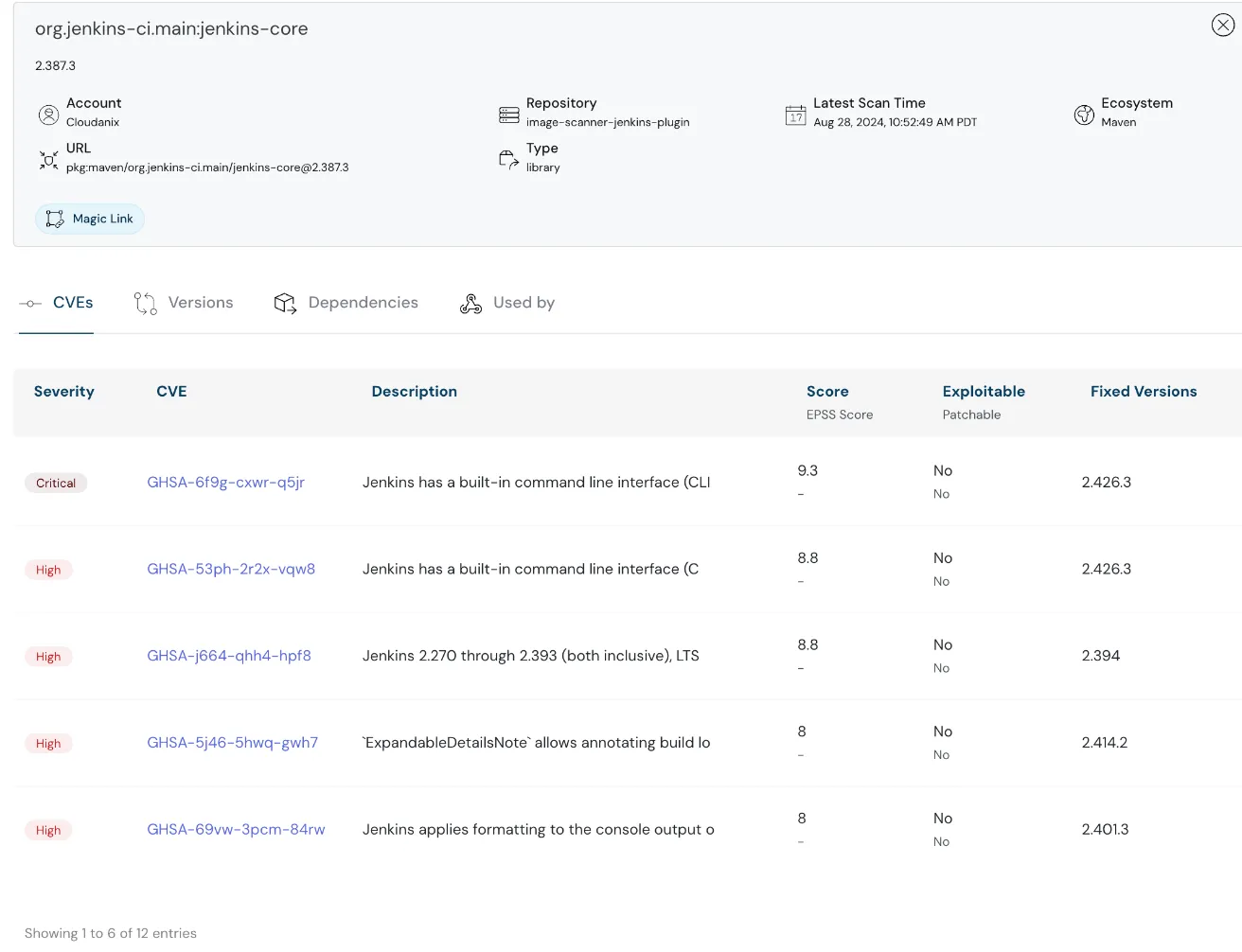 Cloudanix showcasing third party scans
Cloudanix showcasing third party scans
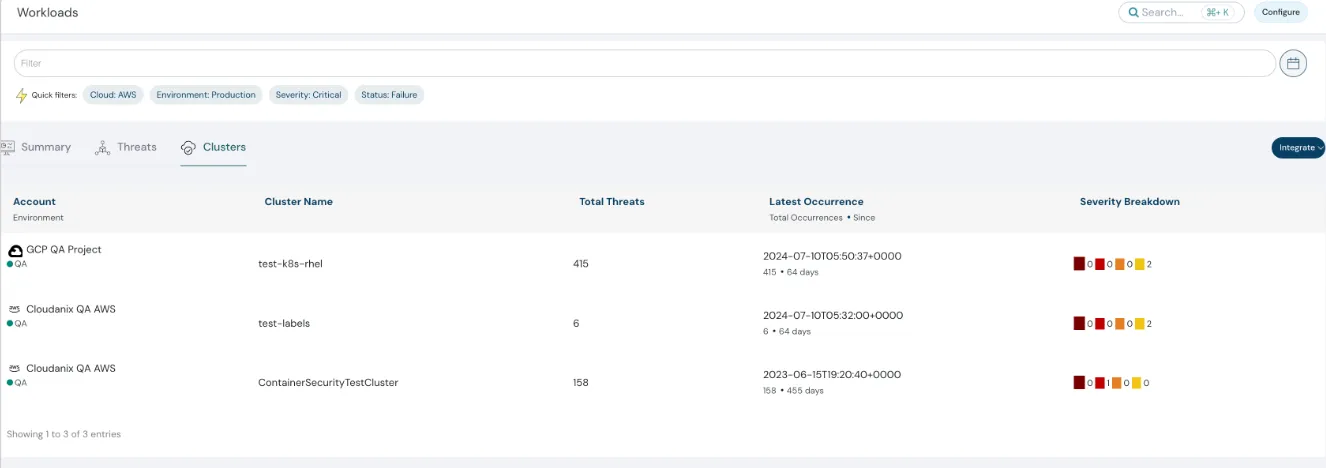
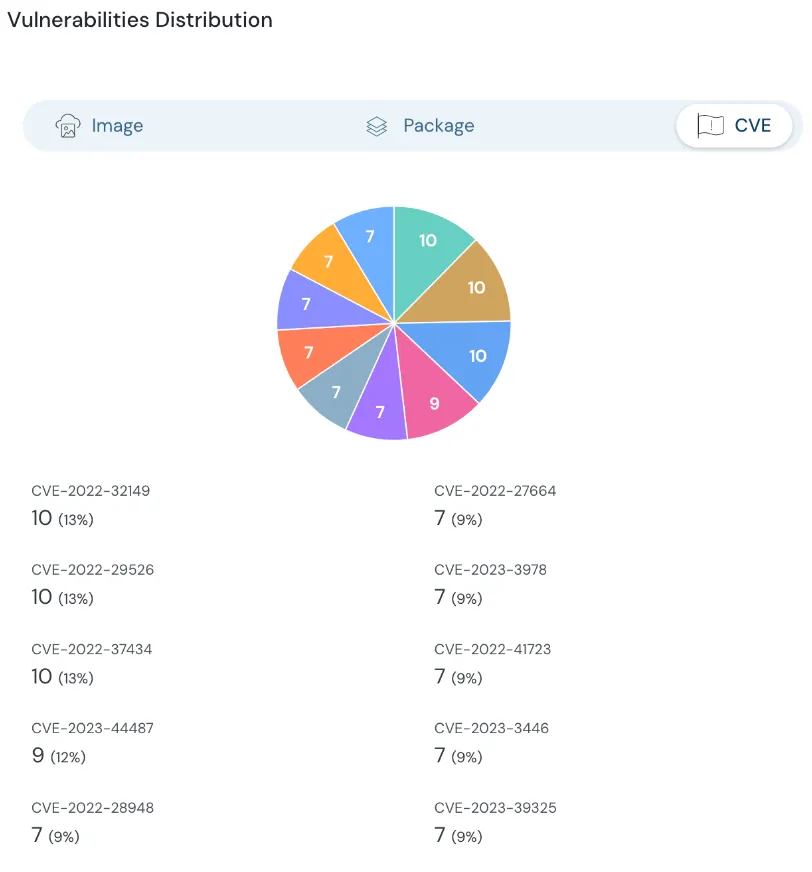
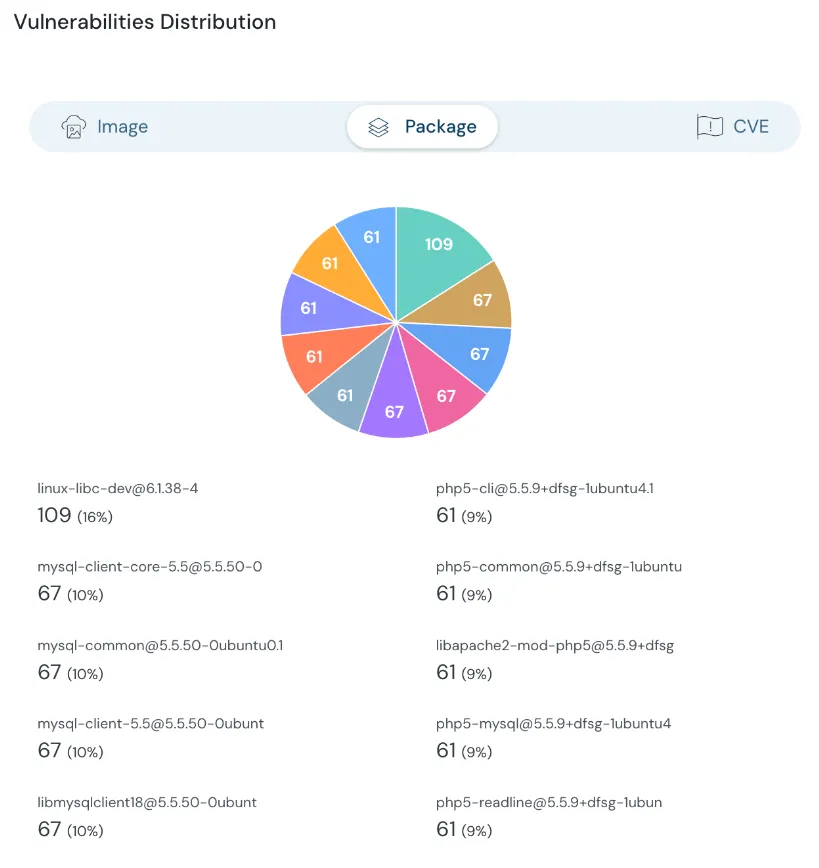
Contextualize Runtime Threats and Image Vulnerabilities
With the latest release, Cloudanix helps improve visibility into containers with both runtime threats and vulnerabilities from images running on those containers. This correlation helps you prioritize and find the most impactful containers to address first.
 Gain granular control over user permissions across AWS and GCP, preventing over-privileged access.
Gain granular control over user permissions across AWS and GCP, preventing over-privileged access.
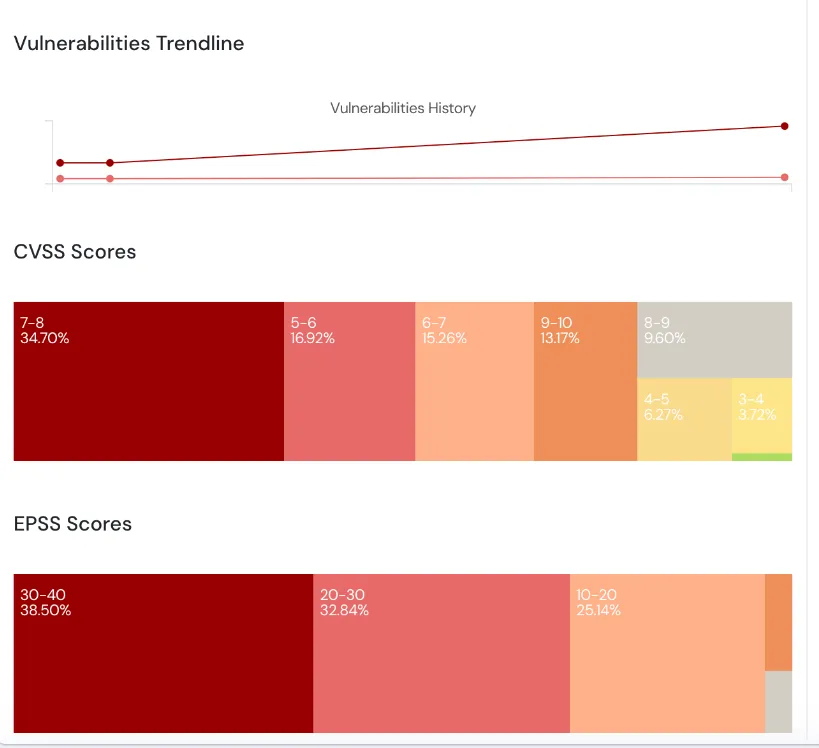
Prioritization Based on Exploitability
Cloudanix not only highlights CVSS scores, but also EPSS scores to understand exploitable vulnerabilities. It helps our users to understand and prioritize image vulnerabilities which need addressing.
 Elevate and revoke privileges for cloud users using Cloudanix console
Elevate and revoke privileges for cloud users using Cloudanix console
 Elevate and revoke privileges for cloud users using Cloudanix console
Elevate and revoke privileges for cloud users using Cloudanix console
 Elevate and revoke privileges for cloud users using Cloudanix console
Elevate and revoke privileges for cloud users using Cloudanix console
Cloudanix Blogs
- Top 10 revised code security best practices for developers
- Why IAM in the Cloud needs attention?
- What is Shift Left Security?
- What is Shared Responsibility Model?
Other Resources
- Cybersecurity Technology Adoption Cycle
- Secure By Default Comparison
- Detection Engineering and Threat Detection
- Building a Security Platform Engineering Team
- GitLab Patches Critical Flaw
TODO:// is not an option for Cloud Security
Ready to see your graph?
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Tuesday, Apr 14, 2026
Top 15 Cloud Misconfigurations in 2026 - How to Fix Them?
Most cloud breaches today are not the result of sophisticated zero-day exploits. They are the result of misconfiguration
Read MoreMonday, Apr 13, 2026
Top 18 Challenges of Cloud Security in 2026
The rapid adoption of cloud computing has brought unprecedented agility and scalability, making it a cornerstone of mode
Read MoreTuesday, Feb 10, 2026
The 2026 CNAPP Compliance Framework: Turning Audit from Crisis to Continuity
Introduction: The Death of the Point-in-Time Audit In the high-velocity cloud landscape of 2026, the traditional app
Read More