Slack App for JIT Access, Smarter Image Vulnerability Scanning and More
You asked, we delivered! We’re thrilled to announce the launch of our new Slack application for JIT (Just In Time) access. This highly requested feature streamlines access management, enabling users to request, accept, and revoke access—all without leaving Slack. But that’s not all! We’ve also enhanced our image vulnerability scanning with smarter tracking and improved visibility, helping you stay ahead of emerging threats and maintain a secure environment.
Request for Just In Time Access from Slack - No more app switching or context-switching
JIT Access is now integrated with Slack. Request on-demand cloud access right where you collaborate without leaving your favorite communication tool. Enhancing productivity and seamless & secure cloud access, all without leaving Slack.
Approval workflow is also integrated with Slack. Simplify cloud IAM permissions, enhance control – all with a quick Slack message, right from the platform your team uses every day.
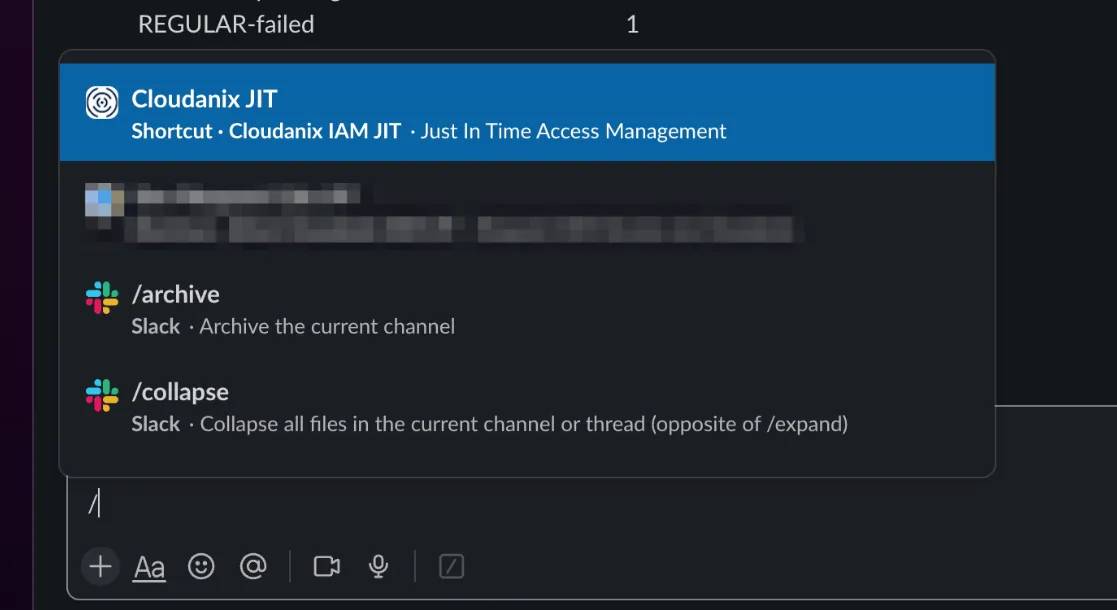 Request for Just In Time Access from Slack
Request for Just In Time Access from Slack
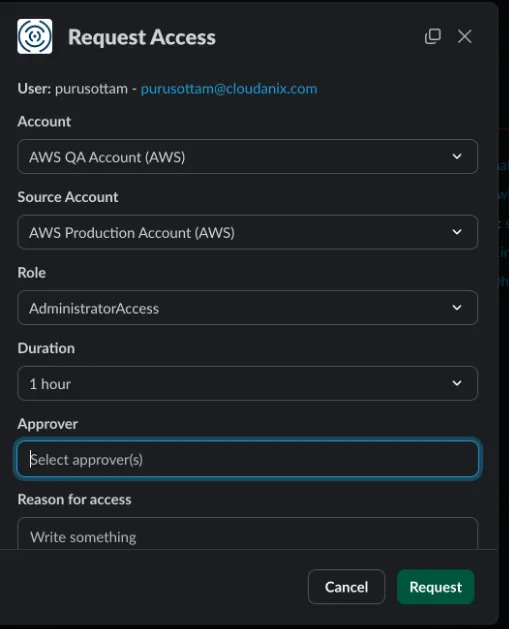 Requesting access from the Slack app
Requesting access from the Slack app
Smarter Image Vulnerability Scanning
Image Vulnerability Scanning has been upgraded to track drift between scan results of different image versions.
Improvements include highlighting newly introduced, resolved and unchanged vulnerabilities.
Understand your image’s security trajectory at a glance. Gain deeper insights into your security posture and stay ahead of threats with this enhanced visibility.
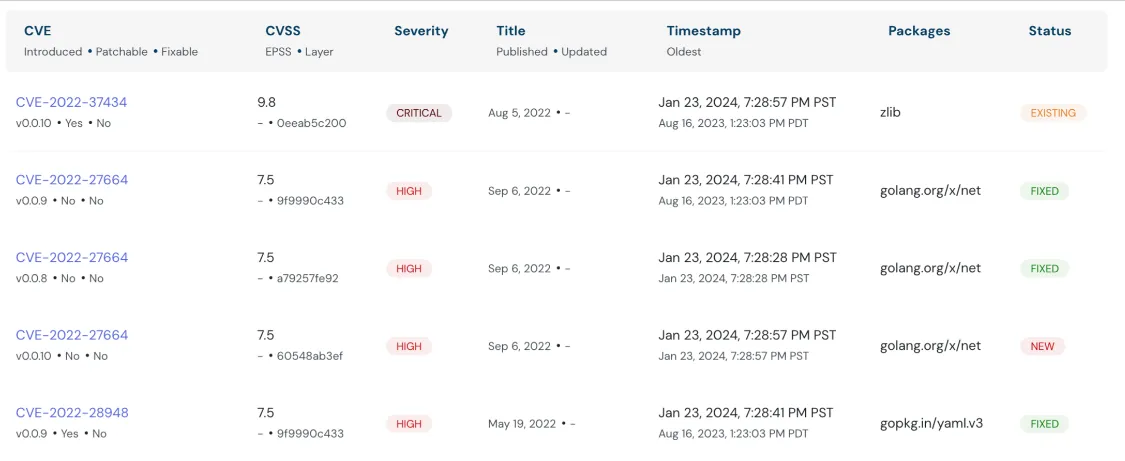 Understand your image’s security trajectory
Understand your image’s security trajectory
Cloudanix Resources
- Vulnerability Management - Deep dive
- Shared Responsibility Model - Securing every aspect of cloud
- Cloud Audit - Comprehensive assessment of cloud environment
Resources over Internet
- All Important updates prior to AWS re:Invent by Chris Farris
- Entrepreneurs Need to Stay Aware: Cybersecurity Threats May Directly Impact the Bottom Line
- eBPF Threat Modeling Guide for Security Usage
TODO:// is not an option for Cloud Security
Ready to see your graph?
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Tuesday, Apr 14, 2026
Top 15 Cloud Misconfigurations in 2026 - How to Fix Them?
Most cloud breaches today are not the result of sophisticated zero-day exploits. They are the result of misconfiguration
Read MoreMonday, Apr 13, 2026
Top 18 Challenges of Cloud Security in 2026
The rapid adoption of cloud computing has brought unprecedented agility and scalability, making it a cornerstone of mode
Read MoreTuesday, Feb 10, 2026
The 2026 CNAPP Compliance Framework: Turning Audit from Crisis to Continuity
Introduction: The Death of the Point-in-Time Audit In the high-velocity cloud landscape of 2026, the traditional app
Read More