JIT for Database, Security Health Monitoring, and Code Security Filters
Tighten your seatbelts, Cloudanix has made available the much-awaited JIT for Database. Our customers from the FSI, E-commerce, and HCLS segments being highly regulated, will benefit from this. There’s more for our customers across segments around VM security health monitoring status. Code security with additional filters for public/private repositories and code languages.
Request for Just In Time Access from Slack - No more app switching or context-switching
Our Identity Security Platform has already been securing cloud environments by enabling temporary, least-privilege IAM access, eliminating the risks of permanent cloud access. Now, we’re taking it a step further—extending JIT Access to databases to ensure sensitive data remains protected while allowing seamless, on-demand access when needed. By enforcing least privilege principles, JIT access ensures that sensitive databases remain secure while enabling seamless workflow access for developers and administrators.
With this enhancement, organizations can now eliminate permanent database credentials, need for a jumpbox, enforce strict access controls, minimize attack surfaces and reduce insider threats. Access is granted dynamically using time-bound tokens, ensuring that users only get the exact level of access required—when they need it, for as long as they need it. Whether it’s for cloud databases, critical applications, or infrastructure access, our dynamic, time-bound access controls provide granular security, auditability, and compliance enforcement in real time. Say goodbye to standing privileges and hello to secure, on-demand access.
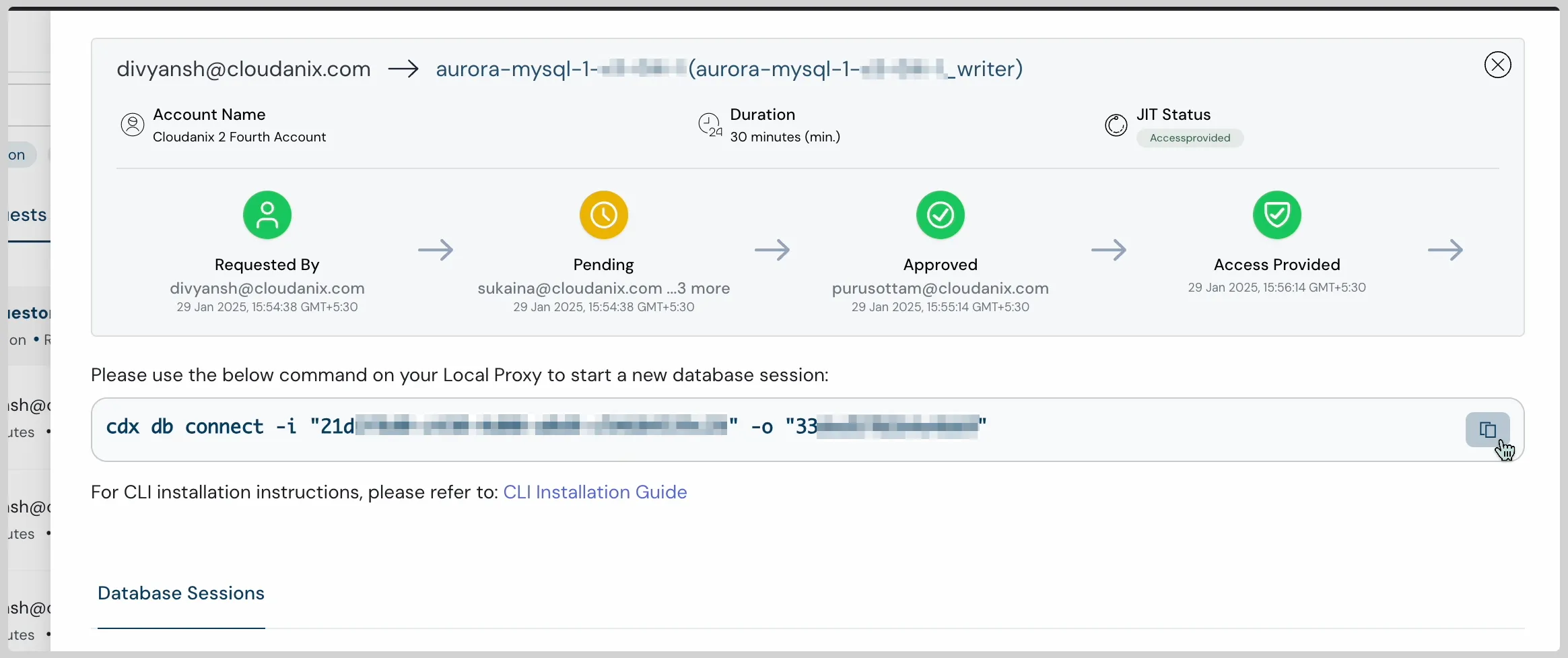
Request for Just In Time Access from Slack
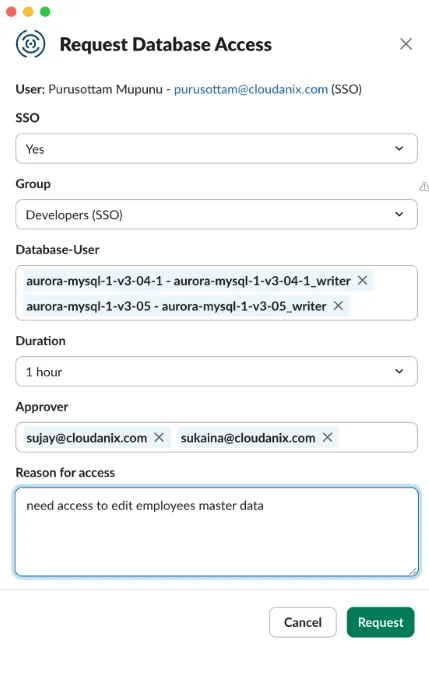
New session permissions
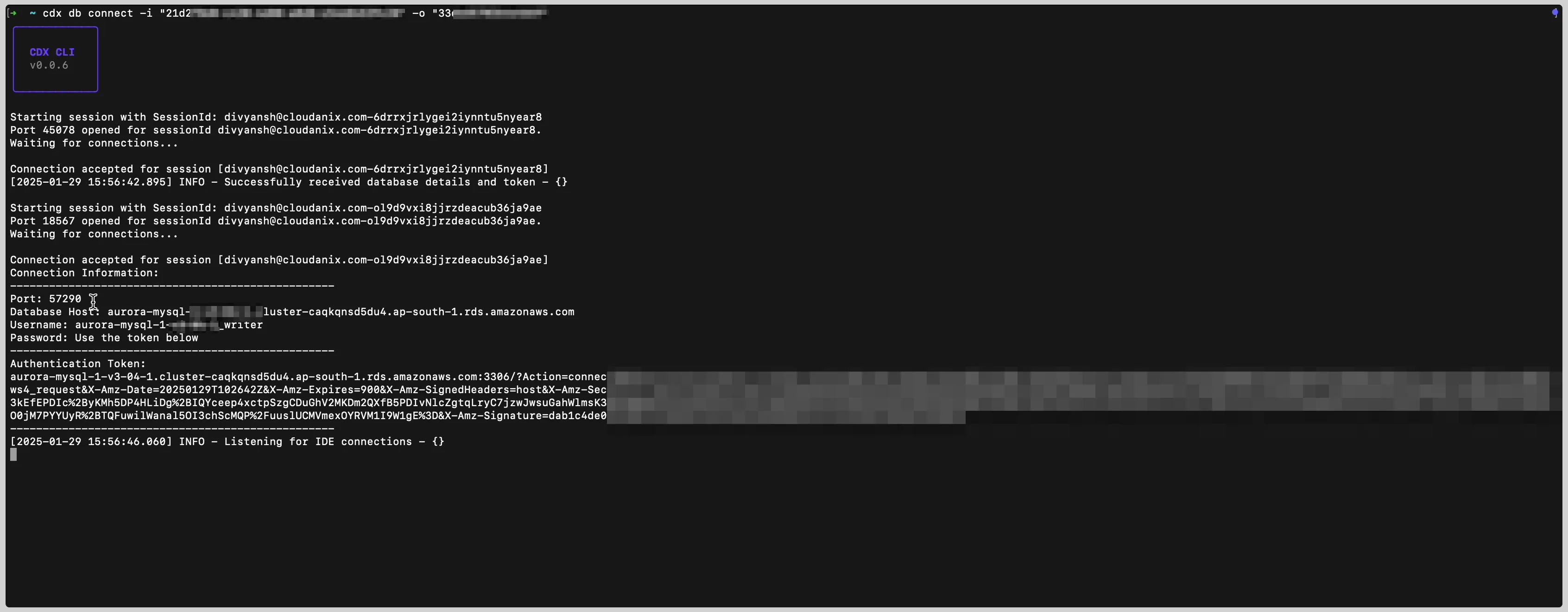
CLX for permission accepted screenshot
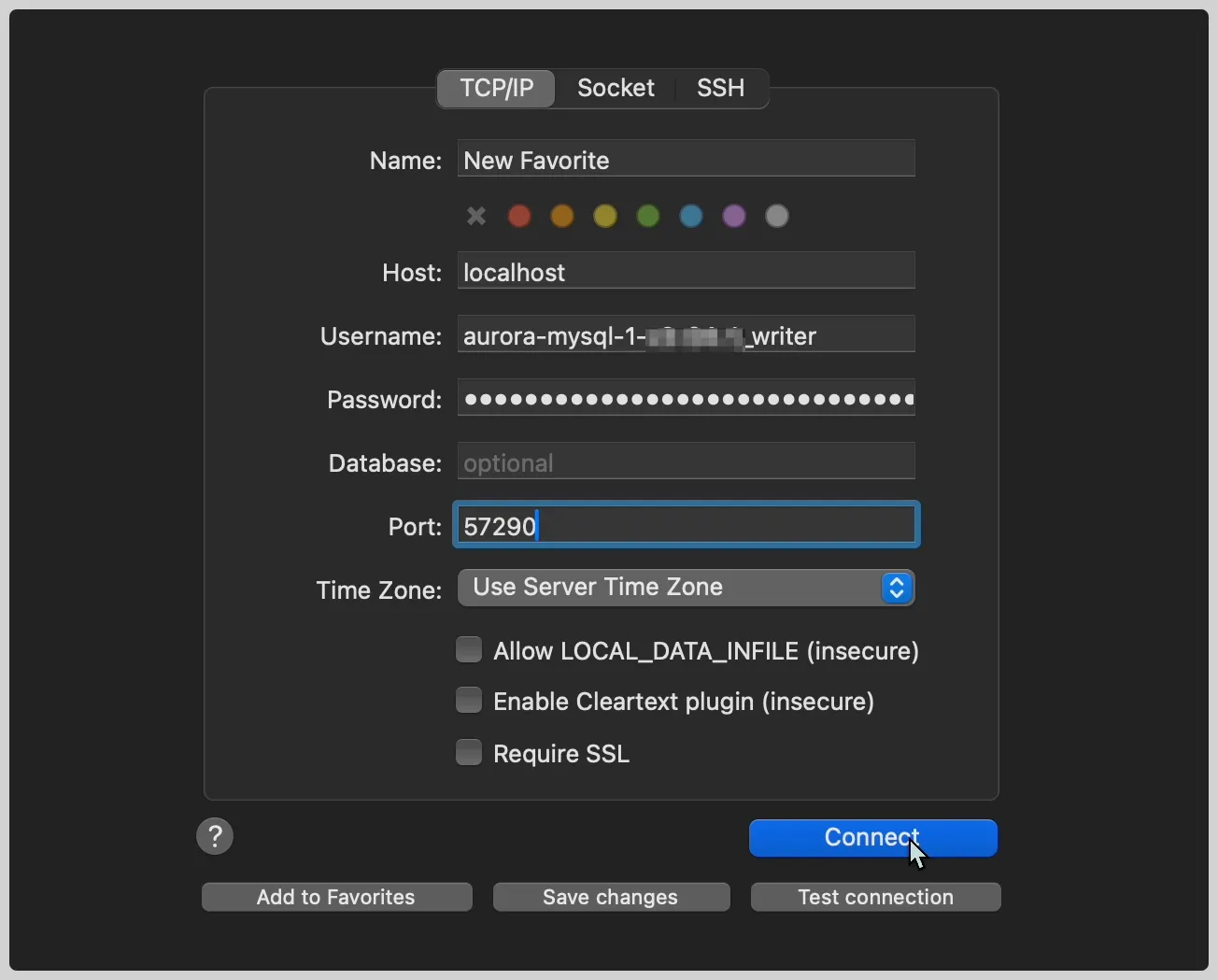 TCP/IP popup window for connection
TCP/IP popup window for connection
Stay up to date with Security Health Monitoring
With Security Health Monitoring, stay up to date with the monitoring status. Take swift action to remediate monitoring gaps directly from the Cloudanix Console.
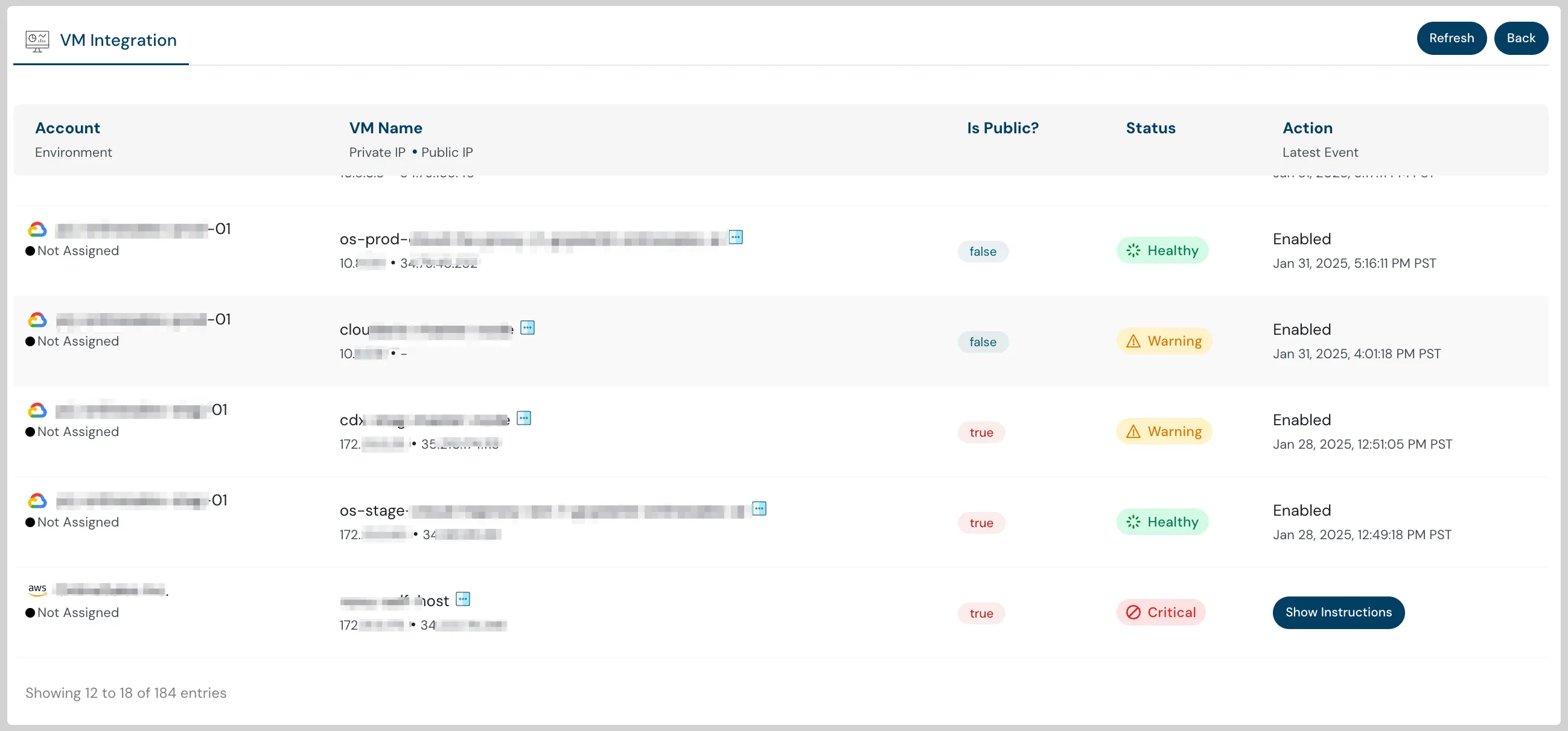 Cloudanix VM integration dashboard
Cloudanix VM integration dashboard
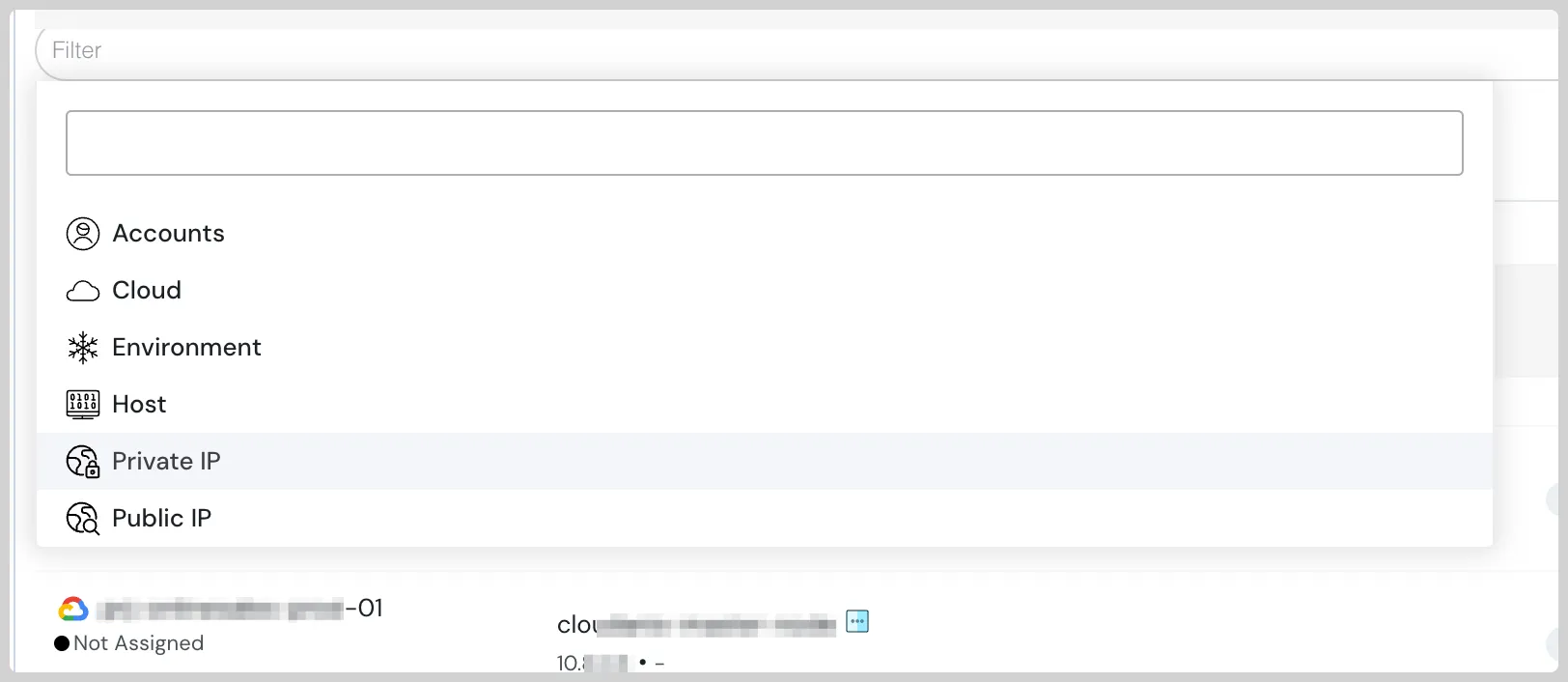 Cloudanix filter dashboard
Cloudanix filter dashboard
Monitor Public / Private Repositories across all code languages
With new filters, monitor both your Public and Private repositories. Also, use the Language filters to understand Code Security posture for all the environments used in the organization.
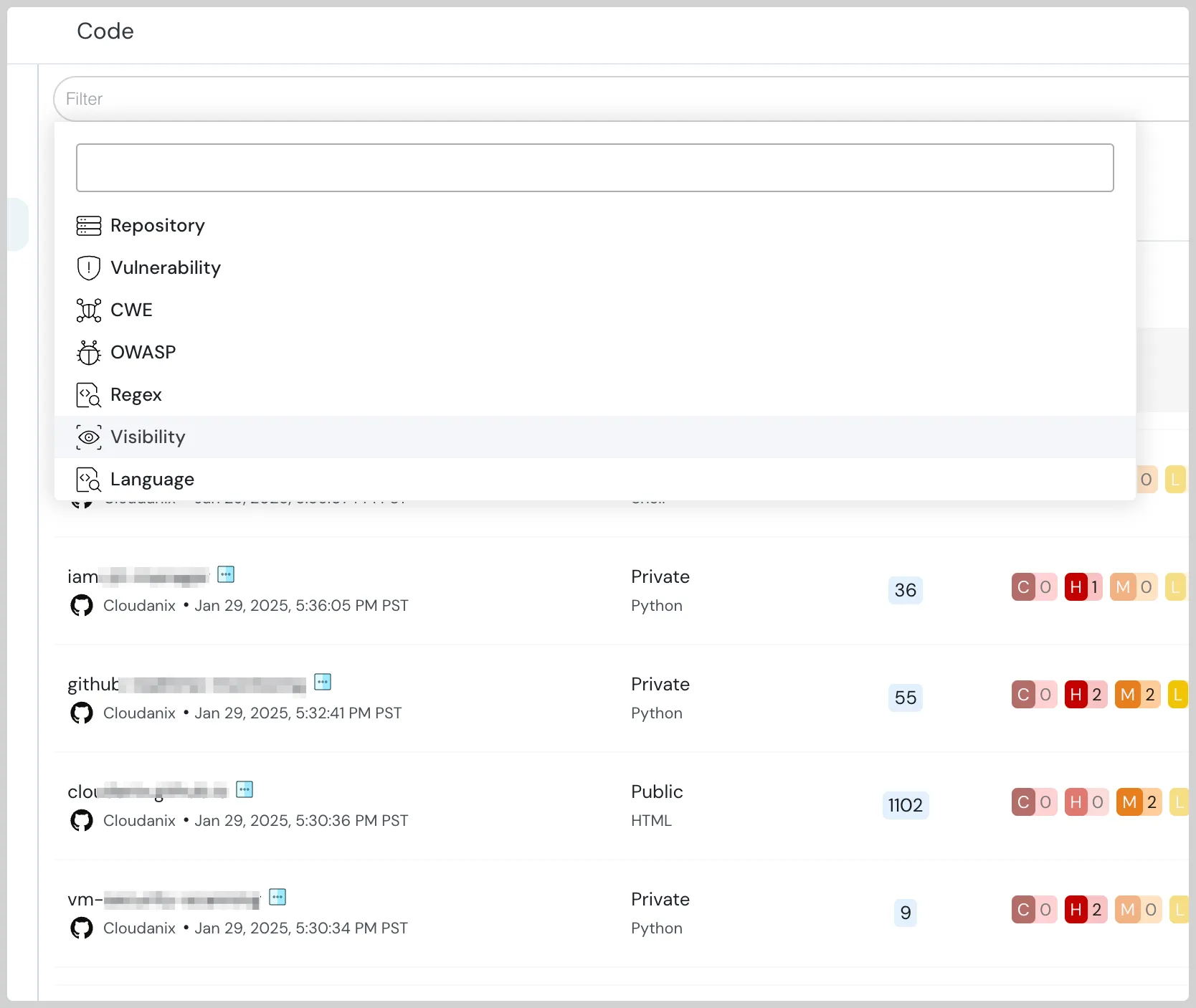 Cloudanix code security posture dashboard
Cloudanix code security posture dashboard
Cloudanix Resources
- Building Security Using Generative AI
- What is Incident Response? - Detailed Explanation
- Free Vendor Risk Assessment Template including Questionnaire
Resources over Internet
Ready to see your graph?
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Tuesday, Apr 14, 2026
Top 15 Cloud Misconfigurations in 2026 - How to Fix Them?
Most cloud breaches today are not the result of sophisticated zero-day exploits. They are the result of misconfiguration
Read MoreMonday, Apr 13, 2026
Top 18 Challenges of Cloud Security in 2026
The rapid adoption of cloud computing has brought unprecedented agility and scalability, making it a cornerstone of mode
Read MoreTuesday, Feb 10, 2026
The 2026 CNAPP Compliance Framework: Turning Audit from Crisis to Continuity
Introduction: The Death of the Point-in-Time Audit In the high-velocity cloud landscape of 2026, the traditional app
Read More