Workload Protection & Platform Enhancements
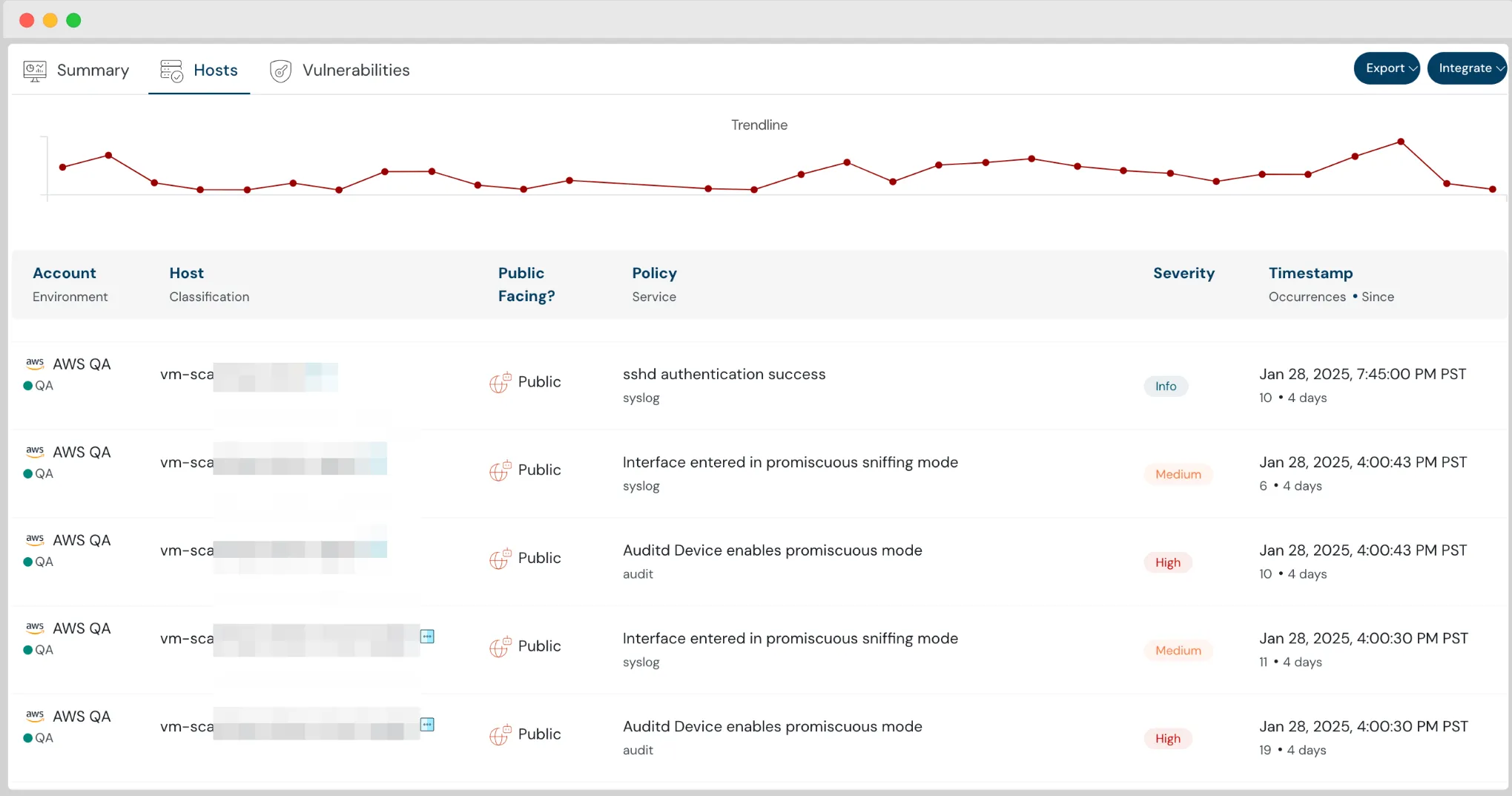
Protect Virtual Machines from Intrusion using Cloudanix IDS
The launch of Intrusion Detection System (IDS) for Virtual Machines further strengthens our Host Security Platform. As organizations scale their cloud infrastructure, attackers are constantly looking for vulnerabilities to exploit. Our IDS for Virtual Machines provides real-time threat detection, ensuring that malicious activities, unauthorized access attempts, and suspicious behaviors are instantly identified and addressed.
We continuously monitor VM traffic, logs, and system activities, leveraging behavioral analytics and signature-based detection to spot potential security threats. Whether it’s detecting zero-day attacks, insider threats, or anomalous access patterns, our IDS ensures that your virtual machines remain protected with continuous monitoring and automated alerts.
Request for Just In Time Access from Slack
Easily request and approve Just In Time access directly from Slack for faster workflows.
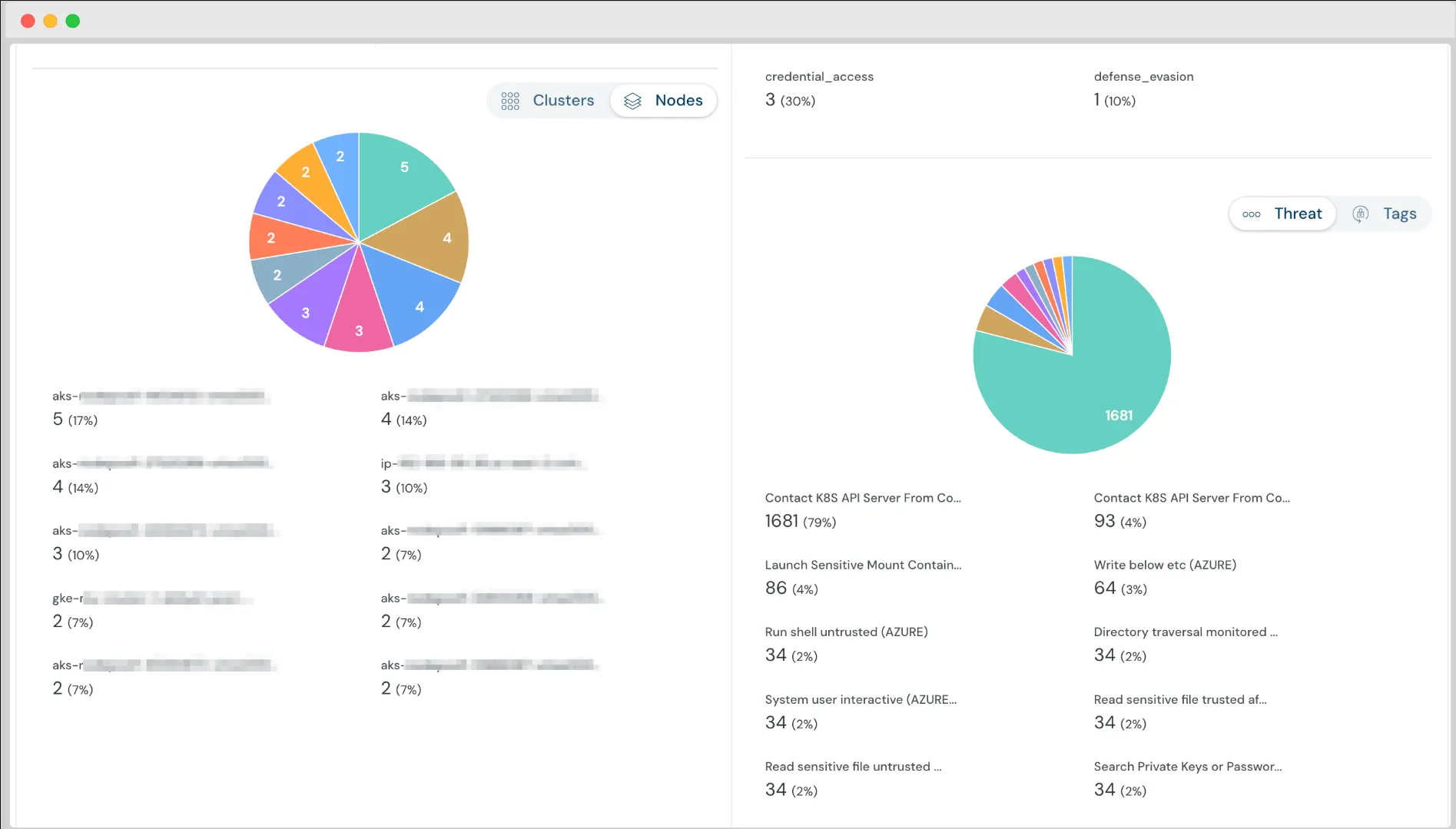
Kubernetes Runtime Security Monitoring at Node Level
Now, slice and dice runtime security threats at a node level — enabling you to analyze and prioritize node pools needing attention.
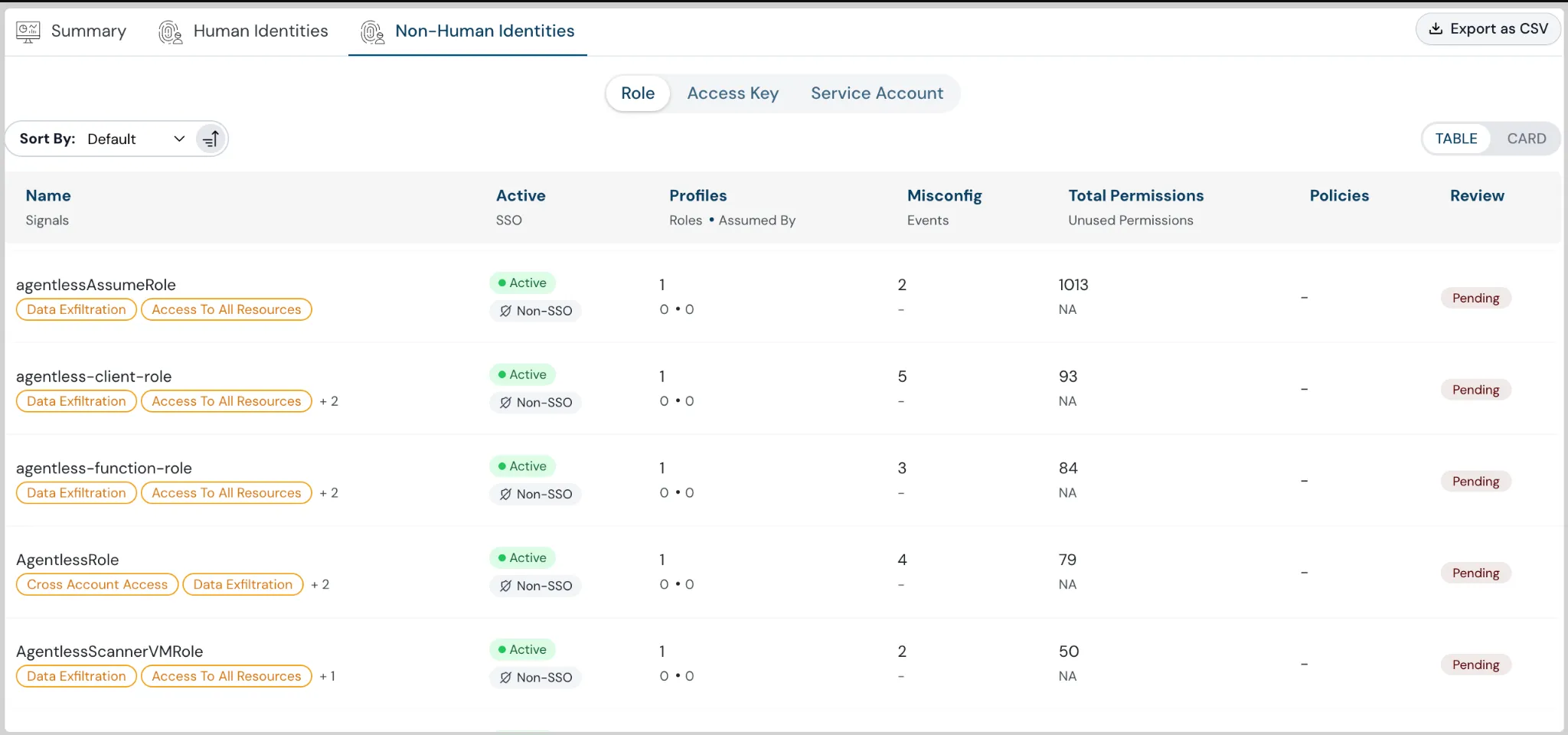
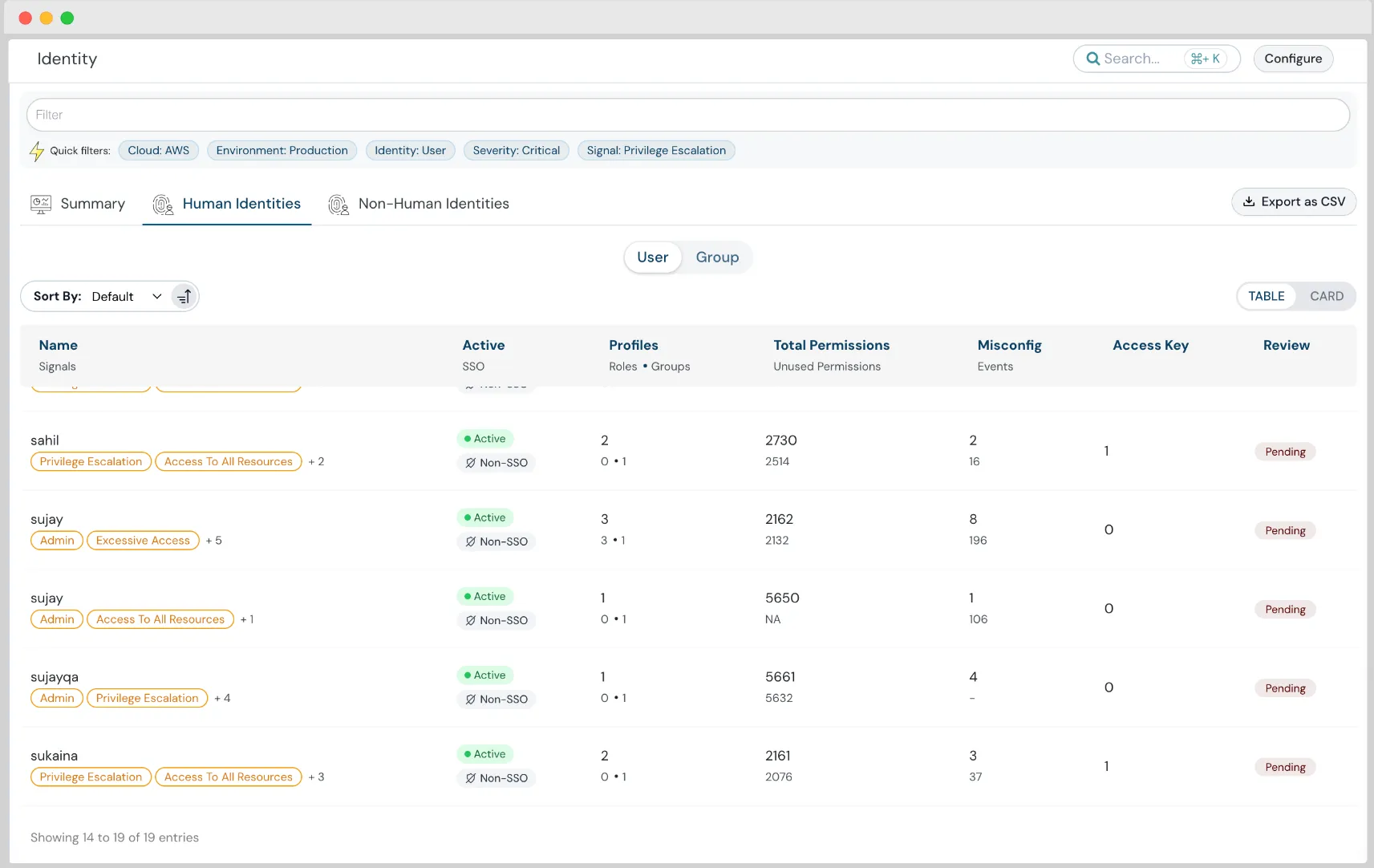
Identities Permission Analysis with Human and Non-Human Identity Segregation
With the latest release, gain deep visibility into identity risks. We now segregate human and non-human identities, making it easier to identify unused permissions, overly permissive identities, and cross-account access.
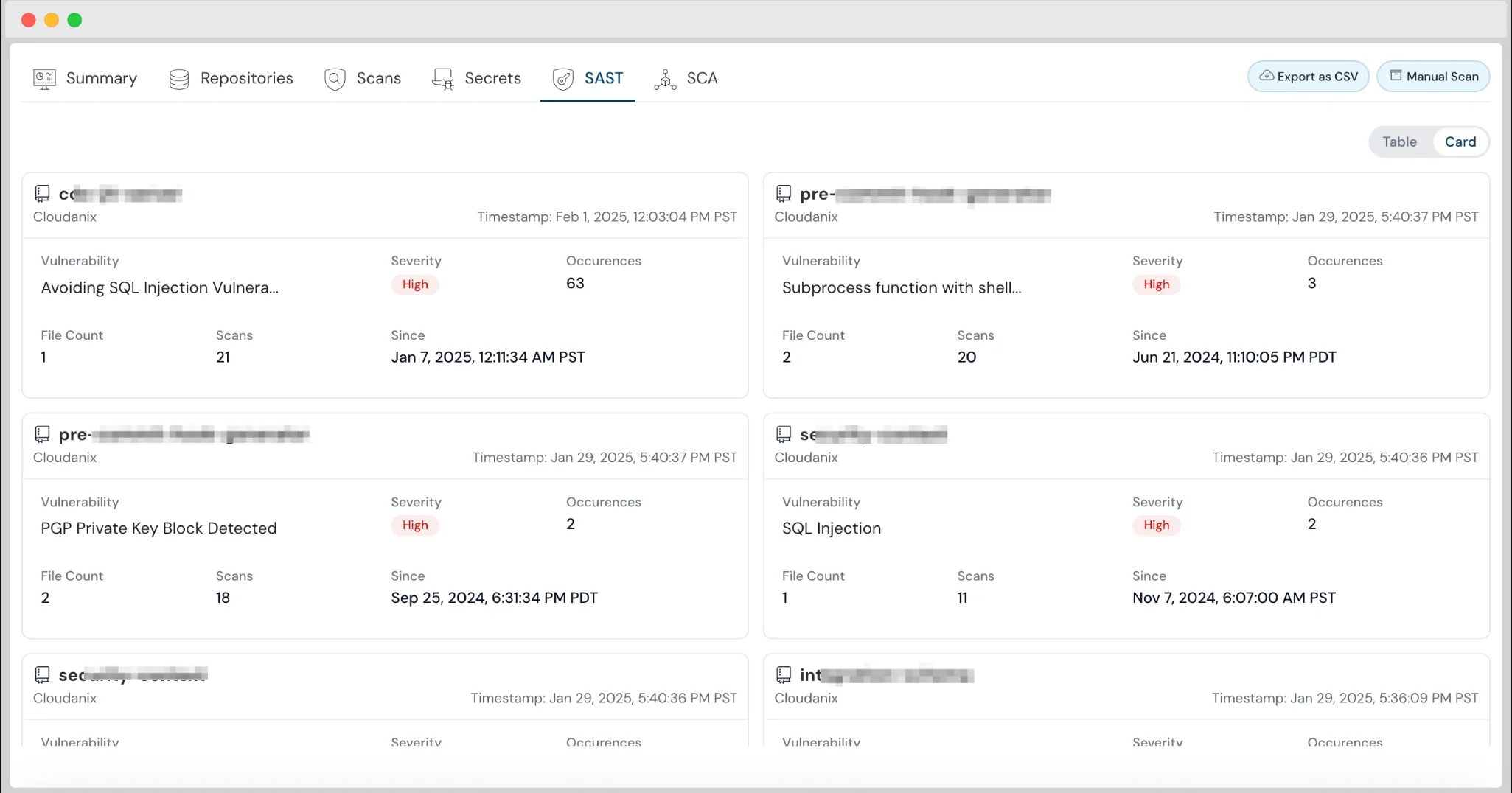
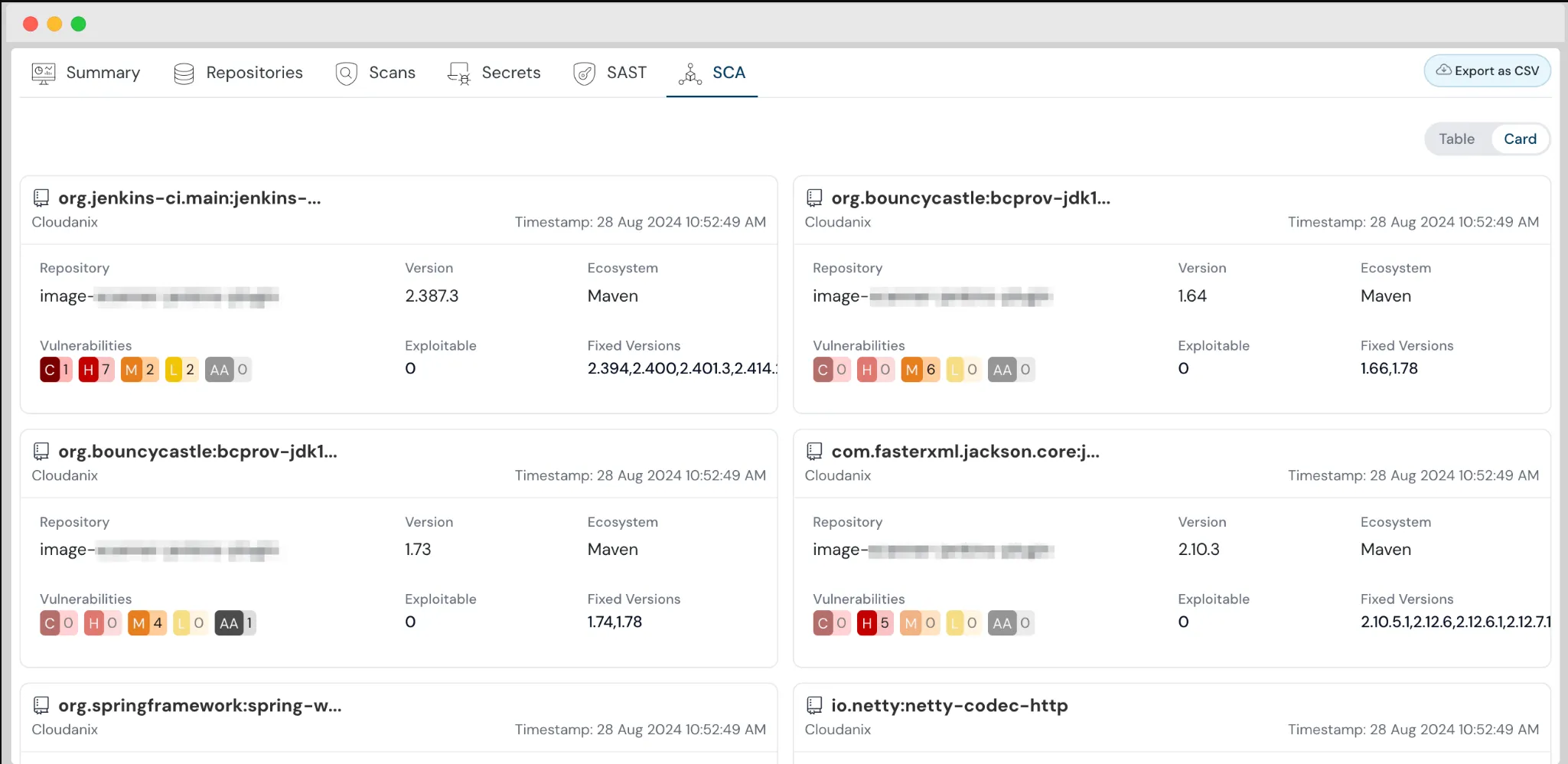
Enhanced Card Views for Code Security
Code Security is enhanced to present findings in a new Card view, helping you visualize issues in a more detailed and structured manner.
Cloudanix Blogs & Resources
- Source Code Security Best Practices
- What is Code Security?
- Top 10 Revised Code Security Best Practices for Developers
Industry News & External Reads
- OWASP Non-Human Identity (NHI) Top 10 - 2025
- AI Agent Identity: It’s Just OAuth — by Maya Kaczorowski
- Why Running as Root in Kubernetes Containers is Dangerous — by Marcin Wasiucionek
TODO:// is not an option for Cloud Security
Ready to see your graph?
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Tuesday, Apr 14, 2026
Top 15 Cloud Misconfigurations in 2026 - How to Fix Them?
Most cloud breaches today are not the result of sophisticated zero-day exploits. They are the result of misconfiguration
Read MoreMonday, Apr 13, 2026
Top 18 Challenges of Cloud Security in 2026
The rapid adoption of cloud computing has brought unprecedented agility and scalability, making it a cornerstone of mode
Read MoreTuesday, Feb 10, 2026
The 2026 CNAPP Compliance Framework: Turning Audit from Crisis to Continuity
Introduction: The Death of the Point-in-Time Audit In the high-velocity cloud landscape of 2026, the traditional app
Read More