Enhanced Vulnerability Management, Fine-Tune Code Security Settings & More
Fueled by your invaluable feedback, Cloudanix continues to evolve! This update prioritizes empowering you with better data consumption. Experience granular filtering controls, tailor your code security with advanced settings, and leverage enhanced reporting capabilities. We are committed to providing you with the tools you need to make informed decisions and achieve optimal security outcomes.
Read to see what we have cooked up for you.
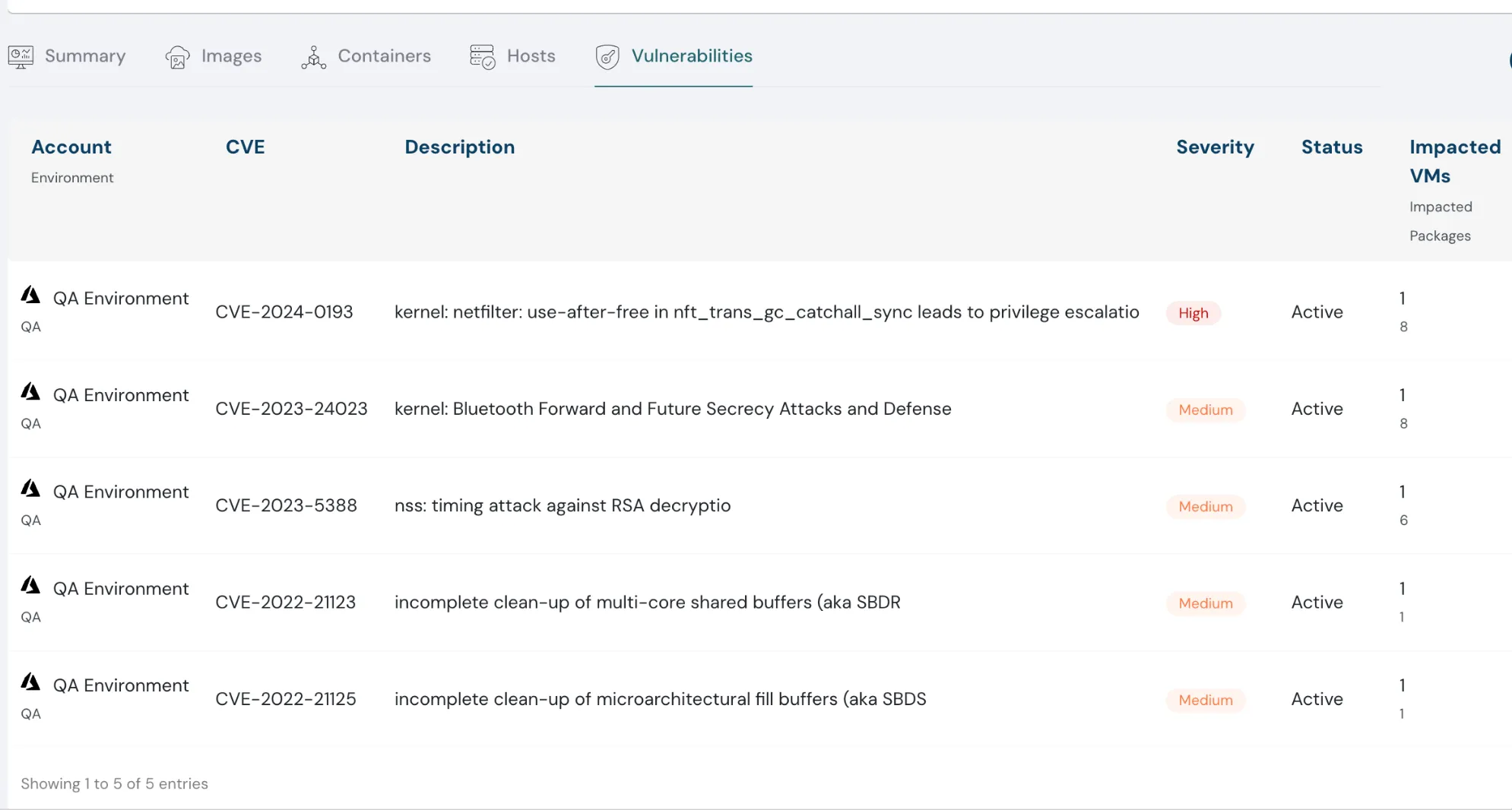
Vulnerability Management for Hosts
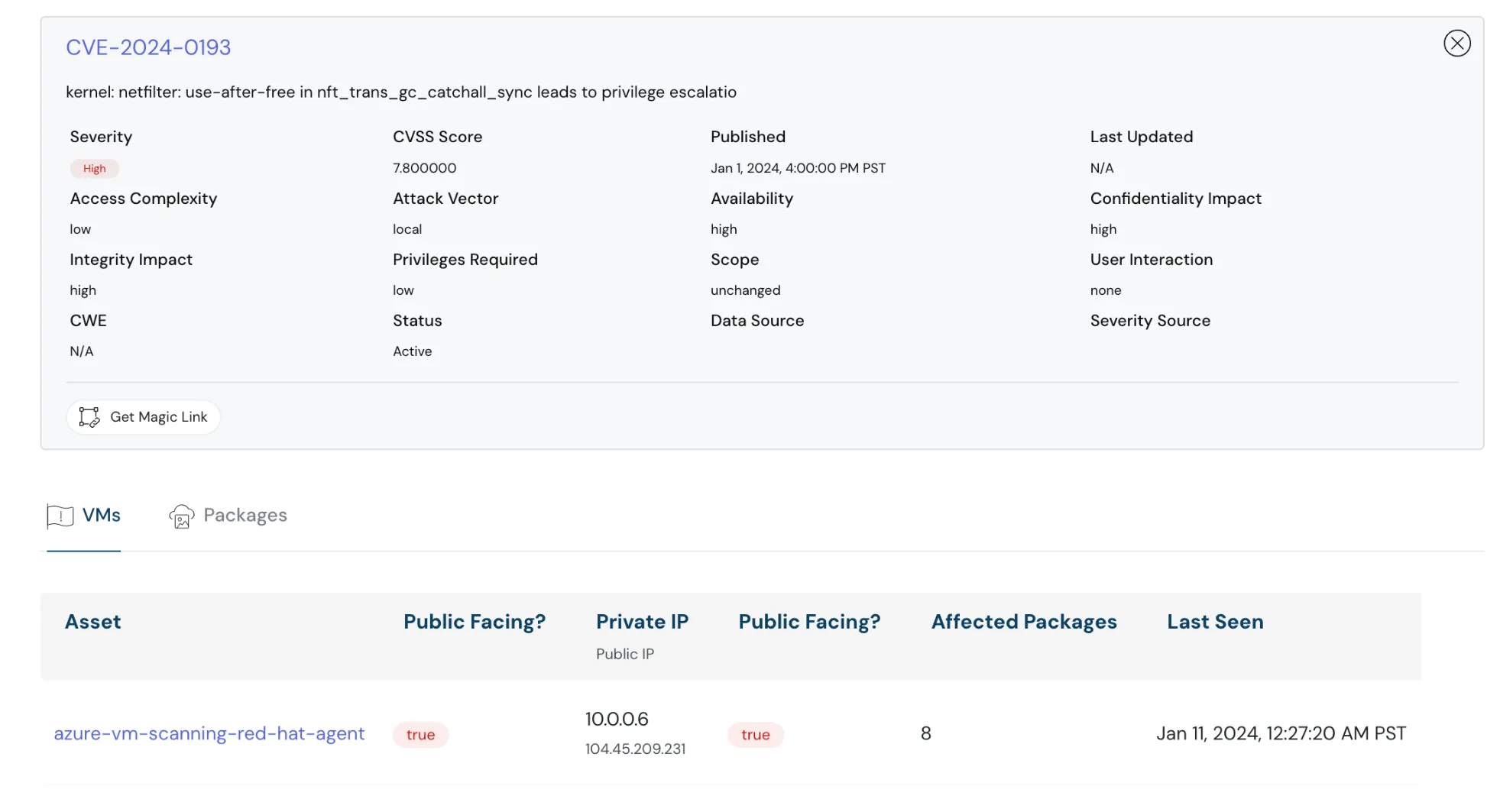
Now, gain complete control over your virtual machine security. See all open vulnerabilities at a glance, with detailed information on severity, exploit complexity, attack vectors, and other crucial factors. This enhanced visibility empowers you to prioritize threats effectively, streamlining your vulnerability triaging and remediation process.
Paired with existing File Integrity Monitoring and Malware Analysis, VM Vulnerabilities Management forms a powerful shield, keeping you one step ahead of attackers.
List of vulnerabilities in cloud environment — Cloudanix dashboard
Detailed information about the severity — Cloudanix dashboard
Improved Filter Control
Our all-new Filter Control empowers you to dissect your findings with better granularity. Simply choose your desired “Area of Filter,” then drill down and select the specific values you need.
This interface puts you in complete control, allowing you to effortlessly pinpoint the exact information you are searching for.
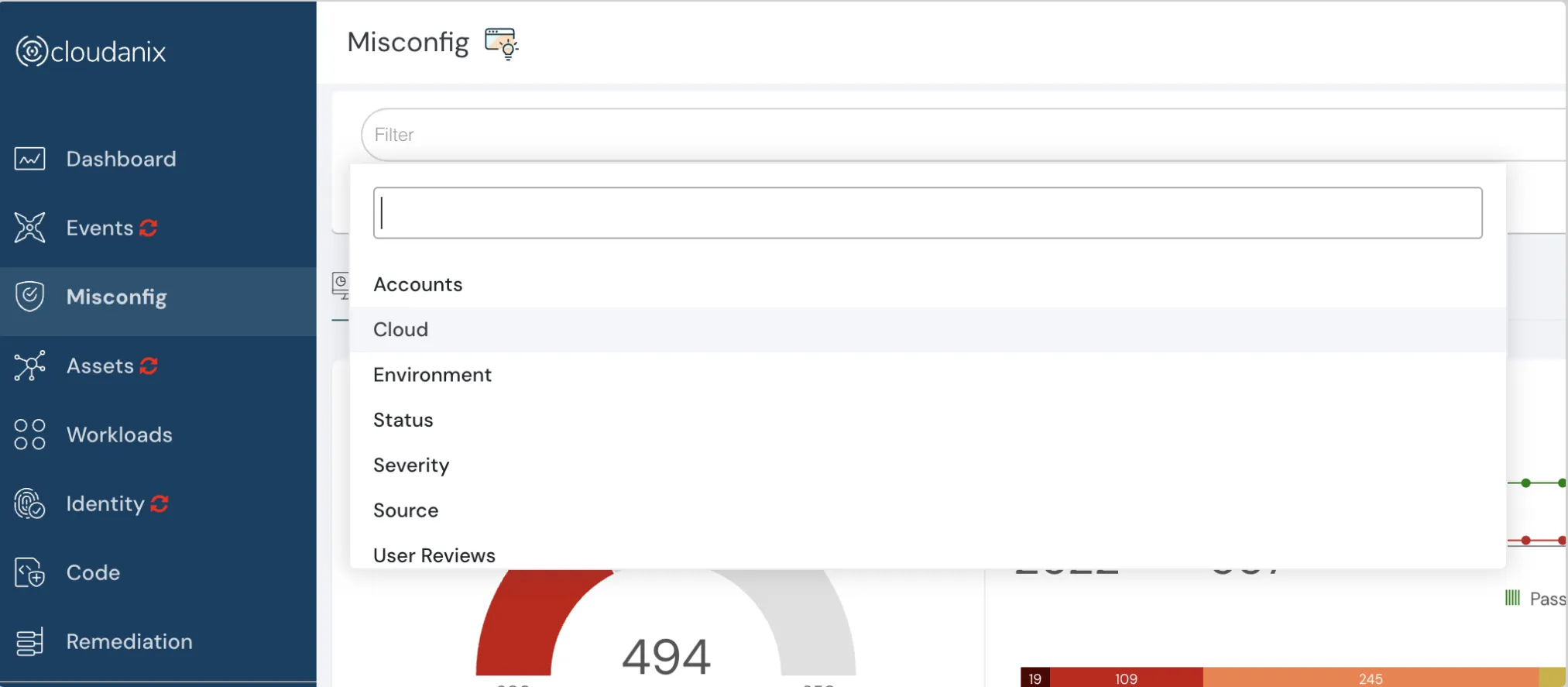 All new filter control feature
All new filter control feature
<img src=“/images/changelog/enhanced-vulnerability-management/enhanced-vulnerability-managementSS4.webp” alt=“Software Screen-Shot” class=“rounded-2xl border-10 border-gray-50”
/> Controls based on severity
Code Security Settings
Each practitioner looks at Code Security in a slightly different way. To empower this diversity, we are introducing advanced Code Security Settings.
This allows you to define:
- Capabilities to use
- Scan Triggers
- Full Scan Schedule (Daily, Weekly, Monthly, etc.)
- PR Failure conditions (Critical Count, High Count, Allowed CVEs, etc.)
- Jira Integration parameters
This flexibility ensures Code Security that adapts to your development process, optimizing efficiency and maximizing security.
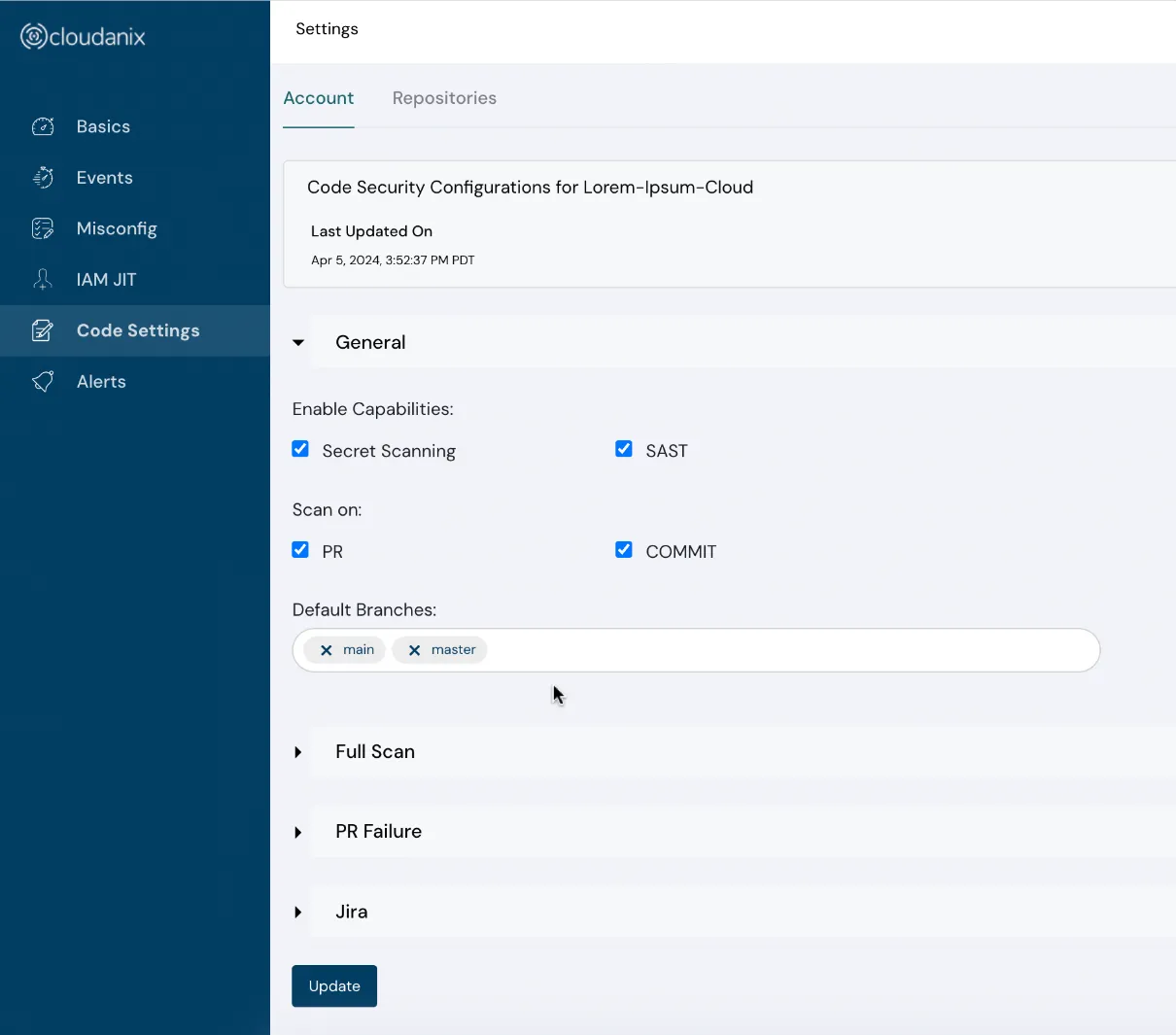
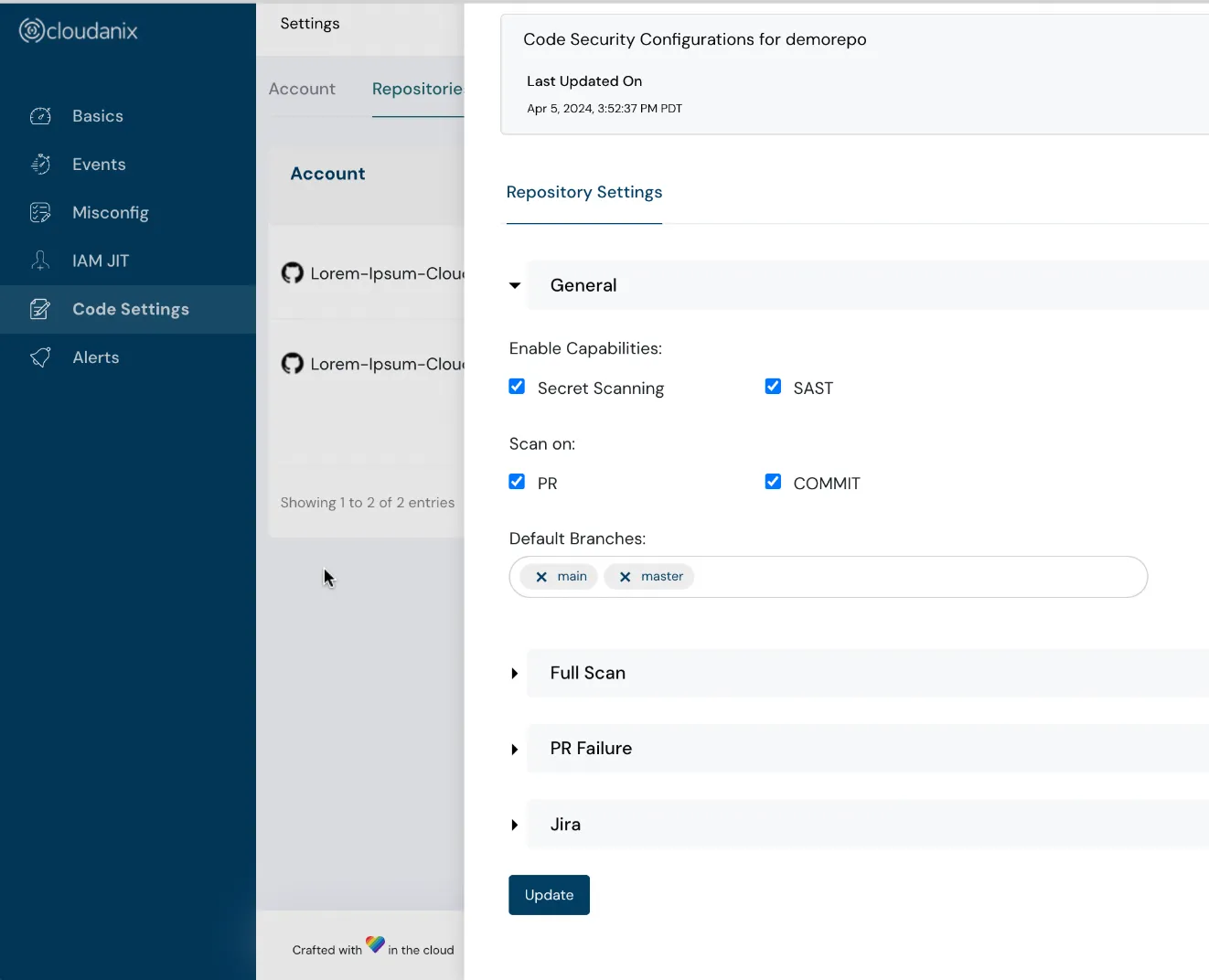
Code security settings screenshots
PDF Reports for Code & Host Security
Now you can generate detailed Security Posture Reports for Code Security and Host Security, and share them with other stakeholders inside and outside of the organization.
Blogs
- Top 12 Container Security Best Practices
- Unveiling Cloud Console Link Project - Your Shortcut to Cloud Resources
Additional Resources
Industry News
- Recipe for Scaling Security - David Dworken
- K8s Secure Design - Doyensec
- Logging at the scale of Cloudflare
- Supply Chain Attacks to rule them all - Adnan Khan
- AWS Security Mind Map - Artem Marusov
TODO:// is not an option for Cloud Security
Ready to see your graph?
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Tuesday, Apr 14, 2026
Top 15 Cloud Misconfigurations in 2026 - How to Fix Them?
Most cloud breaches today are not the result of sophisticated zero-day exploits. They are the result of misconfiguration
Read MoreMonday, Apr 13, 2026
Top 18 Challenges of Cloud Security in 2026
The rapid adoption of cloud computing has brought unprecedented agility and scalability, making it a cornerstone of mode
Read MoreTuesday, Feb 10, 2026
The 2026 CNAPP Compliance Framework: Turning Audit from Crisis to Continuity
Introduction: The Death of the Point-in-Time Audit In the high-velocity cloud landscape of 2026, the traditional app
Read More