Code Quality Gate Thresholds, Infrastructure Classifications and More
Code security took center stage in our sprints last month. Enhancing and building deeper checks and capabilities that ensure the code checked in is safe from exploits. Some of the things we’ve worked on are enforcing thresholds for PRs using Cloudanix Quality Gate, consolidated report with Code Insights, use tagging for classification of your application and data, and more.
Enforce Thresholds for Your PRs Using Cloudanix Quality Gate
With Cloudanix Quality Gate capability, Security Teams and Engineering Managers can enforce thresholds for PRs. This enables Developers to focus on the most important security gaps in the world of noise.
Thresholds include Vulnerability Counts by Severity, Allowed & Denied CVEs, Allowed CWEs, etc.
Enforce thresholds for your PRs using Cloudanix Quality Gate
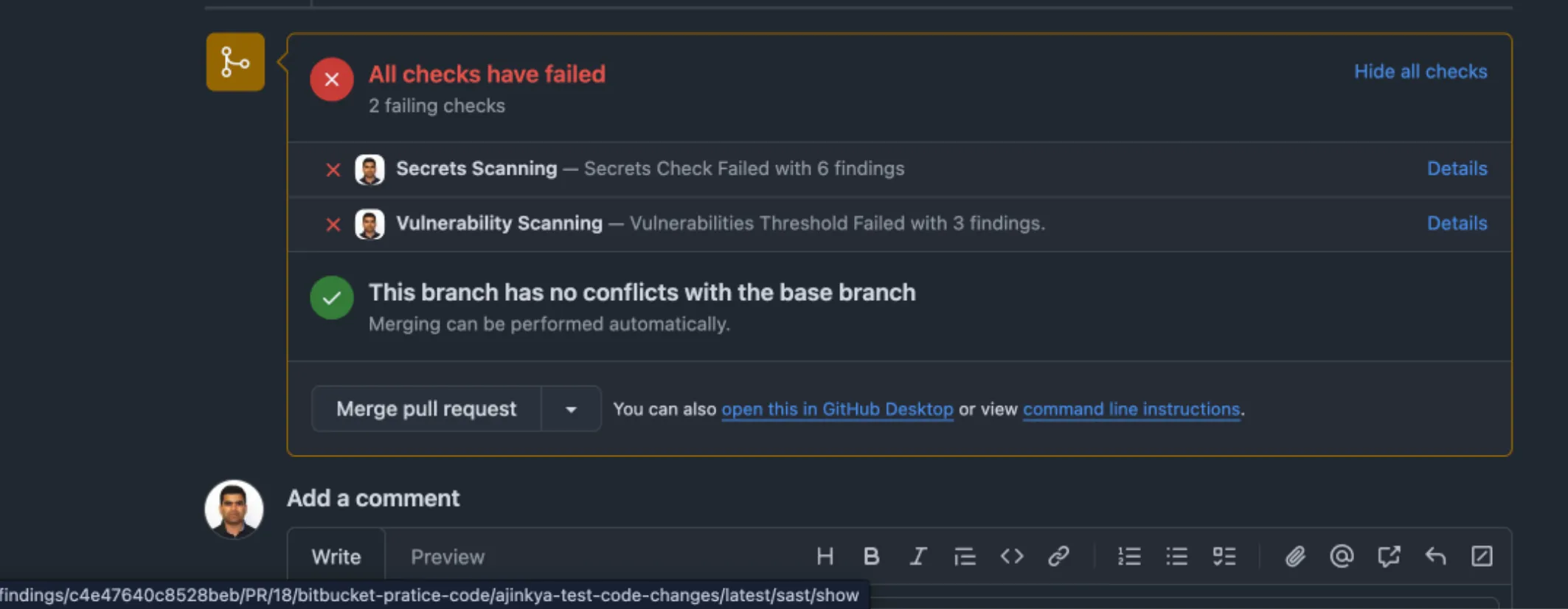
One Consolidated Report with Code Insights
In Bitbucket, integrate Cloudanix to generate Annotations. Improve code quality in the Pull Requests via the Code Review process in the Reports.
Annotations include capabilities like Secrets Detection, Vulnerability Scanning (SAST) and Supply Chain Security (SCA).
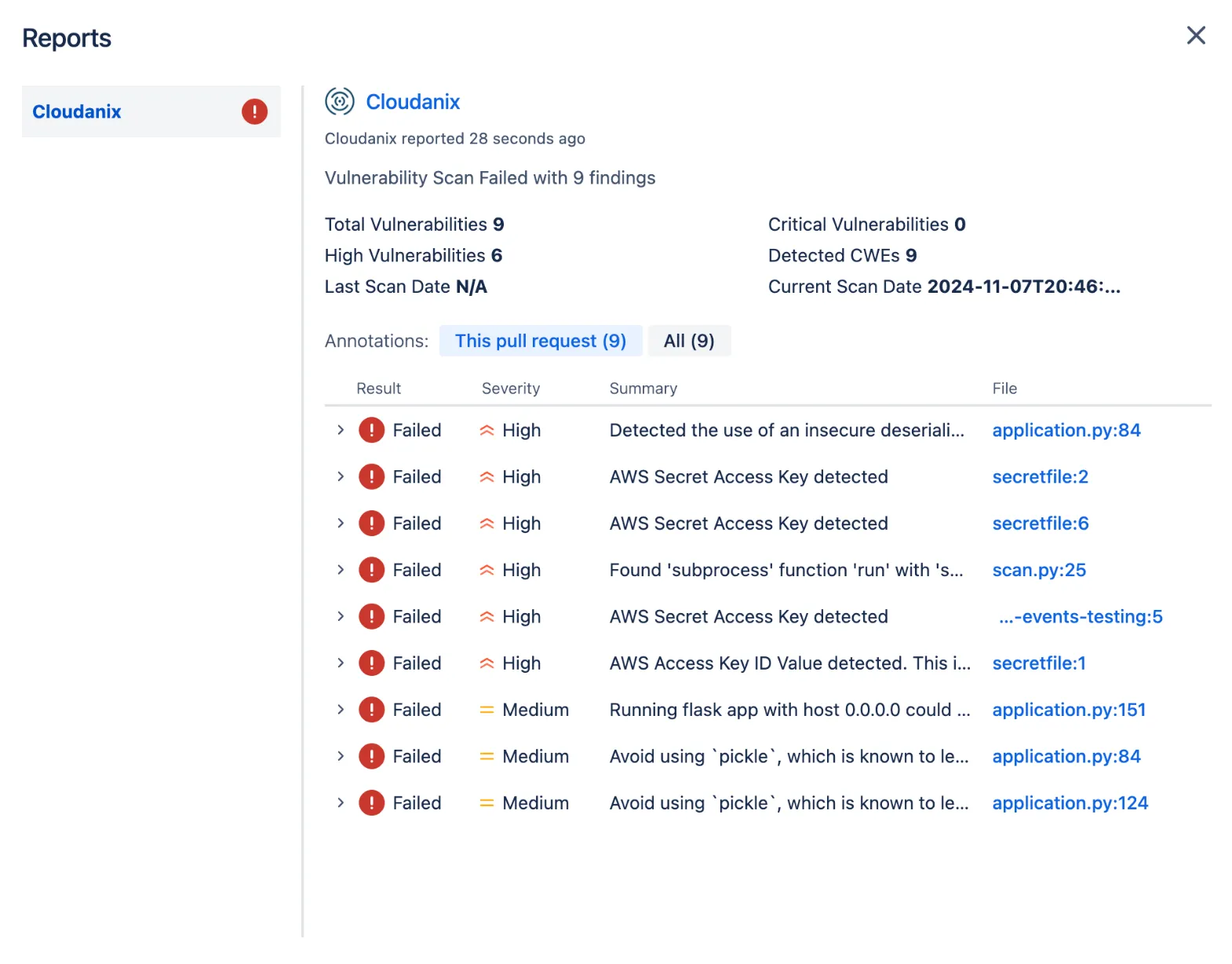 One consolidated report with Code Insights
One consolidated report with Code Insights
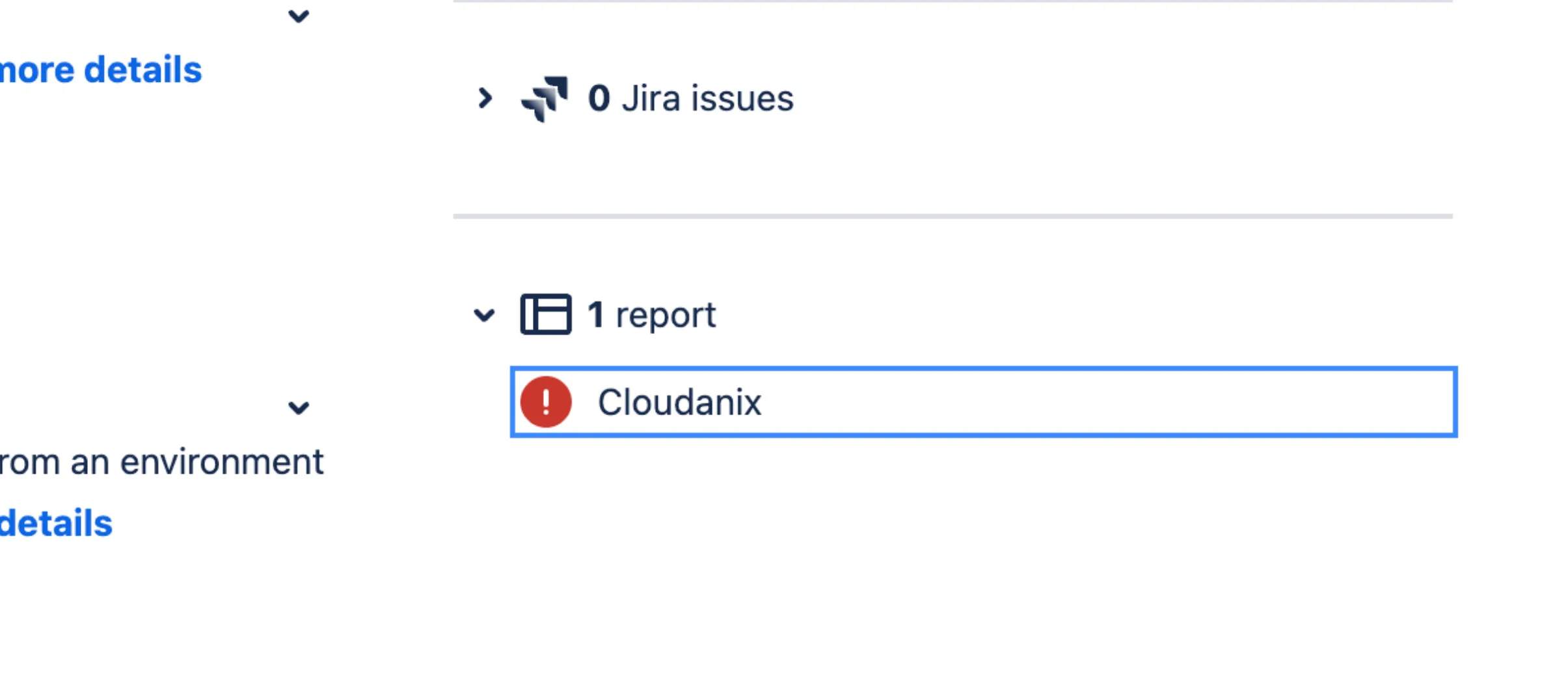 One consolidated report with Code Insights
One consolidated report with Code Insights
Understand Sensitivity of Your Infrastructure Using Classifications
Not all infrastructure is created equal. With the latest release, tag your applications and data with different classifications.
This helps Cloudanix understand the sensitivity of the infrastructure and data.
Use the classifications to slice and dice better in the Platform.
 Tag your Applications and Data with different classifications
Tag your Applications and Data with different classifications
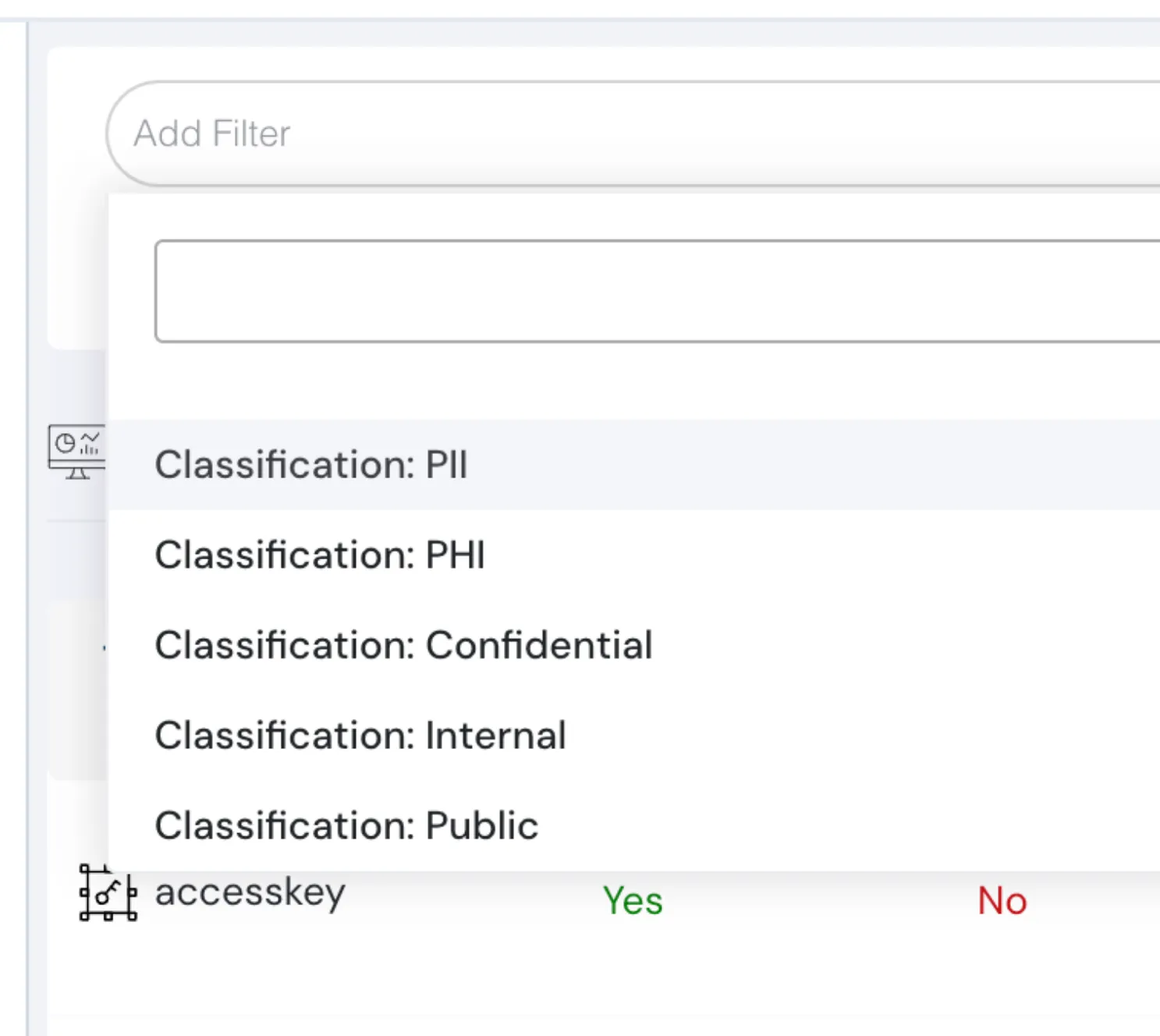 Tag your Applications and Data with different classifications
Tag your Applications and Data with different classifications
Cloudanix Resources
- The Science of Hiring Cybersecurity Professionals
- Platform Engineering - A deep dive
- Comprehensive Guide to Threat Modeling
- Security that goes beyond your traditional security practices - Zero Trust Security
- Restorative Justice Framework in Cloud Security
Resources over Internet
- Simplifying XSS Detection with Nuclei
- Cloud Access Management Maturity Model - Part 1 by Rowan Udell
- Zero Trust Maturity Model by CISA
- Research - CyberGreen
- Threat Modeling: Designing for Security (Book) by Adam Shostack
TODO:// is not an option for Cloud Security
Ready to see your graph?
Connect a cloud account in under 30 minutes. See every finding rooted in identity, asset, and blast radius — with a fix path attached.
Book a DemoBlog
Read More Posts
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Friday, May 29, 2026
Best Wiz Alternatives in 2026: A Technical Side-by-Side Comparison for Security Teams
Wiz changed how the industry thinks about agentless cloud security. It also left four major surfaces uncovered. And in 2
Read MoreThursday, May 21, 2026
Cloud Asset Management: The Complete 2026 Guide for Multi-Cloud Teams
As we navigate through 2026, the role of the security leader has shifted from being a "gatekeeper" to becoming a strateg
Read MoreWednesday, May 20, 2026
Kubernetes Security Checklist 2026: Hardening EKS, AKS & GKE
The 2026 K8s Threat Landscape Kubernetes has become the backbone of modern cloud infrastructure, and attackers know
Read More